🧠 Introduction
The rise of Eclipse RAT 2026 Cracked has become a major concern in the cybersecurity world. Originally developed as a premium remote administration tool, its cracked version has made powerful capabilities accessible to a much wider audience.
This unauthorized distribution has significantly increased the risk level, as even low-skilled individuals can now deploy advanced malware. In this article, we provide a complete and structured analysis of Eclipse RAT 2026 Cracked, including its builder system, command dashboard, monetization features, and potential threats.
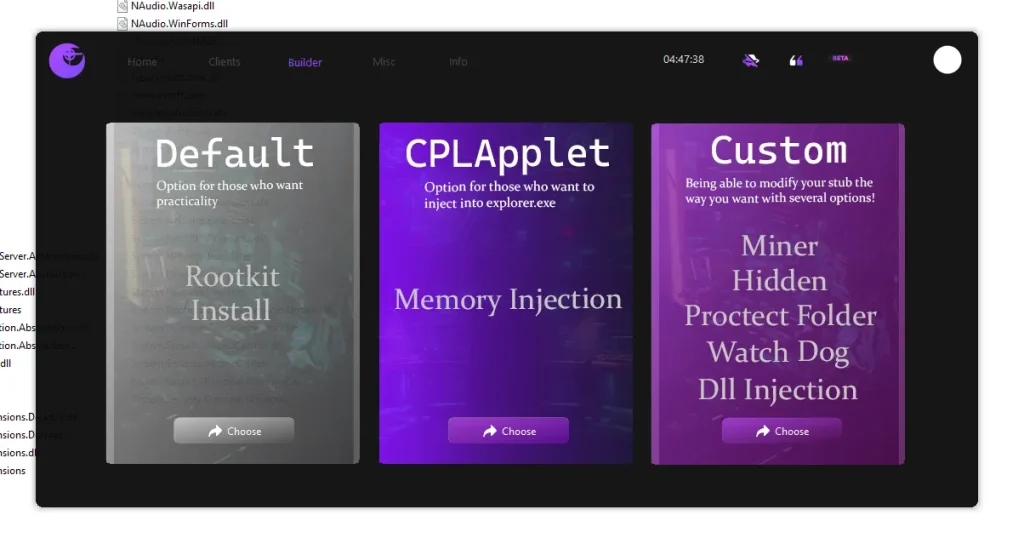
⚙️ Builder System: How Eclipse RAT 2026 Cracked Creates Payloads
The builder is the core component of Eclipse RAT 2026 Cracked, allowing users to generate customized malicious files. It offers multiple modes, each designed for different use cases.
🔹 🧩 Default Mode – Simple & Fast Deployment
- 🚀 Generates a basic executable quickly
- ⚡ Minimal configuration required
- 📉 Limited stealth capabilities
👉 Detailed Explanation:
Default mode is ideal for quick deployment scenarios where speed matters more than sophistication. However, due to its lack of advanced obfuscation techniques, it is more likely to be detected by modern antivirus and endpoint security solutions.
🔹 🧬 CPL Applet Mode – Stealth-Based Execution
- 🛠️ Uses Control Panel applet technique
- 🖥️ Injects into trusted processes like explorer.exe
- 🕵️ Enhances stealth and persistence
👉 Detailed Explanation:
This mode leverages legitimate Windows components to disguise malicious activity. By injecting into trusted system processes, Eclipse RAT avoids raising suspicion and can bypass weaker security defenses.
🔹 🔥 Custom Mode – Advanced Control & Flexibility
- 🎯 Full customization of payload
- 🔒 Advanced persistence and protection
- ⚙️ Multiple stealth and injection options
📋 Advanced Features Explained

- 🧍 Hidden Execution:
Runs silently in the background without showing any visible signs. This ensures that the victim remains unaware of the infection. - 🛡️ Protection Mechanism:
Blocks attempts to remove or terminate the malware, often interfering with security tools. - 🔄 Watchdog Process:
Automatically restarts the malware if it is stopped, ensuring continuous operation. - 📂 Folder Persistence:
Installs itself in system directories so it launches automatically after reboot. - 🧪 DLL Injection:
Injects malicious code into legitimate processes, making detection extremely difficult. - ⛏️ Crypto Miner Option:
Adds a hidden mining component to generate revenue from infected systems.
👉 Detailed Explanation:
Custom mode transforms Eclipse RAT 2026 Cracked into a highly advanced cyber tool, capable of long-term persistence, stealth operation, and deep system control.
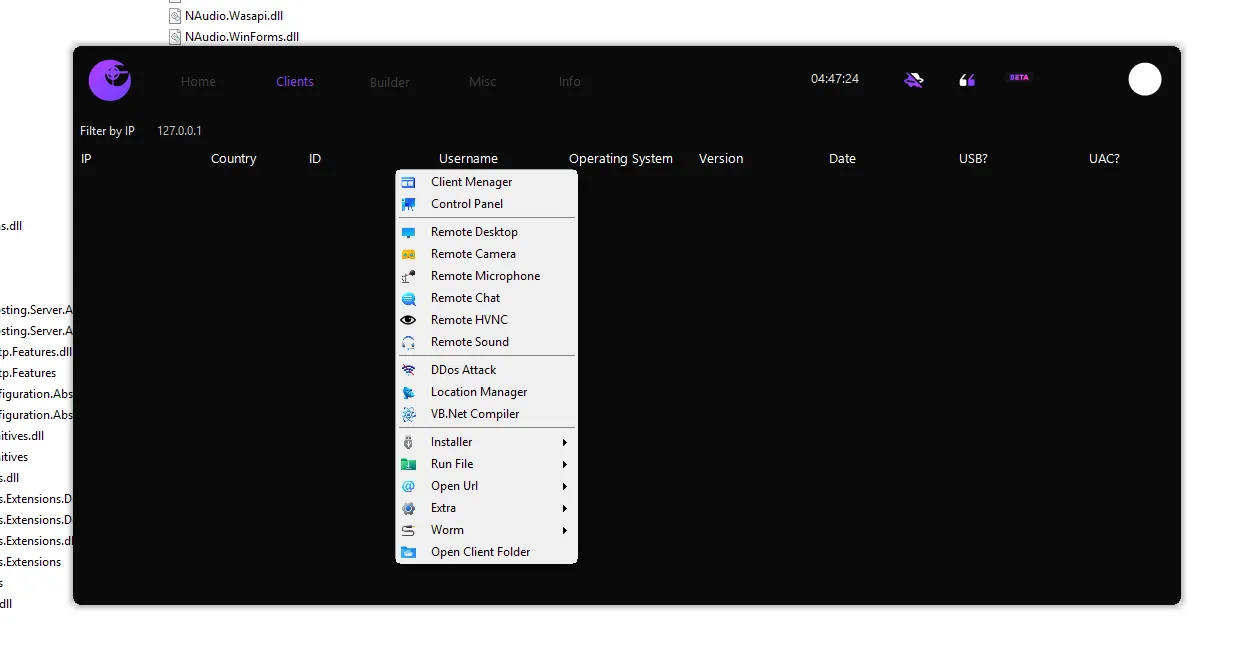
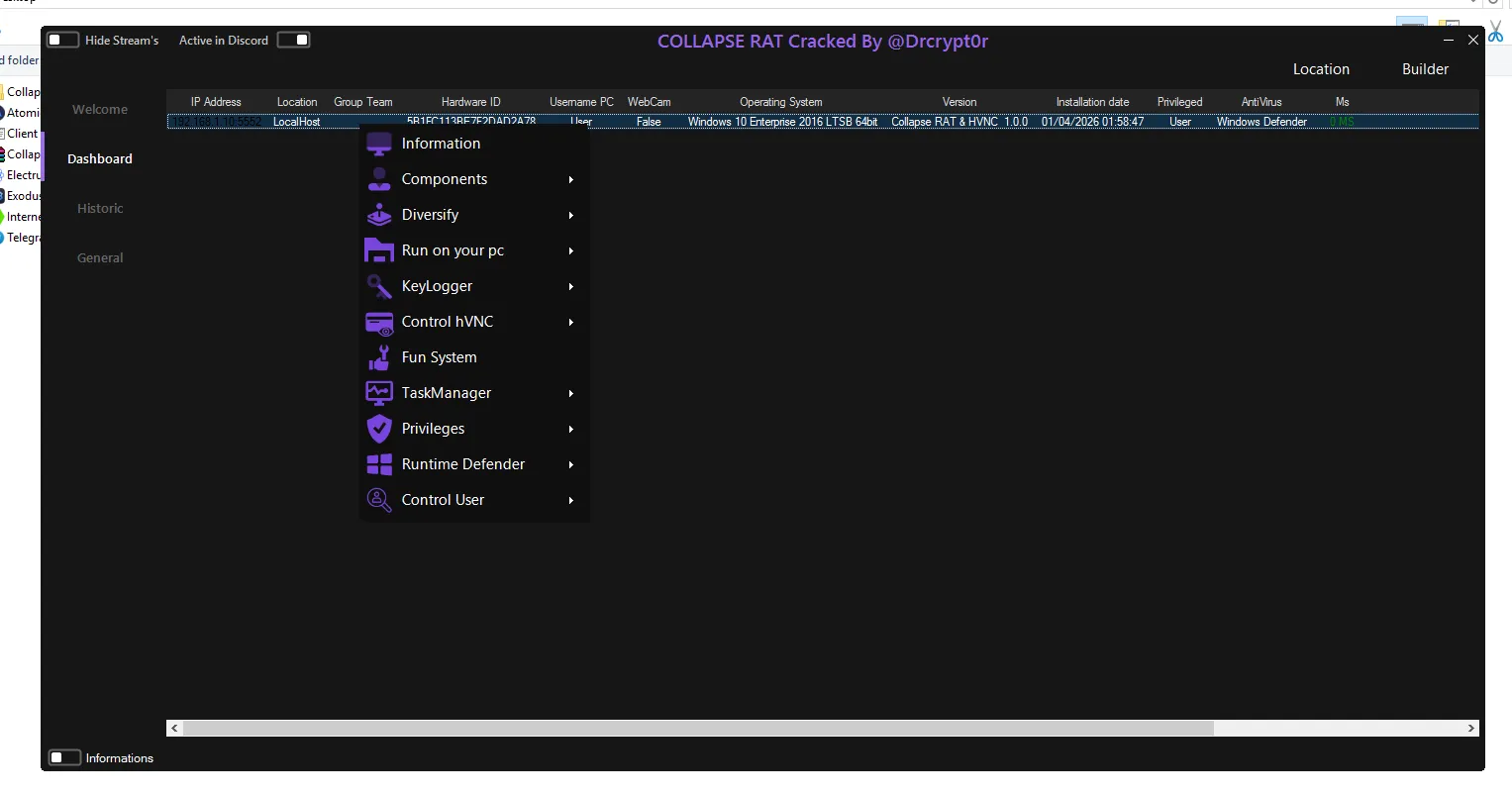
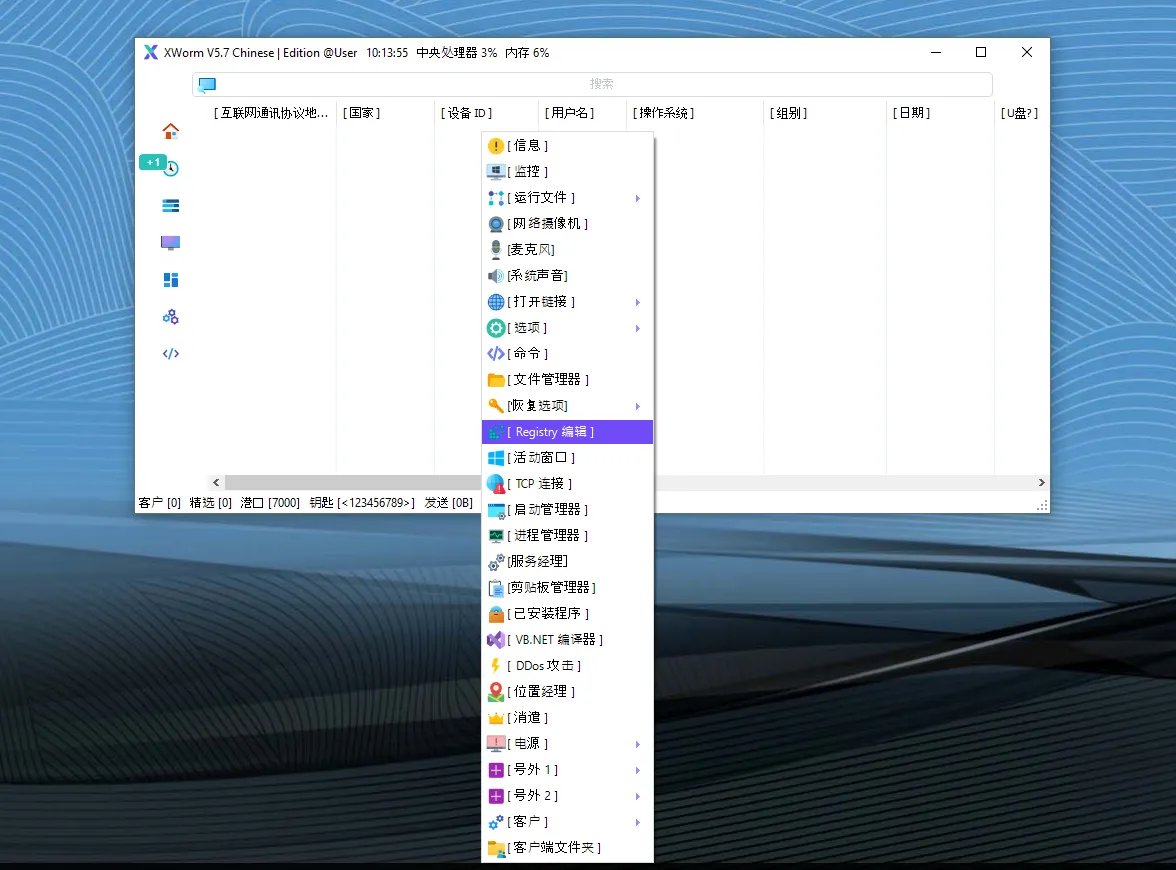
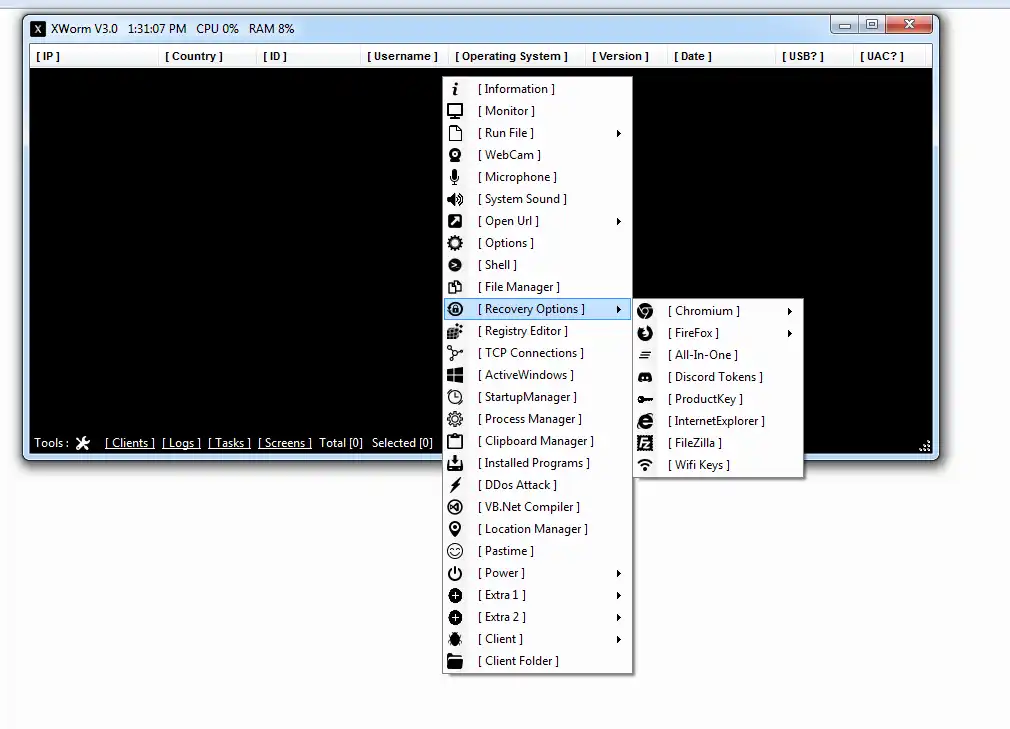
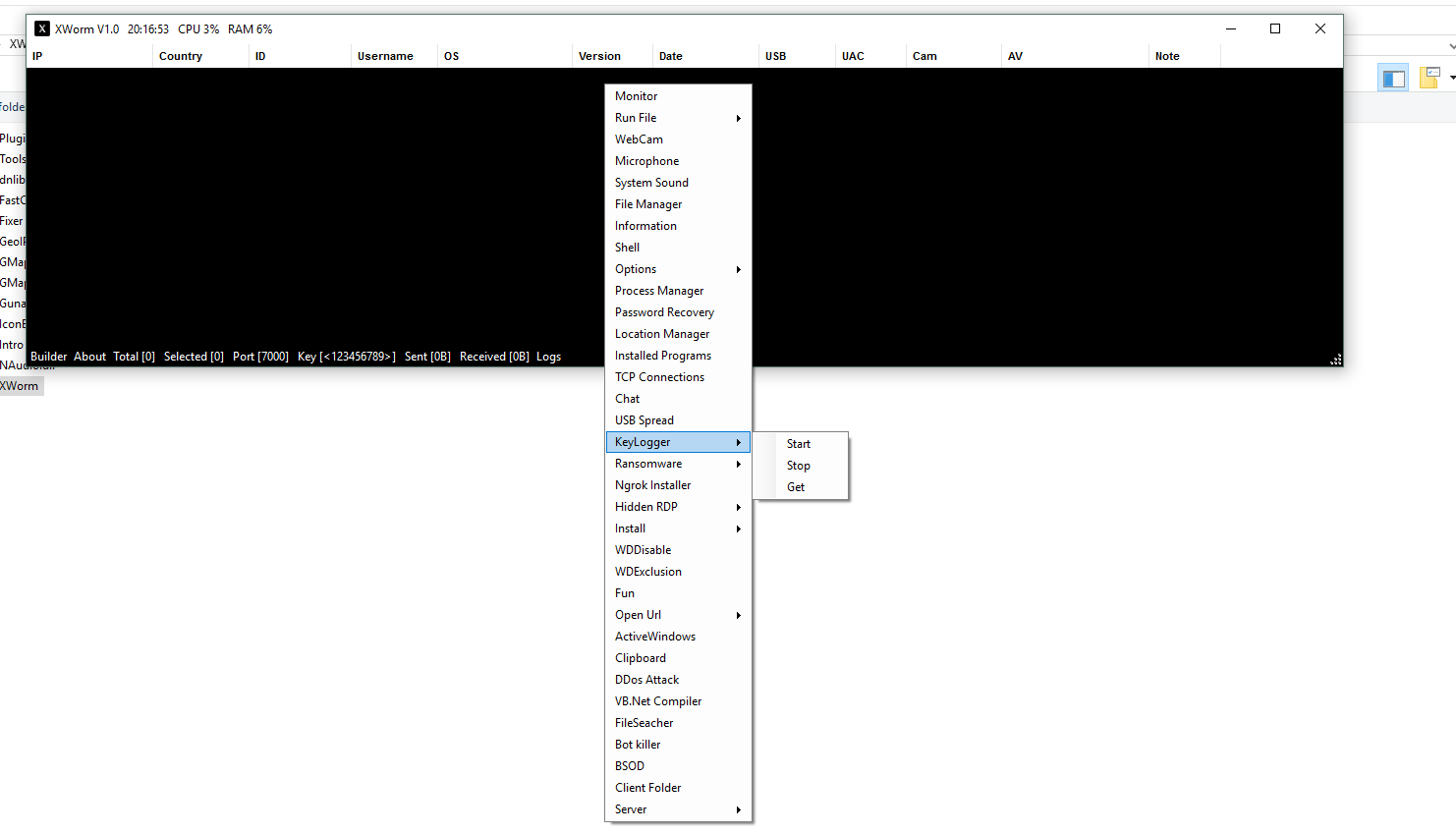
🖥️ Command & Control Dashboard
After infection, attackers manage compromised systems through a centralized control panel.
🔹 🎛️ Core Functional Modules
- 📷 Remote Camera & Microphone Access:
Allows attackers to monitor victims through webcam and microphone in real time. This poses serious privacy risks. - 🖥️ Remote Desktop Control:
Provides full visual access to the system, enabling attackers to monitor or control user activity. - 🔊 Remote Audio Control:
Attackers can listen to system sounds or send audio messages through the victim’s device. - 🌐 DDoS Attack Capability:
Turns infected machines into bots used for large-scale Distributed Denial-of-Service attacks. - 💻 VB.NET Compiler:
Enables execution of custom scripts directly on the victim’s system, increasing flexibility. - 🔁 Worm Propagation Tools:
Spreads infection via USB drives and network shares, expanding reach rapidly.
👉 Detailed Explanation:
These features make Eclipse RAT 2026 Cracked a multi-functional cyber weapon, combining surveillance, control, and attack capabilities in one platform.
💰 Built-in Cryptocurrency Mining
🔹 ⛏️ Hidden Revenue Generation
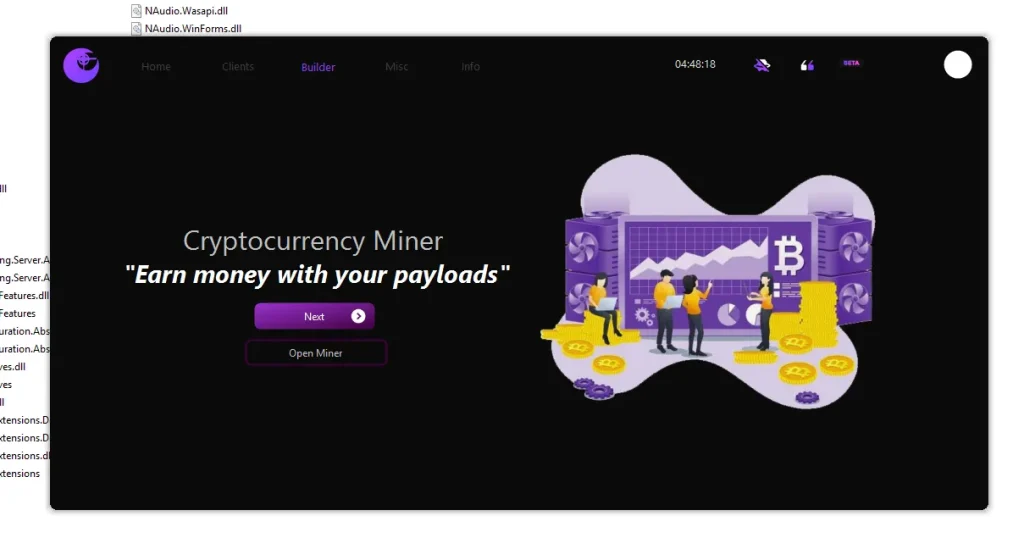
- 💸 Uses victim’s hardware resources
- 🔐 Operates silently without detection
- 🪙 Targets cryptocurrencies like Monero
👉 Detailed Explanation:
The inclusion of a crypto miner highlights the financial motivation behind modern malware. Instead of just stealing data, attackers generate continuous income by exploiting system performance.
🔐 Persistence & System Control
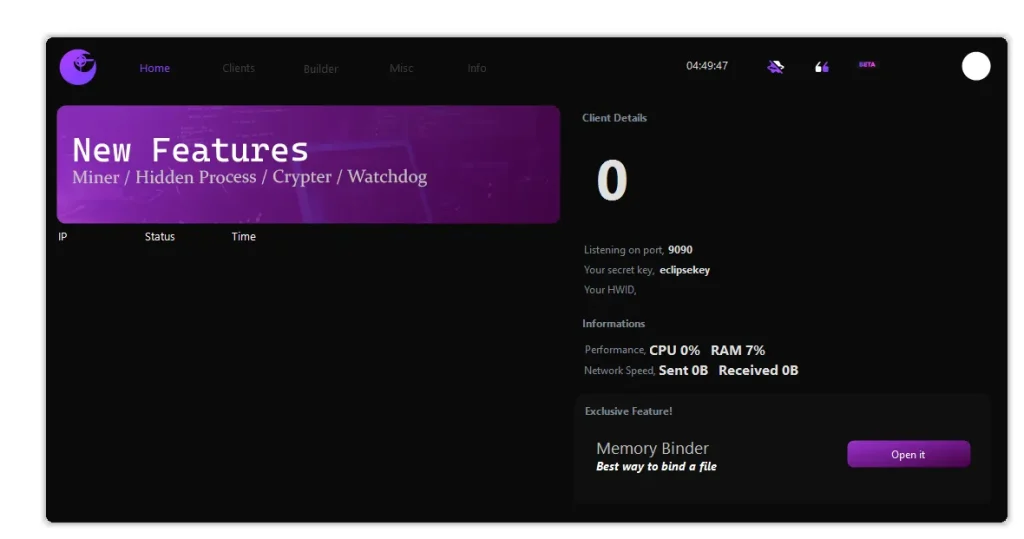
🔹 ⚡ Advanced Techniques
- 🌍 Port Communication (e.g., 9090):
Maintains stable communication between attacker and victim using secure keys. - 📊 Performance Monitoring:
Displays CPU and RAM usage for efficient management. - 🧠 Memory Binder:
Executes malware in memory instead of disk, bypassing traditional detection systems.
👉 Detailed Explanation:
These techniques ensure that Eclipse RAT remains active for long periods while minimizing detection risk.
⚠️ Risks of Eclipse RAT 2026 Cracked
- 🚨 Easy access for cybercriminals
- 📉 Increased global malware threats
- 🧑💻 Misuse by inexperienced users
- 💣 Large-scale botnet creation
👉 Detailed Explanation:
The cracked version significantly amplifies cybersecurity threats by removing access barriers and enabling widespread misuse.
Download Eclipse RAT 2026 Cracked
✅ Conclusion
Eclipse RAT 2026 Cracked represents a new generation of malware that combines control, surveillance, and monetization into one powerful tool.
Understanding its features helps:
- 🛡️ Strengthen cybersecurity defenses
- 🔍 Detect advanced threats
- 📚 Educate users about risks
Awareness is the key to prevention in today’s evolving digital threat landscape.
❓ FAQs
❓ What is Eclipse RAT 2026 Cracked?
Eclipse RAT 2026 Cracked is a remote access trojan that allows unauthorized control, monitoring, and exploitation of infected systems.
❓ Why is Eclipse RAT 2026 Cracked dangerous?
Because it provides advanced hacking features to a wide audience, increasing the risk of cyberattacks.
❓ How does Eclipse RAT spread?
It spreads through infected files, USB devices, malicious downloads, and network vulnerabilities.
❓ Can Eclipse RAT be detected?
Yes, advanced antivirus and endpoint security solutions can detect it using behavioral analysis.
❓ What does the crypto miner do?
It uses system resources to mine cryptocurrency, generating profit for attackers.
❓ How to stay safe from RAT malware?
- Avoid unknown downloads
- Use trusted antivirus software
- Keep your system updated
- Do not run unverified programs
⚠️ Disclaimer
This content is for educational and cybersecurity awareness purposes only. Unauthorized use of such tools is illegal.