🐍 Cobra RAT 2026: The Ultimate Guide to Android Malware & Crypto Theft
🔍 🚀 Introduction of Cobra RAT 2026
The mobile cybersecurity landscape has changed dramatically in recent years. With the rise of mobile banking, digital wallets, and cryptocurrency trading across the United States and Europe, cybercriminals are shifting their focus toward smartphones. One of the most alarming threats in 2026 is Cobra RAT 2026, a highly advanced Android Remote Access Trojan (RAT).
Unlike traditional malware, this threat is designed not just to disrupt devices—but to silently steal money, monitor activity, and maintain long-term control. It combines social engineering, stealth techniques, and financial exploitation into one powerful attack system.
Understanding how Cobra RAT works is essential for anyone who uses an Android device for banking, communication, or crypto transactions.
📱 🧪 APK Dropper: The Hidden Entry Point in Cobra RAT 2026
The infection process typically begins with a malicious APK file that tricks users into installing it manually.
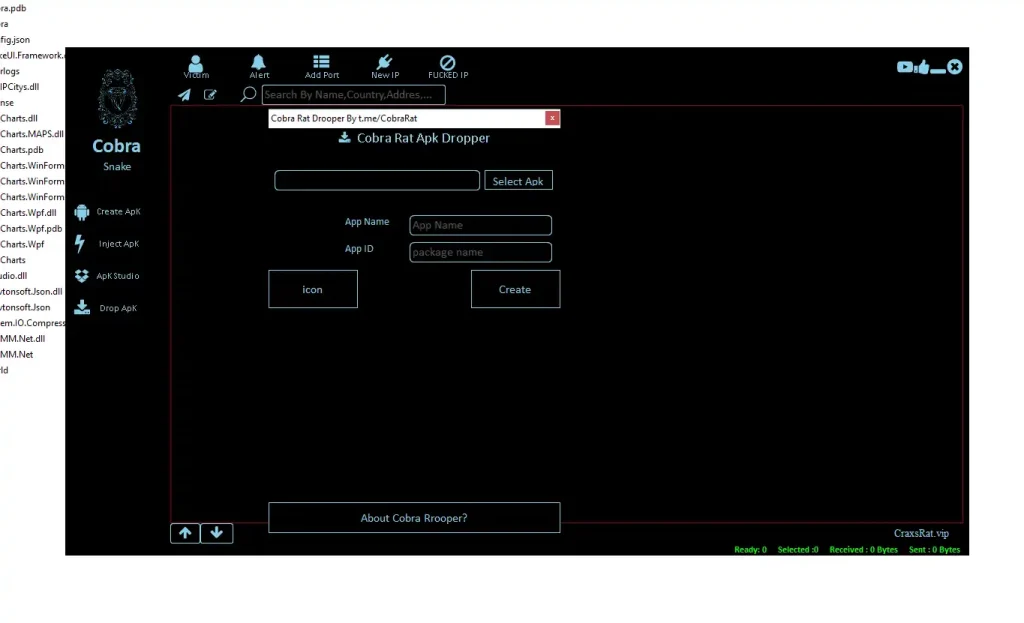
🔹 Key Attack Mechanisms:
- 🧩 Icon Cloning Technique:
Attackers design fake applications that look identical to trusted apps such as banking platforms, payment apps, or popular games. The logo, app name, and interface are carefully copied to create familiarity and trust. Many users fail to notice subtle differences, especially when downloading apps from unofficial sources. This deception increases the chances of installation significantly. In real-world scenarios, users often install such apps during urgency—like accessing their bank quickly. Once installed, the fake app behaves normally on the surface but hides malicious processes underneath. This psychological manipulation is one of the most effective entry strategies used by modern malware developers. - ⚙️ Silent Payload Installation:
After installation, the APK dropper quietly deploys the malicious payload in the background. There are no warning messages or visible signs of suspicious activity. This ensures that the victim remains unaware while the malware establishes control. The payload may include spyware, keyloggers, or crypto-stealing modules. Since everything happens silently, traditional detection methods often fail. This stealth approach allows attackers to gain a strong foothold early. By the time users notice unusual behavior, the damage is often already done. Silent installation is a core feature that makes Cobra RAT extremely dangerous.
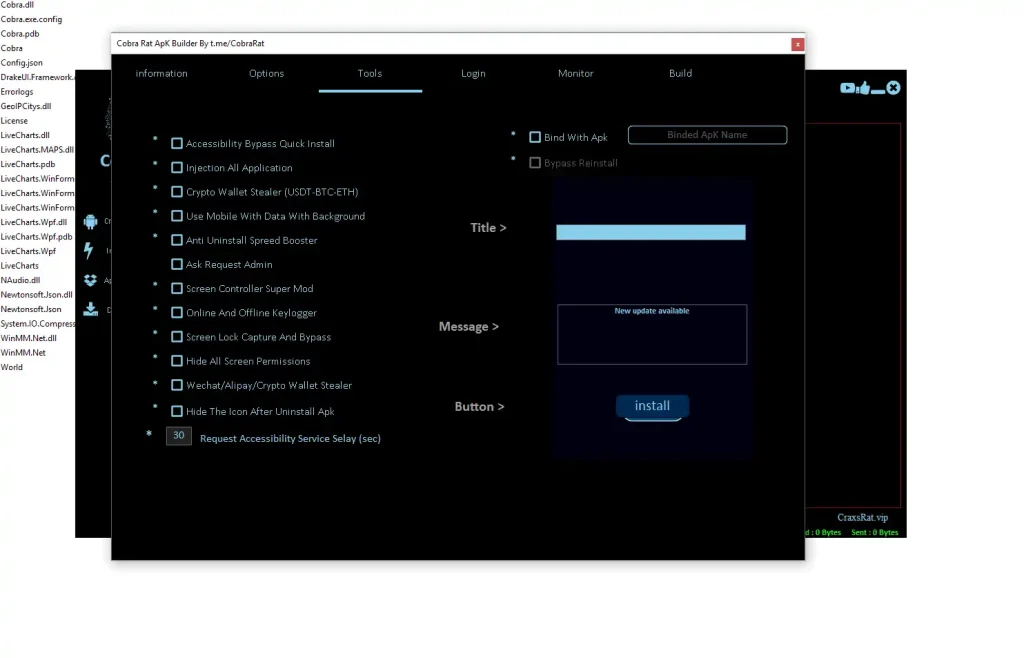
🛠️ 🧬 Cobra RAT 2026 Malware Development Toolkit (APK Studio)
Cobra RAT includes a powerful backend toolkit that allows attackers to create customized malicious apps.
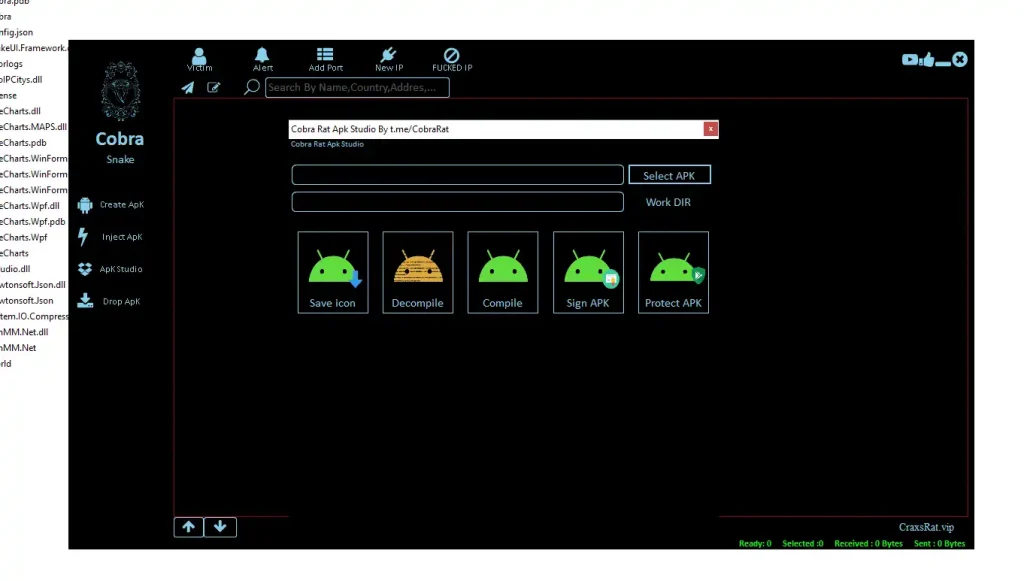
🔹 Core Capabilities:
- 🔧 APK Repackaging & Injection:
Cybercriminals take legitimate Android apps and inject malicious code into them. The modified app still works as expected, which reduces suspicion. Users continue using the app normally, unaware that their data is being monitored. This method is particularly effective because it bypasses user skepticism. It also allows malware to spread faster, especially through file-sharing platforms. The injected code runs in the background and communicates with attacker-controlled servers. This technique turns trusted apps into dangerous carriers. It’s one of the most widely used methods in modern Android malware campaigns. - 🔐 Code Obfuscation & Anti-Analysis:
To avoid detection, the malware uses advanced techniques to hide its internal structure. Security tools and researchers struggle to analyze such code because it appears scrambled or encrypted. Anti-debugging mechanisms prevent experts from studying the malware behavior in controlled environments. This increases the lifespan of the malware in real-world attacks. Even if detected, understanding how it works becomes difficult. These techniques make Cobra RAT more resilient and harder to eliminate. It reflects the growing sophistication of cyber threats targeting mobile users.
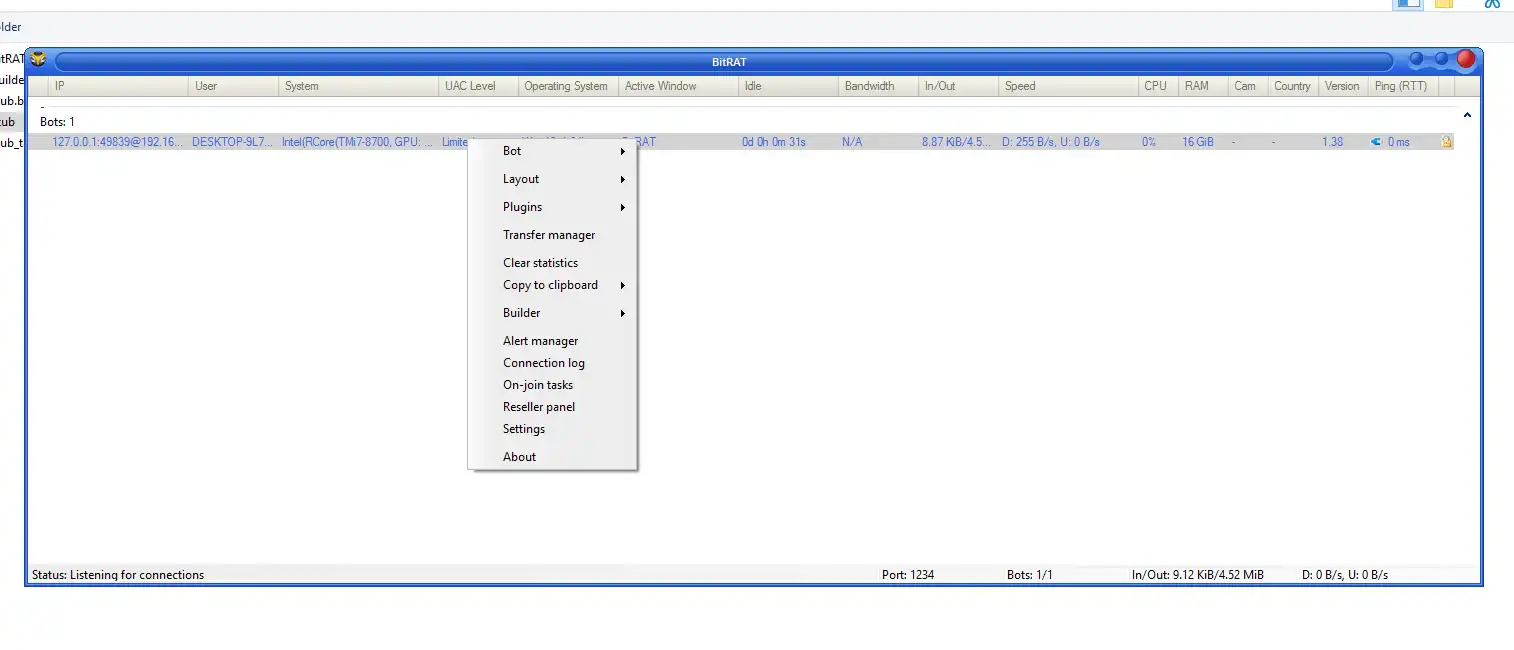
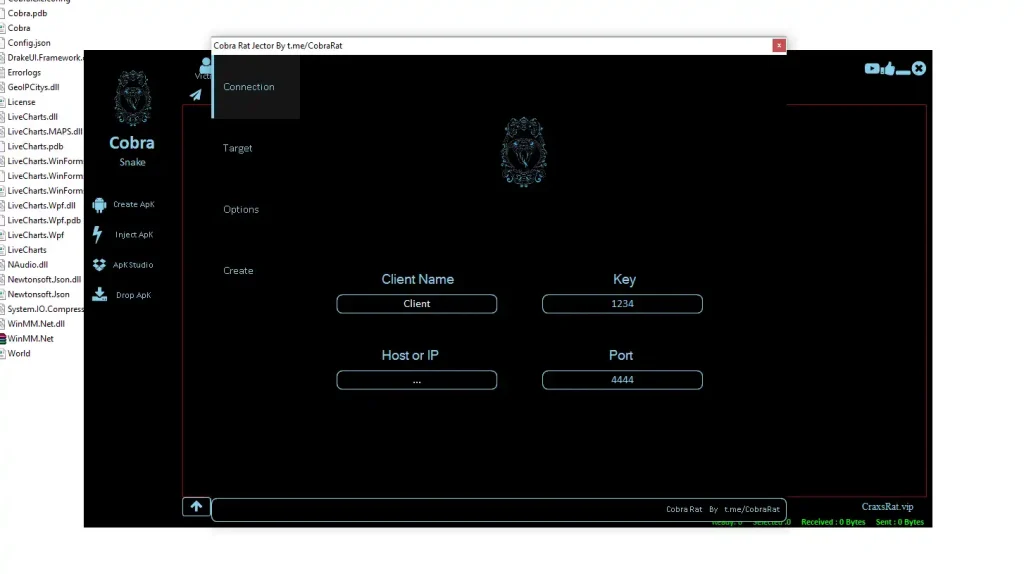
⚙️ 🧠 Builder Panel: Custom Attack Configuration in Cobra RAT 2026
The Builder Panel allows attackers to fine-tune how the malware behaves on infected devices.
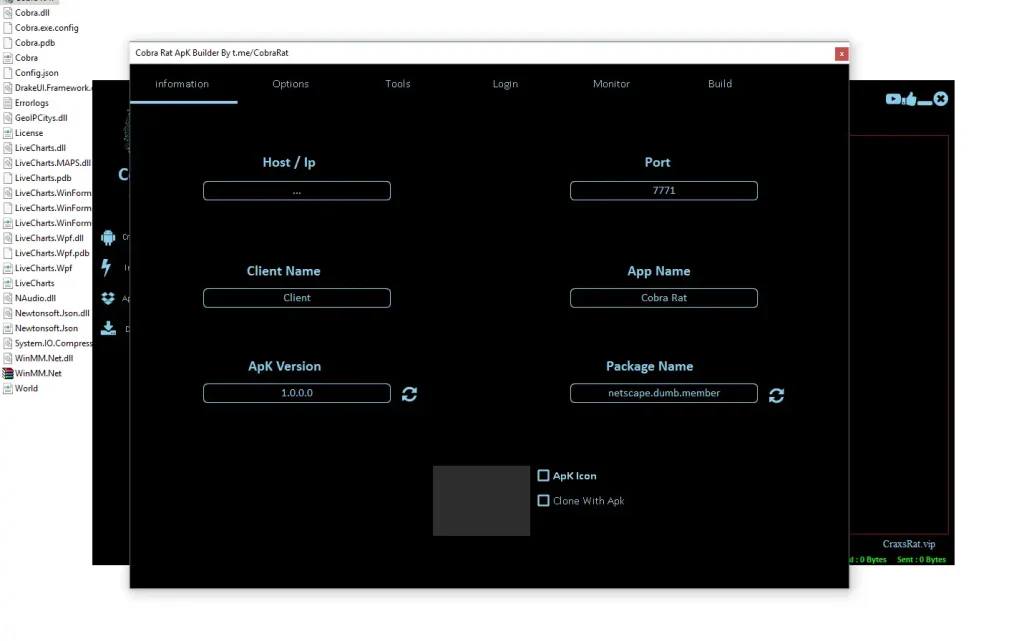
🔹 Configuration Features of Cobra RAT 2026:
- 🌐 Command & Control (C2) Integration:
The attacker connects infected devices to a remote server that acts as the control center. Through this server, commands are sent and data is received in real time. This enables full remote access to the victim’s device from anywhere in the world. The attacker can monitor activities, extract files, or execute commands instantly. This constant communication ensures ongoing control. It also allows attackers to update malware features dynamically. The C2 infrastructure is the backbone of the entire attack system.
- 💾 Persistence Mechanisms:
Cobra RAT is designed to survive even after users attempt to remove it. It may hide within system processes or reinstall itself automatically. This makes it extremely difficult for average users to eliminate the threat. Persistence ensures long-term access to sensitive data. Attackers can continue spying or stealing information over extended periods. This increases the overall impact of the attack. In many cases, only advanced troubleshooting or a factory reset can fully remove the malware.
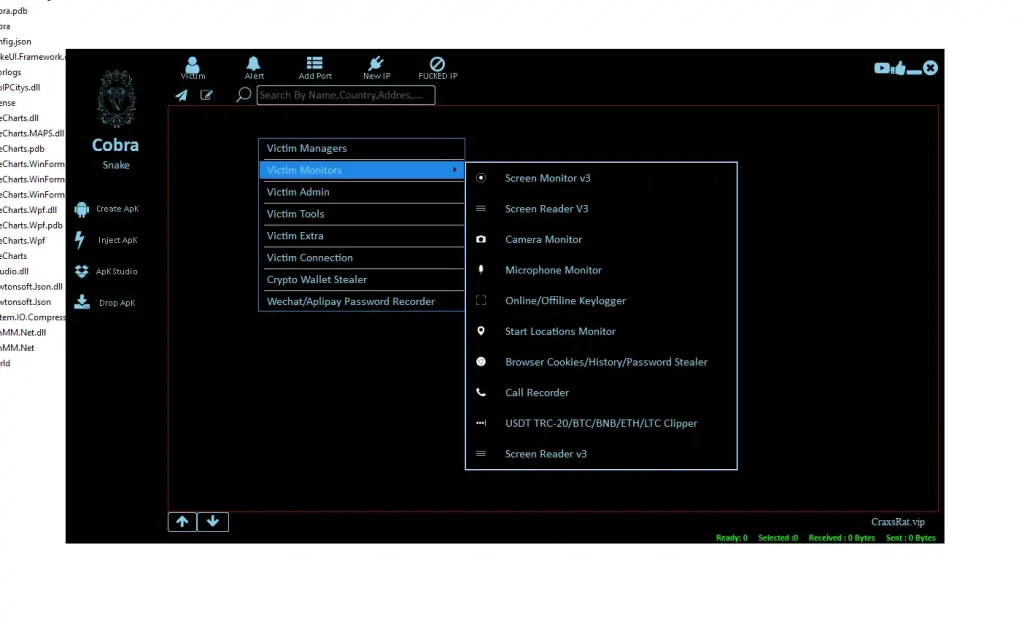
💰 🔐 Crypto Theft Engine: Targeting Digital Assets
One of the primary goals of Cobra RAT 2026 is to steal cryptocurrency from unsuspecting users.
🔹 Financial Exploitation Techniques:
- 📋 Clipboard Hijacking (Clipper Attack):
Cobra RAT 2026 constantly monitors clipboard activity on the device. When a user copies a cryptocurrency wallet address, the malware instantly replaces it with the attacker’s address. This happens so quickly that most users never notice the change. As a result, funds are unknowingly sent to the attacker. This method is extremely effective because it does not require direct hacking of the wallet. It exploits user behavior instead. Clipboard hijacking is widely used in crypto-related malware. It’s simple, stealthy, and highly profitable for attackers. - 📱 Wallet Detection & Credential Theft:
Cobra RAT 2026 scans the device for installed cryptocurrency apps. Once identified, it attempts to extract sensitive information such as login credentials, private keys, or recovery phrases. This data is then transmitted to the attacker’s server. With this information, attackers can gain full access to the victim’s funds. This makes it one of the most dangerous aspects of the malware. Unlike traditional theft, crypto transactions are irreversible. Once stolen, funds are nearly impossible to recover. This highlights the importance of securing digital wallets.
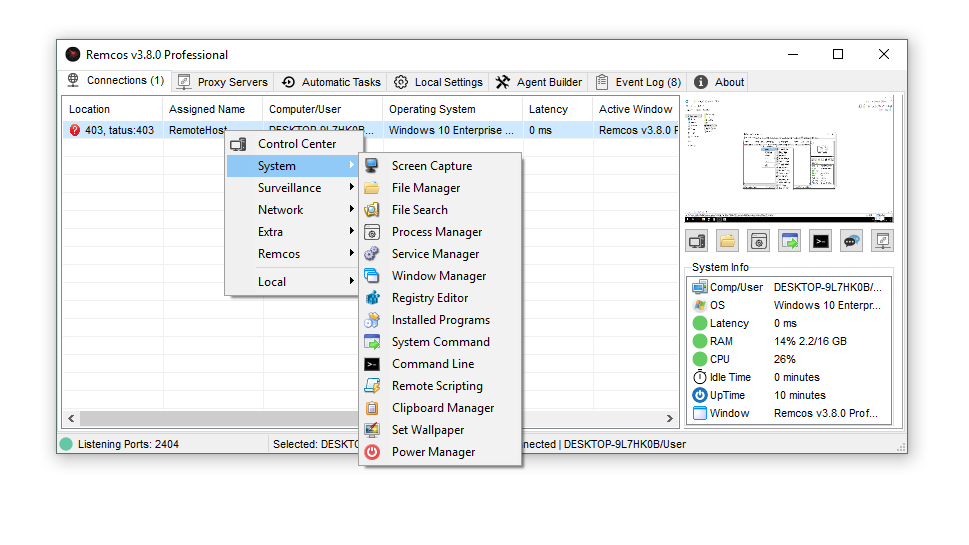
🔓 ⚠️ Accessibility Exploitation: Total Device Control
Cobra RAT 2026 abuses Android accessibility services to gain powerful permissions.
🔹 Dangerous Capabilities:
- 👁️ Screen Monitoring & Remote Interaction:
Cobra RAT 2026 can view everything displayed on the screen in real time. It can also simulate touches, typing, and gestures. This allows it to bypass security measures such as PIN codes or authentication prompts. Essentially, the attacker can control the device as if they were holding it. This level of access compromises all personal and financial data. It also enables unauthorized transactions or actions. Screen monitoring is a critical component of advanced spyware systems. - 🔒 Administrator Privileges Abuse:
By gaining admin-level permissions, the malware prevents users from uninstalling it easily. It can lock the device, change settings, or restrict access to security features. This ensures that the malware remains active for as long as possible. Users often struggle to remove such threats without technical knowledge. This increases frustration and damage potential. Admin abuse is a key reason why advanced malware persists on devices for long periods.
🔁 🧪 Injection Engine: Stealth Persistence
🔹 Advanced Injection Strategy in Cobra RAT 2026:
- 🧬 Live App Injection:
Instead of relying only on new installations, Cobra RAT injects itself into already installed apps. This makes it extremely difficult to detect. Users continue using their favorite apps without noticing any issues. Meanwhile, the malware operates silently in the background. This reduces suspicion and increases survival time. It also avoids triggering security alerts. Injection techniques represent a new level of stealth in mobile malware evolution.
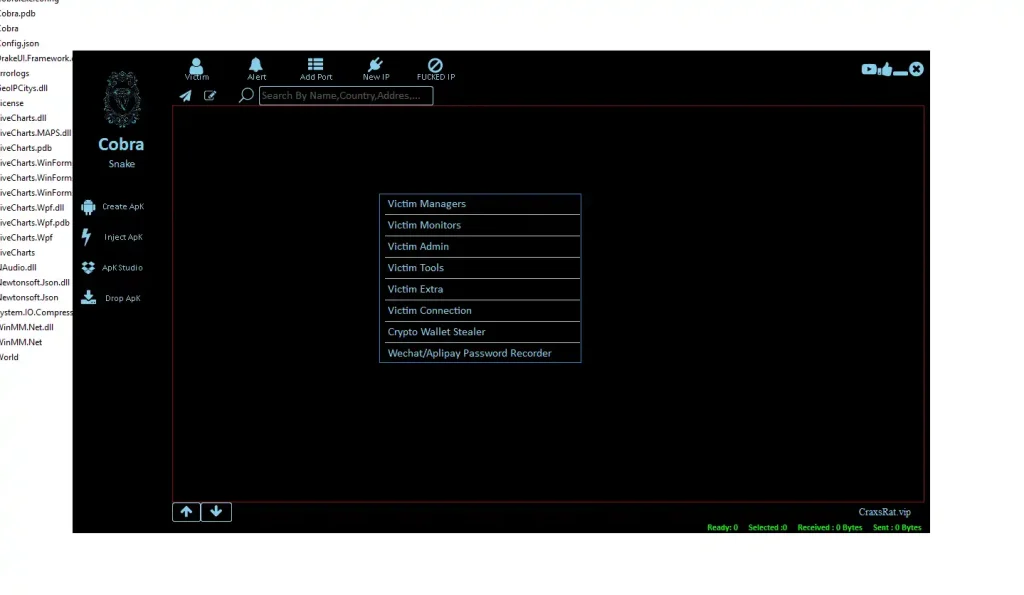
📊 📡 Victim Monitoring System
🔹 Surveillance Features of Cobra RAT 2026:
- 🎥 Camera & Microphone Surveillance:
Attackers can remotely activate the device’s camera and microphone. This allows real-time spying without user knowledge. Conversations, surroundings, and private moments can be recorded. This creates serious privacy and security risks. In extreme cases, such data can be used for blackmail. Surveillance capabilities extend the threat beyond financial loss. It becomes a complete invasion of personal privacy.
🛡️ 🧠 Cybersecurity Protection Guide Cobra RAT 2026
🔹 How to Stay Safe:
- 🚫 Avoid Installing APKs from Unknown Sources:
One of the most effective ways to stay safe is to avoid downloading apps outside official app stores. Unofficial APK files often bypass security checks and may contain hidden malware. Even if the app looks legitimate, it could be repackaged with malicious code. Always verify the source before installing any application. Trusted platforms implement strict security policies. This simple habit can prevent most infections. It is the first line of defense against mobile threats. - 🔍 Carefully Review App Permissions:
Before installing any app, take time to review the permissions it requests. If an app asks for access that doesn’t match its purpose, consider it a red flag. For example, a simple calculator should not need accessibility or microphone access. Granting unnecessary permissions can expose your device to control and surveillance. Understanding permissions helps you make informed decisions. It significantly reduces the risk of malware infection.
Download Cobra RAT 2026
🏁 📌 Conclusion: The Future of Mobile Cyber Threats
Cobra RAT 2026 represents a new generation of mobile malware focused on financial gain, stealth, and long-term control. It highlights how cybercriminals are evolving alongside technology, targeting users where they are most vulnerable—on their smartphones.
For users in the US and Europe, where digital payments and cryptocurrency are widely used, awareness and proactive security measures are essential. Staying informed is no longer optional—it is a necessity.
❓ FAQs
❓ What is Cobra RAT 2026 and why is it dangerous?
Cobra RAT 2026 is an advanced Android malware that allows attackers to control devices remotely, steal sensitive data, and target cryptocurrency wallets, making it highly dangerous.
❓ How does Cobra RAT infect Android devices?
It typically spreads through malicious APK files disguised as legitimate apps, often downloaded from unofficial sources or phishing campaigns.
❓ Can Cobra RAT steal cryptocurrency safely without detection?
Yes, it uses techniques like clipboard hijacking and credential extraction, which often go unnoticed by users during transactions.
❓ How can I remove Cobra RAT from my device?
You can remove it by uninstalling suspicious apps, revoking permissions, using security tools, or performing a factory reset if necessary.
❓ Does Cobra RAT affect iPhones or only Android devices?
Cobra RAT primarily targets Android devices because of APK-based installations and Android’s flexible permission system.
❓ What are the early signs of infection?
Unusual battery drain, unknown apps, unexpected permissions, and strange device behavior may indicate infection.
❓ Is mobile antivirus enough to stop such threats?
While helpful, antivirus alone is not enough. Safe browsing habits and avoiding untrusted apps are equally important.
❓ How can I protect my crypto wallet from such attacks?
Use hardware wallets, verify wallet addresses before transactions, and avoid copying sensitive data on compromised devices.