🔥 Dystopia C2 2026 Framework – Complete Guide for Ethical Hackers & Red Teams
🧠 Introduction to Dystopia C2
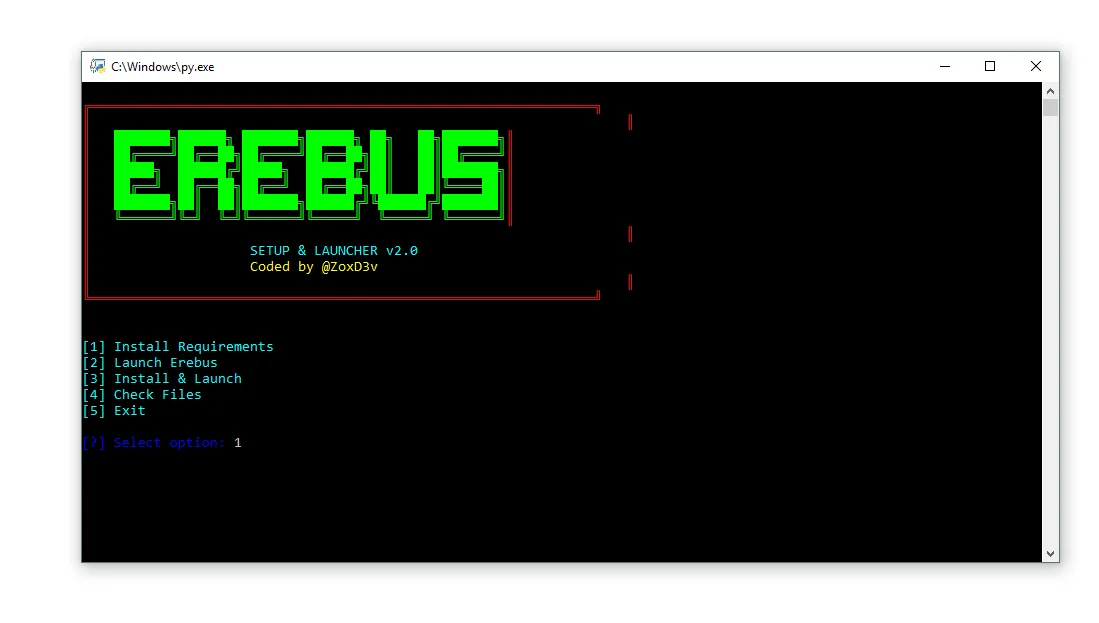
Dystopia C2 2026 is a modern open-source Command-and-Control (C2) framework designed for cybersecurity professionals, penetration testers, and red team operators. It enables centralized control of multiple remote systems through secure communication channels.
This framework is widely used in ethical hacking environments to simulate real-world cyber attack scenarios and evaluate system defenses.
⚙️ 🚀 Key Features of Dystopia C2
🖥️ 🔹 Centralized Remote Control
- ⚡ Execute commands across multiple systems simultaneously
- 🧑💻 Real-time remote shell access
- 🔄 Fast and reliable communication
📂 🔹 File Management System
- 📤 Upload files remotely
- 📥 Download system data
- 🗂️ Full file control and management
📸 🔹 Monitoring & Surveillance
- 📷 Capture webcam snapshots
- 👁️ Monitor system activity
- 🔍 Ideal for controlled testing environments
🧩 🔹 Modular & Customizable
- 🧱 Extend with custom modules
- ⚙️ Build and deploy payloads
- 🛠️ Flexible for advanced operations
🌐 🔹 Cross-Platform Support
- 💻 Works on Windows & Linux
- 🔗 Easy deployment across environments
🛠️ ⚡ How Dystopia C2 Works
Dystopia C2 2026 uses a structured architecture:
🧠 1. Command Server (C2 Panel)
- Central control system
- Sends commands and receives responses
🤖 2. Client/Agent (Payload)
- Installed on target machines
- Executes instructions from server
🔗 3. Communication Channel
- Secure data transmission
- Maintains connection between server and clients
🎯 🚀 Use Cases of Dystopia C2
✅ Ethical Uses
- 🔐 Penetration testing
- 🛡️ Red team simulations
- 🎓 Cybersecurity training
- 🧪 Malware research labs
⚠️ Misuse Warning
- 🚫 Unauthorized use is illegal
- ⚖️ Always operate in controlled environments
- 🔒 Follow ethical hacking standards
📊 ⭐ Advantages of Dystopia C2
- ✅ Open-source and flexible
- ✅ Lightweight performance
- ✅ Highly customizable
- ✅ Suitable for advanced security operations
❌ ⚠️ Limitations
- ❗ Requires technical expertise
- ❗ May be detected by security software
- ❗ Complex setup for beginners
- ❗ Needs proper configuration
🔐 🛡️ Security & Legal Considerations
When using Dystopia C2 2026, keep in mind:
- ✔️ Only test on authorized systems
- ✔️ Always have permission
- ✔️ Avoid illegal deployment
- ✔️ Follow cybersecurity laws and ethics
Download Dystopia C2
🏁 ✅ Conclusion
Dystopia C2 stands out as a powerful and flexible framework built for modern cybersecurity professionals. Its modular design and remote management capabilities make it highly valuable for ethical hacking and testing environments.
However, due to its advanced capabilities, it must always be used responsibly, ethically, and legally.
❓ FAQs
❓ What is Dystopia C2 2026?
Dystopia C2 2026 is an open-source command-and-control framework used for managing remote systems in cybersecurity testing.
❓ Is Dystopia C2 2026 legal?
Yes, it is legal when used for authorized and ethical purposes only.
❓ Who should use Dystopia C2 2026?
It is ideal for ethical hackers, penetration testers, and red team professionals.
❓ Does Dystopia C2 2026 support multiple platforms?
Yes, it works on Windows and Linux systems.
❓ Is Dystopia C2 2026 beginner-friendly?
No, it requires intermediate to advanced technical knowledge.