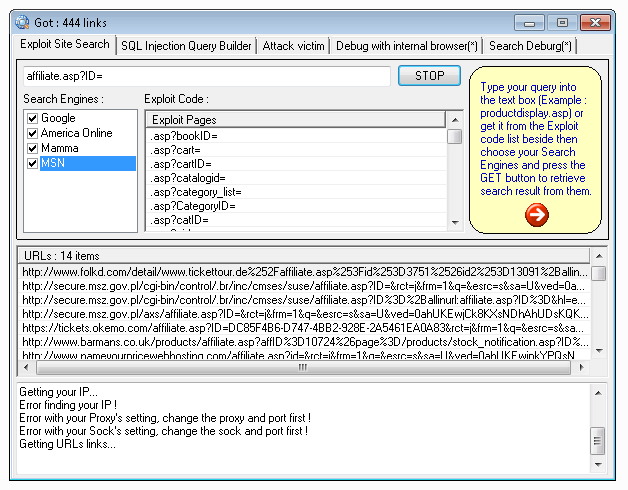
Google URL Extractor 2025
Google URL Extractor 2025 very powerfulll scanning for all kind of server
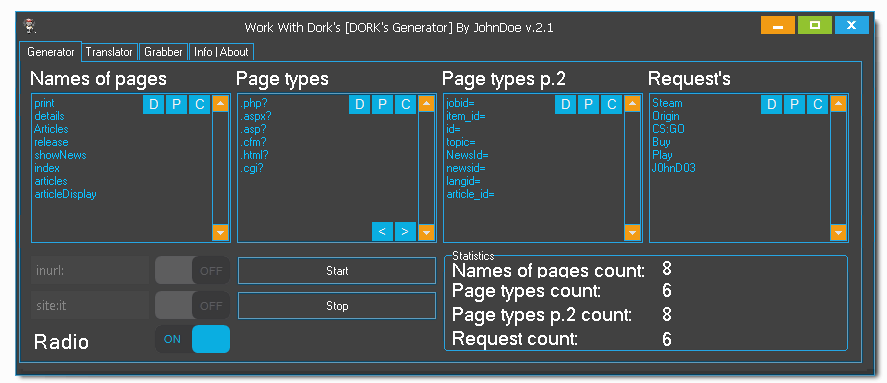
Work With Dorks 2025
Work With Dorks 2025 [DORK’s Generator]-Dork Generator
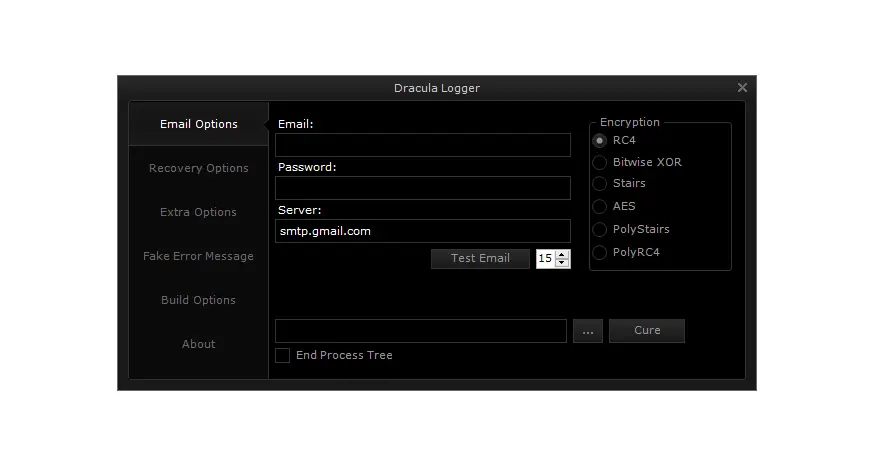
XSS Exploitation Tool 2025
XSS Exploitation Tool 2025 The XSS Exploitation Tool 2025 by Sharpforce, hosted on GitHub, is a powerful penetration testing utility designed to explore and…
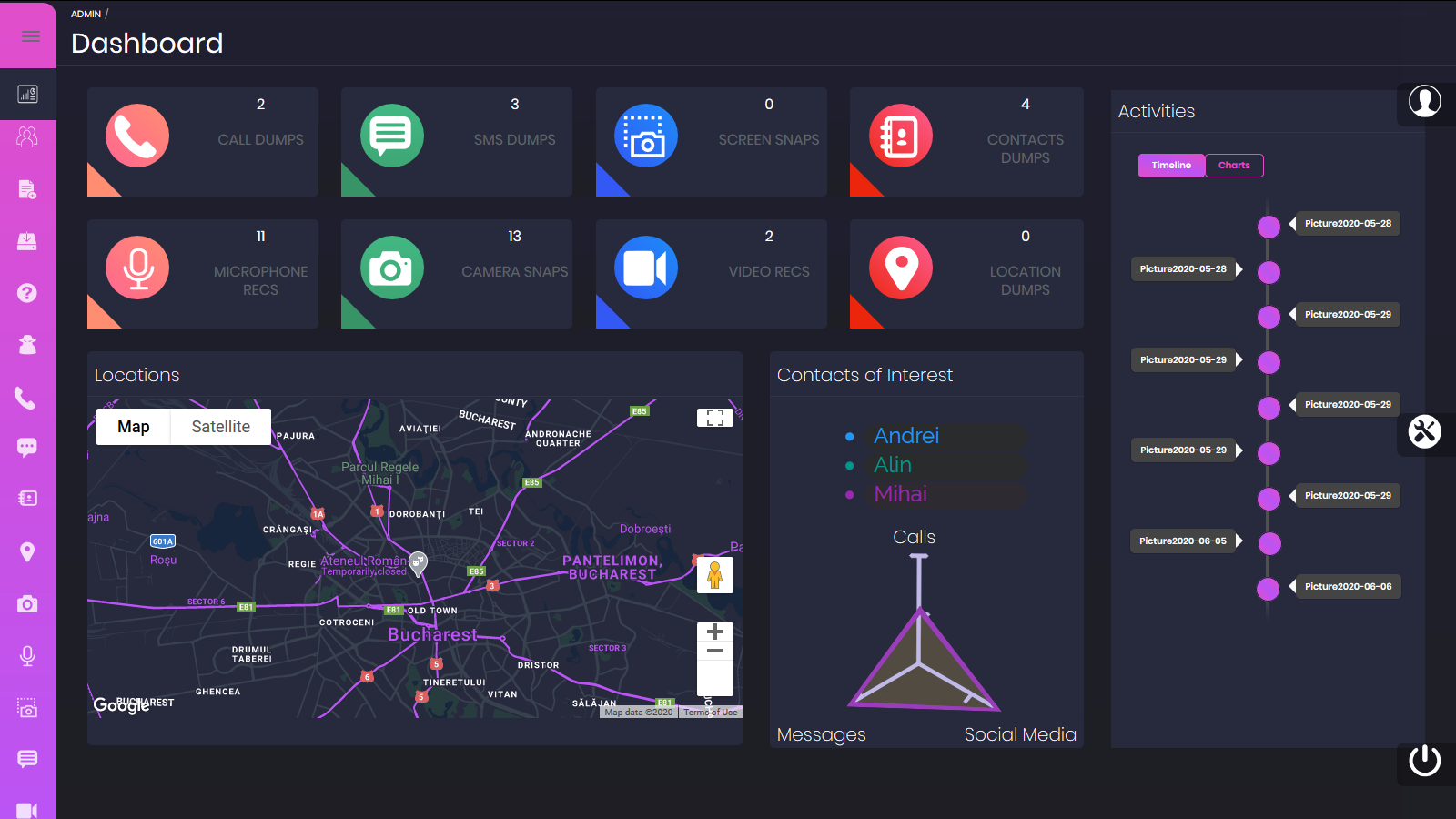
no1se Andro RAT 2025
no1se Andro RAT 2025 In the realm of cybersecurity and mobile device management, remote access tools (RATs) play a pivotal role for developers and…
Roundcube Webmail Sorter V 2.0
Roundcube Webmail Sorter V 2.0 Roundcube Webmail Sorter v2.0: Fast & Accurate Sorting for RedWebmail, BlueWebmail & Other Roundcube-Based Emails In the world of…
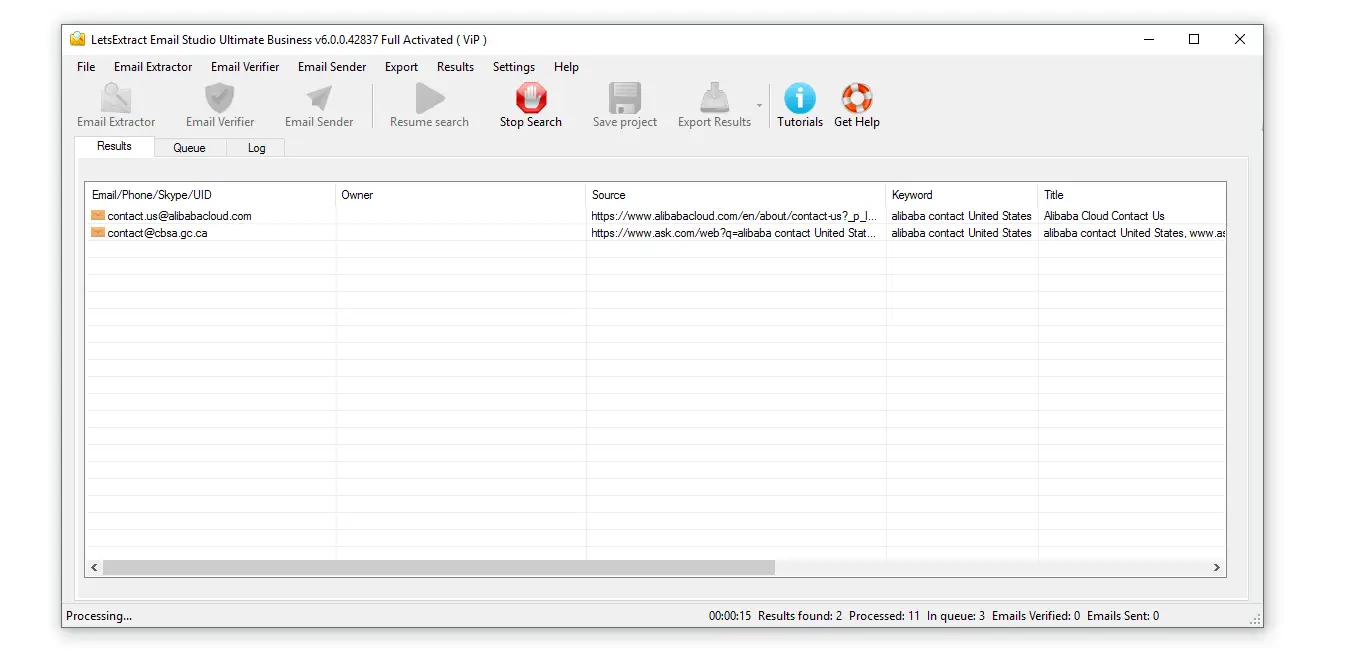
LetsExtract Email Studio Business 2025
LetsExtract Email Studio Business 2025 LetsExtract Email Studio Business 2025: The Ultimate All-in-One Email Marketing Solution for Growing Businesses In the fast-paced world of…
Fox RAT V 6.0
Fox RAT V 6.0 Fox RAT v6.0: Android-Based Remote Access Trojan Fox RAT v6.0 is a sophisticated Android malware designed for unauthorized remote surveillance…
Doofi Stealer 2025
Doofi Stealer 2025 Doofi Stealer 2025: Advanced FUD Python Stealer for Discord Integration and Chrome V20 Compatibility In the evolving landscape of cybersecurity tools…