🧠 Introduction
The cybersecurity landscape in 2026 has taken a dangerous turn with the rise of Icarus Evil Worm Cracked 2026. Once a premium malware toolkit reserved for skilled cybercriminals, it is now widely distributed in cracked form, removing both financial and technical barriers.
👉 As a result, cyber threats are no longer limited to advanced attackers—anyone with basic knowledge can now launch powerful attacks.
🧬 What is Icarus Evil Worm Cracked 2026?
Icarus Evil Worm Cracked 2026 is a highly advanced malware that combines the capabilities of a Remote Access Trojan (RAT) with a self-propagating worm.

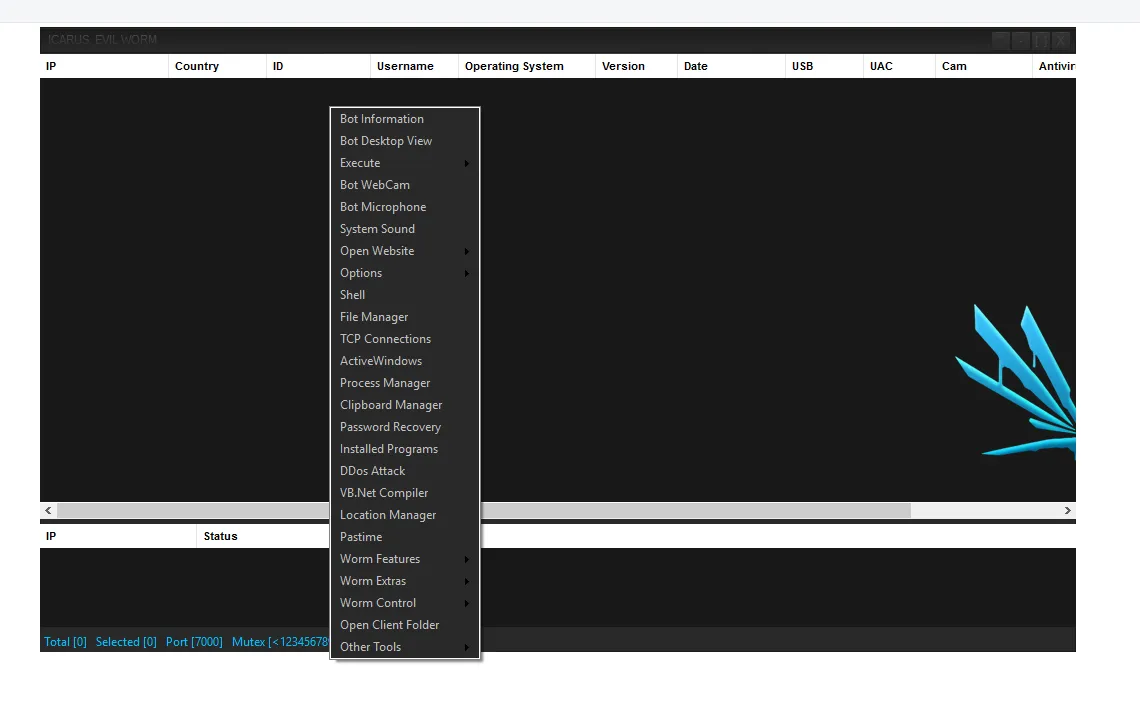
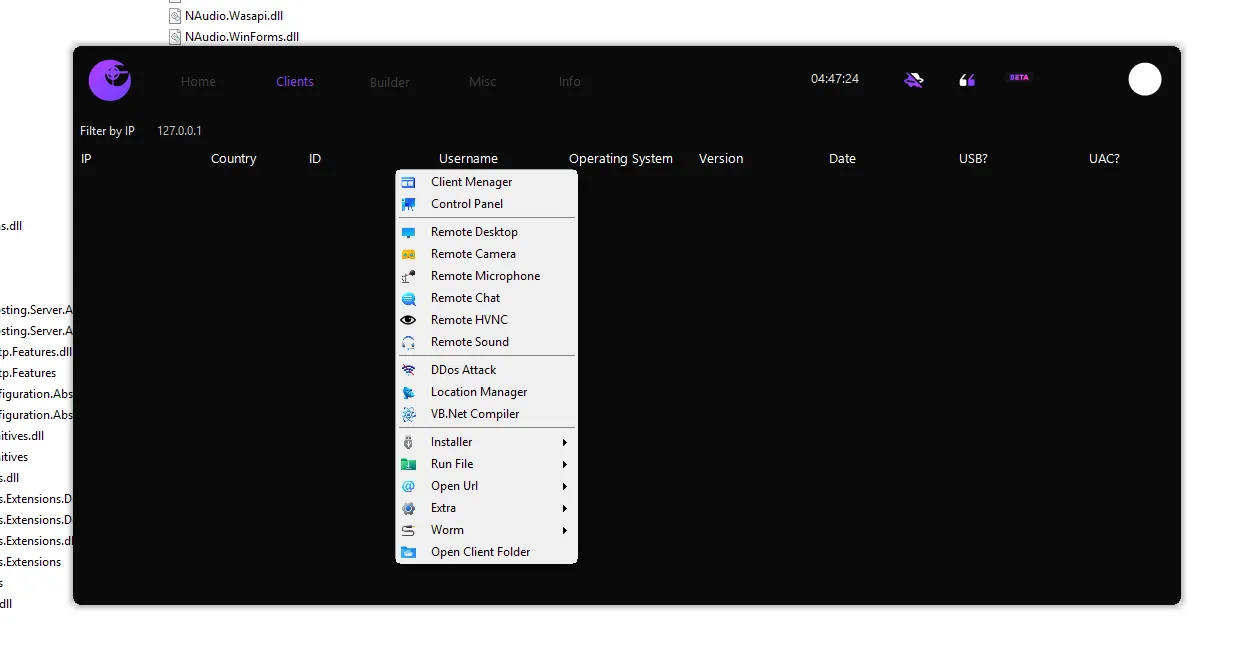
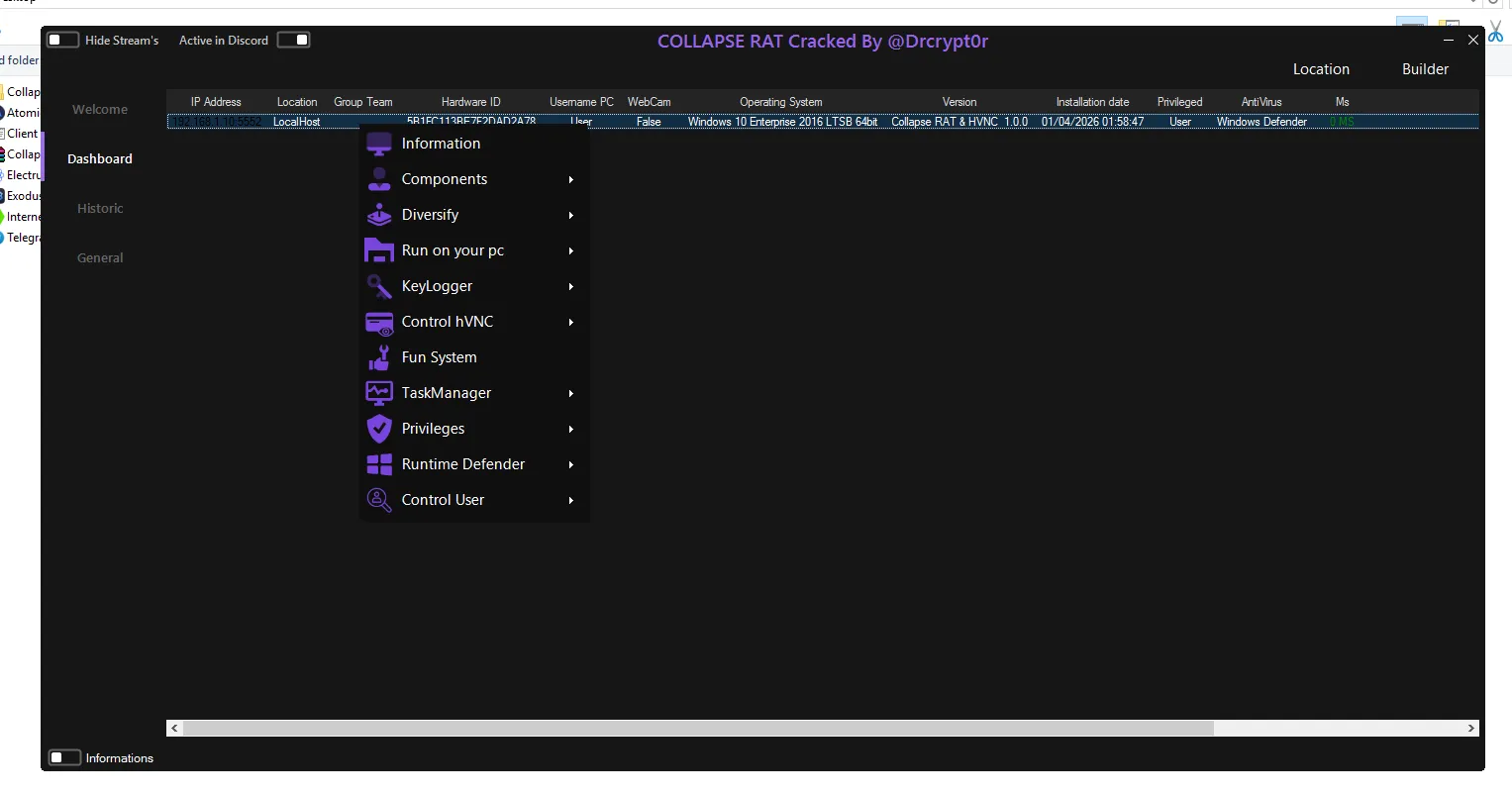
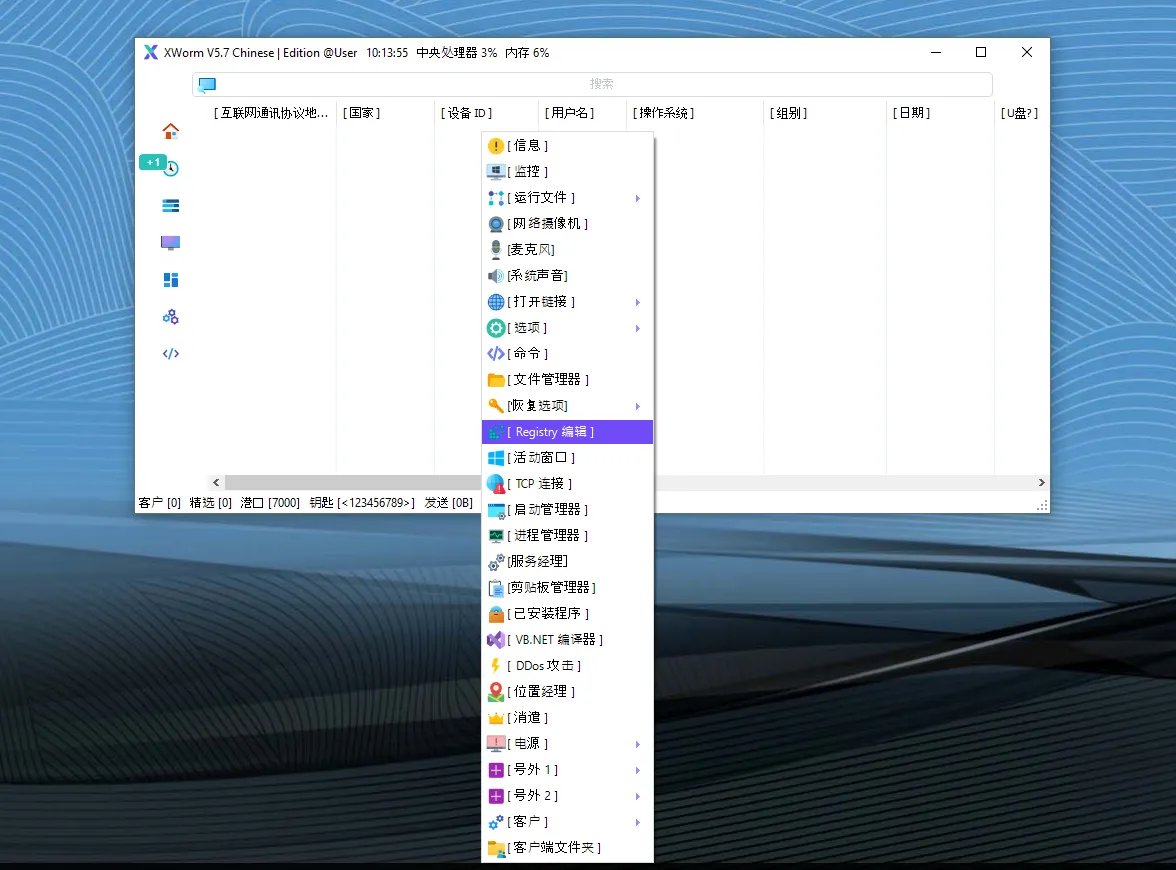
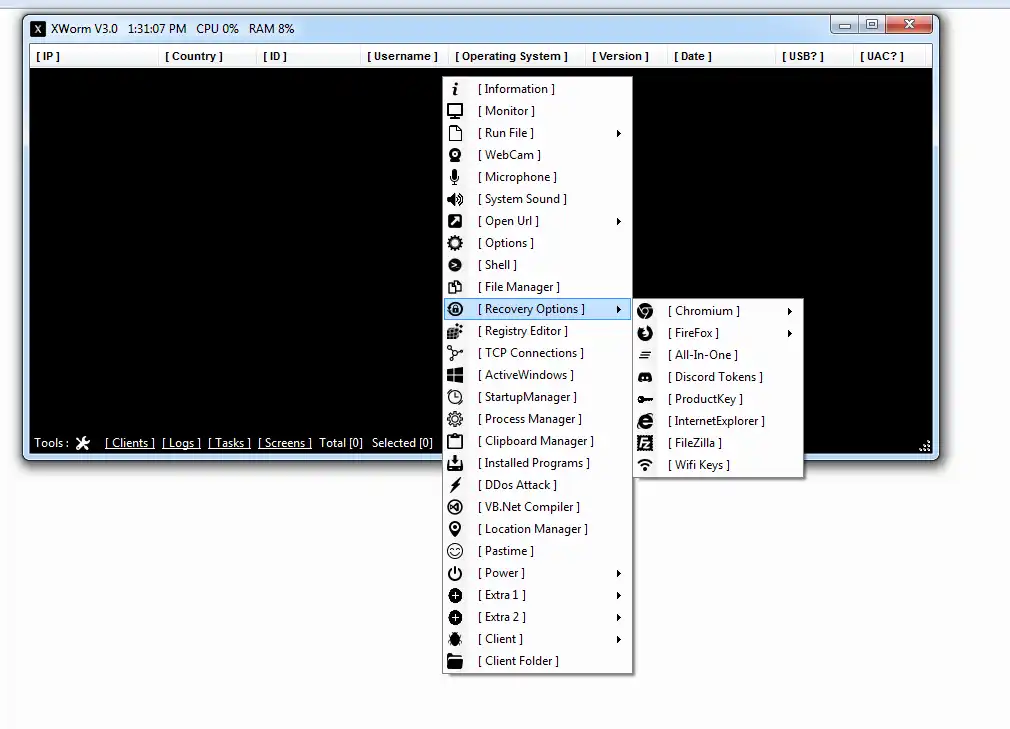
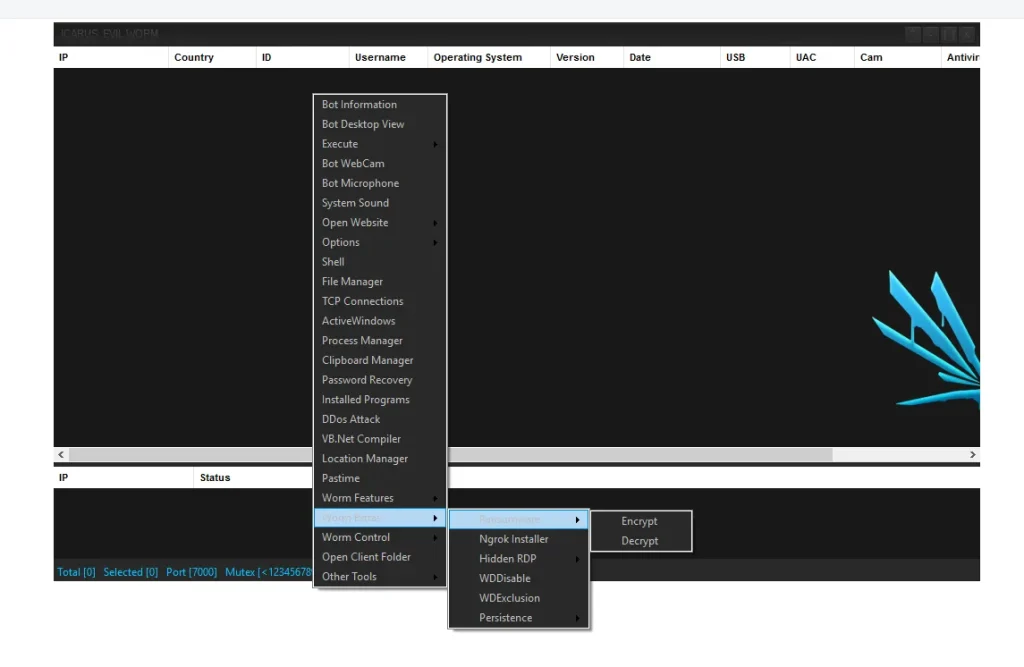
🔍 Core Functionalities of Icarus Evil Worm Cracked 2026 Explained
🖥️ 📡 Remote System Control
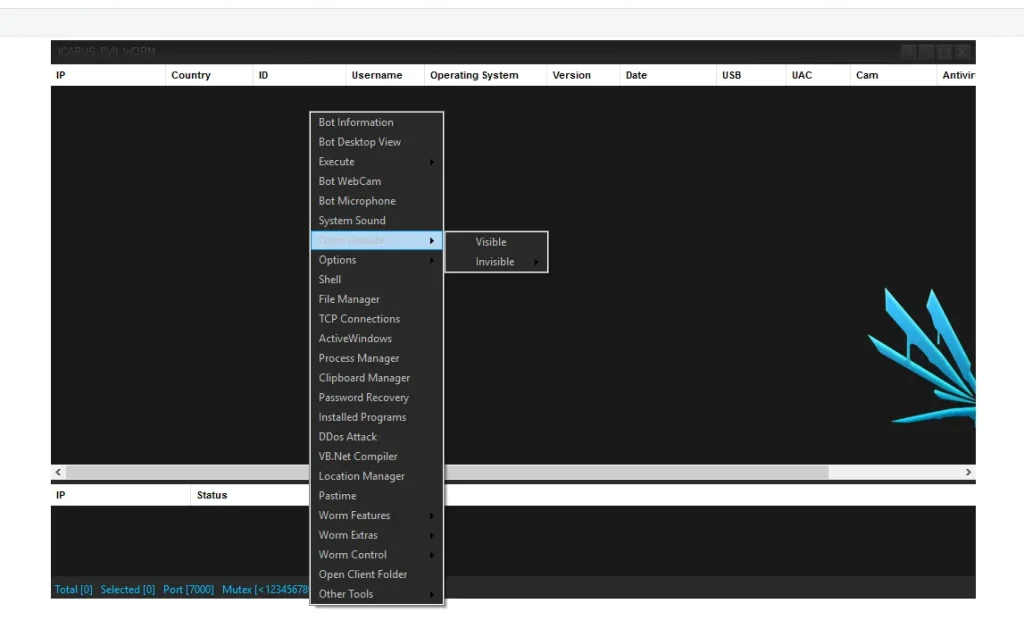
- Gain full access to a victim’s computer
- Execute commands remotely
- Monitor user activity in real time
👉 This allows attackers to completely take over a device without the user’s knowledge.
🎥 🎙️ Surveillance & Monitoring
- Activate webcam secretly
- Record audio through microphone
👉 These features are often used for spying, blackmail, or corporate espionage.
🔑 📂 Data Theft Capabilities
- Extract saved browser passwords
- Access personal and business files
- Capture login sessions and cookies
👉 This can lead to identity theft, account breaches, and financial loss.
🔁 🔌 Worm-Based Propagation
- Spread through USB drives
- Move across internal networks automatically
👉 A single infected device can compromise an entire organization.
⚠️ What is Icarus Evil Worm Cracked 2026?
The Icarus Evil Worm 2026 Cracked version is an unauthorized, modified release where all licensing protections have been removed.

💣 Why This Version is Especially Dangerous
🆓 Free Public Distribution
Previously sold privately, it is now freely available on various platforms.
👉 This dramatically increases the number of potential attackers.
🧑💻 Beginner-Friendly Usage

- Simple interface
- Pre-configured attack modules
👉 Even individuals with no coding experience can deploy it.
⚙️ Full Feature Unlock
All advanced features are accessible without restriction.
👉 This enables large-scale and highly damaging attacks.
⚙️ Advanced Features in Detail
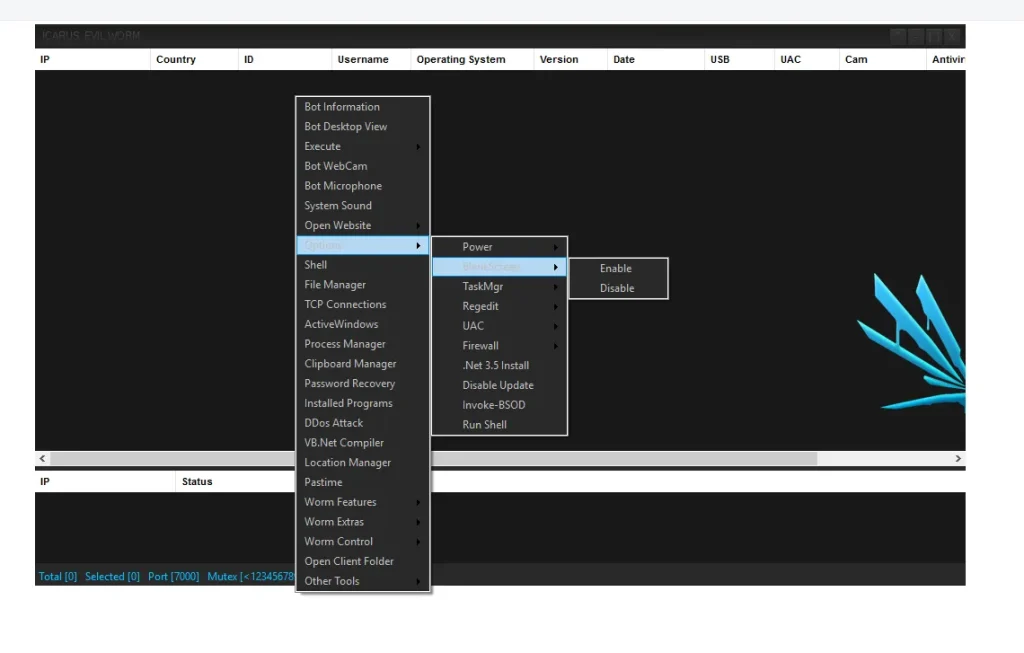
🔐 🧩 Persistence Mechanisms
- UAC Bypass
👉 This feature allows the malware to gain administrative privileges without triggering security warnings. It ensures deep system access and makes removal difficult. - Prevent Sleep Mode
👉 Keeps the infected system active, maintaining a continuous connection with the attacker’s control panel.
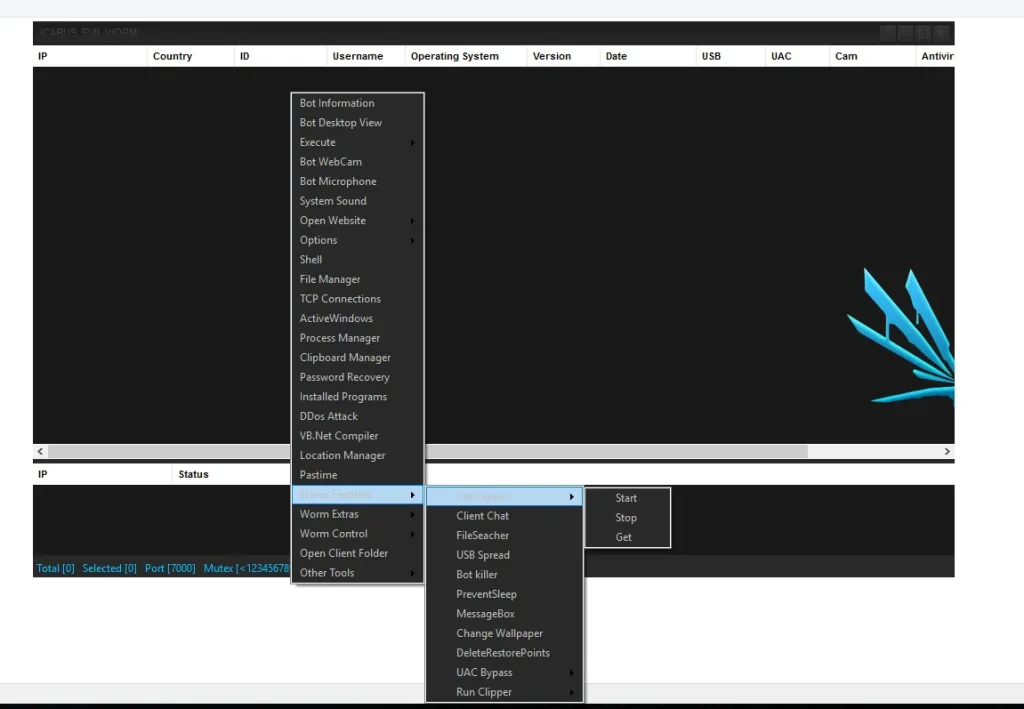
🔁 🌐 Propagation Capabilities
- USB Spread
👉 Infects removable drives, allowing the malware to spread offline between multiple devices. - Network Propagation
👉 Moves laterally across connected systems, targeting shared folders and weak security configurations.
💥 🧨 Destructive Functions
- Delete Restore Points
👉 Removes system recovery options, preventing users from restoring their system to a safe state. - DDoS Attack Module
👉 Converts infected devices into bots that can be used in large-scale Distributed Denial-of-Service attacks.
🕵️ 📋 Data Theft Modules
- Clipboard Hijacking
👉 Monitors copied data and replaces cryptocurrency wallet addresses, redirecting funds during transactions. - Password Recovery Tools
👉 Extracts stored credentials from browsers and applications, enabling unauthorized access to accounts.
🛡️ 🧬 Evasion Techniques
- Antivirus Bypass
👉 Uses obfuscation techniques to avoid detection by security software. - Stealth Execution
👉 Runs silently in the background, making it difficult for users to notice unusual activity.
📉 Why Cracked Malware is a Major Threat
1️⃣ 🎯 Reduced Entry Barrier
👉 Advanced hacking tools are now accessible to inexperienced users, increasing the number of cyber attackers globally.
2️⃣ 🌍 Shift Toward Mass Attacks
👉 Instead of targeting specific individuals, attackers now launch large-scale campaigns affecting thousands of users.
3️⃣ ⚠️ Hidden Risks for Attackers
👉 Cracked versions often contain hidden backdoors, meaning attackers themselves can be monitored or compromised.
🌍 Real-World Impact in Icarus Evil Worm Cracked 2026
The spread of Icarus Evil Worm 2026 Cracked has led to:
- Increased phishing and malware campaigns
- Rapid growth of botnet networks
- Higher rates of identity theft
- Financial losses for individuals and businesses
👉 Organizations across the US and Europe are particularly vulnerable due to their digital dependency.
🛡️ Cybersecurity Protection Guide
✅ 🔌 Disable AutoPlay
👉 Prevents automatic execution of malicious files from USB devices, reducing infection risk.
✅ 🔒 Use Application Control (AppLocker)
👉 Restricts unauthorized applications from running, improving system security.
✅ 🔄 Keep Systems Updated
👉 Regular updates patch vulnerabilities that malware often exploits.
✅ 🌐 Monitor Network Traffic
👉 Detect unusual activity, especially on uncommon ports like Port 7000, which may indicate malware communication.
✅ 🛡️ Install Advanced Security Software
👉 Use antivirus solutions with real-time protection and behavioral detection features.
Download Icarus Icarus Evil Worm Cracked 2026
📌 Conclusion
The rise of Icarus Evil Worm Cracked 2026 highlights a critical shift in cyber threats. By removing cost and complexity barriers, it has enabled widespread misuse of powerful malware tools.
👉 For individuals and organizations alike, adopting strong cybersecurity practices is essential to minimize risk and protect sensitive data.
❓ FAQs
❓ What is Icarus Evil Worm Cracked 2026?
It is a cracked version of a RAT-worm malware that allows attackers to control systems and spread infections.
❓ Is it illegal in the US and Europe?
Yes, creating, distributing, or using malware is illegal and punishable under cybersecurity laws.
❓ How does it spread?
Through USB devices, phishing emails, malicious downloads, and network vulnerabilities.
❓ Why is the cracked version more dangerous?
Because it is freely accessible and easy to use, increasing the number of cyberattacks.
❓ Can antivirus detect it?
Some versions can be detected, but advanced variants may evade detection, making prevention essential.
❓ What are common signs of infection?
- Slow system performance
- Unknown background processes
- Unusual network activity