S400 RAT 2026 (Cracked) – Complete Malware Analysis, Features & Security Risks
🧠 Introduction S400 RAT 2026
S400 RAT 2026 (Cracked) is a highly dangerous Remote Access Trojan (RAT) that appears to be a leaked or pirated version of a commercial cybercrime tool. It is designed to give attackers full unauthorized control over Windows-based systems while remaining hidden from detection.
Unlike older malware, this RAT combines multiple attack techniques such as credential theft, cryptocurrency mining, clipboard hijacking, and self-propagation. Its cracked availability makes it accessible to low-skill attackers, increasing global cybersecurity risks—especially across the United States and Europe.
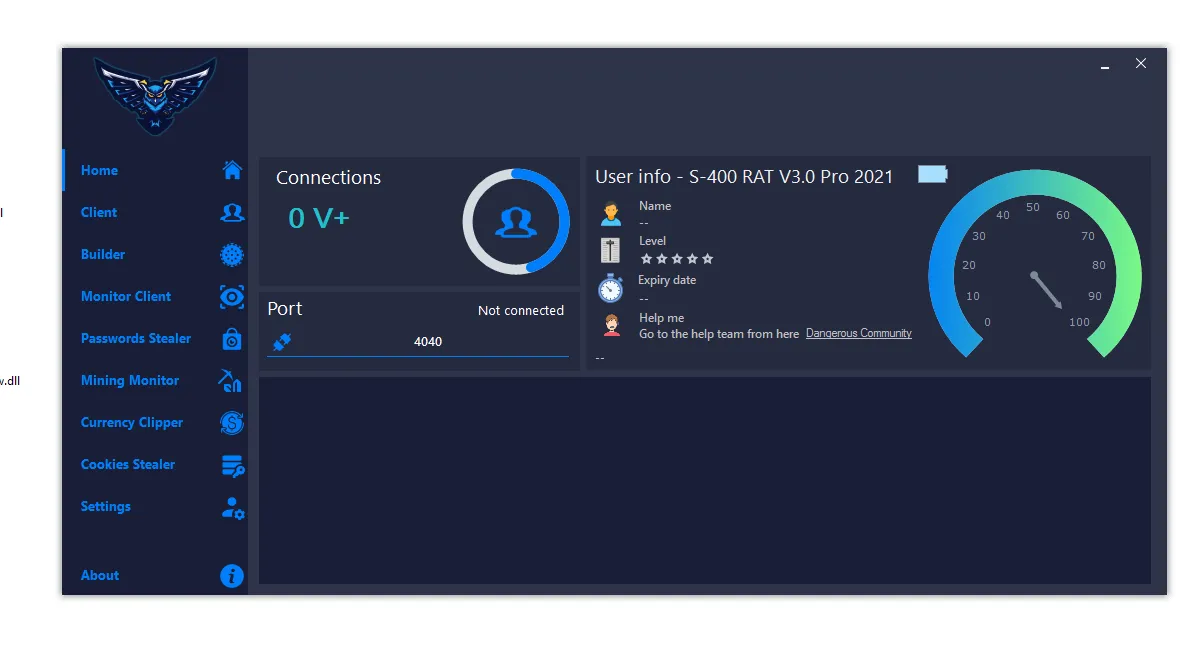
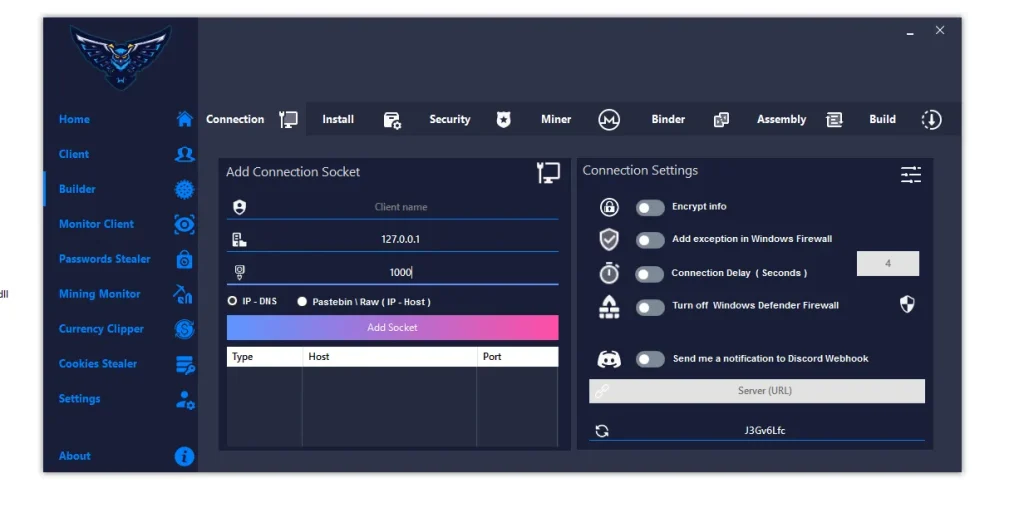
⚙️ 1. Client & Connection Management in S400 RAT 2026
🔌 How Attackers Control Infected Systems
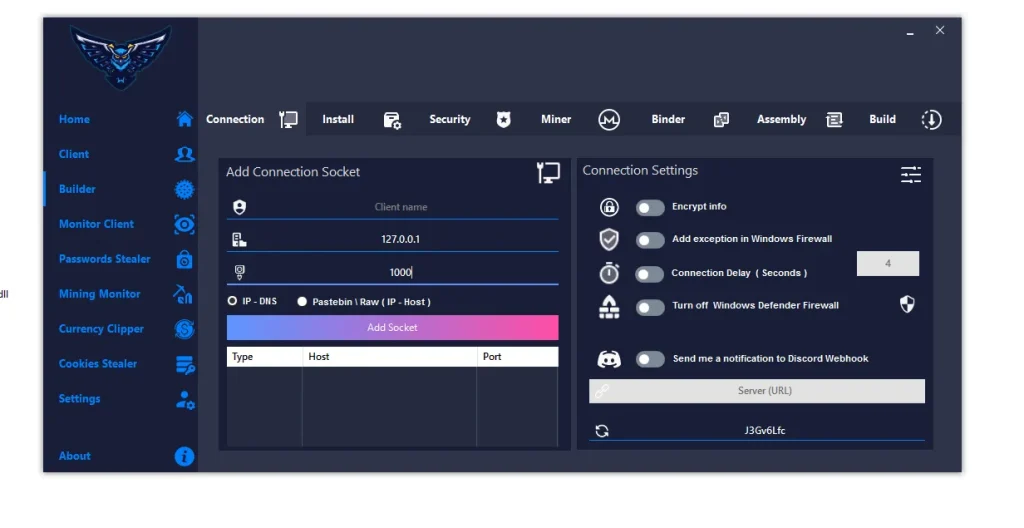
- 🔹 Connection Socket Setup:
This feature allows attackers to manually configure IP addresses and ports to establish direct communication with infected machines. It ensures stable control even in restricted networks.
It also enables flexible targeting, allowing attackers to manage multiple victims simultaneously. - 🔹 Encrypted Communication:
All data transferred between attacker and victim is encrypted to avoid detection by firewalls and network monitoring systems.
This makes it difficult for cybersecurity tools to identify suspicious traffic patterns. - 🔹 Dynamic Command & Control (C2):
The malware can fetch updated server addresses using DNS or remote sources, ensuring continuous connectivity.
Even if one server is taken down, attackers can quickly switch to another without rebuilding the malware. - 🔹 Discord Notification Integration:
Sends automatic alerts to attackers when a new system is infected, including system details.
This provides real-time monitoring and immediate awareness of successful attacks.
💾 2. Installation & Persistence of S400 RAT 2026

🧩 How Malware Stays Hidden
- 🔹 Stealth Installation Paths:
The malware installs itself in system folders like AppData or ProgramData to blend with legitimate files.
This reduces suspicion and makes manual detection difficult for average users. - 🔹 Startup Persistence Mechanism:
It adds itself to Windows startup so it runs automatically after every reboot.
This ensures long-term access without requiring reinfection. - 🔹 Hidden Execution Mode:
The malware runs silently in the background without showing any visible windows or alerts.
Users remain unaware while malicious activities continue. - 🔹 Anti-VM & Sandbox Detection:
Detects virtual machines and analysis environments used by security researchers.
If detected, it may stop execution to avoid being analyzed.
🛡️ 3. Security Evasion & System Manipulation of S400 RAT 2026
🔒 Disabling System Defenses
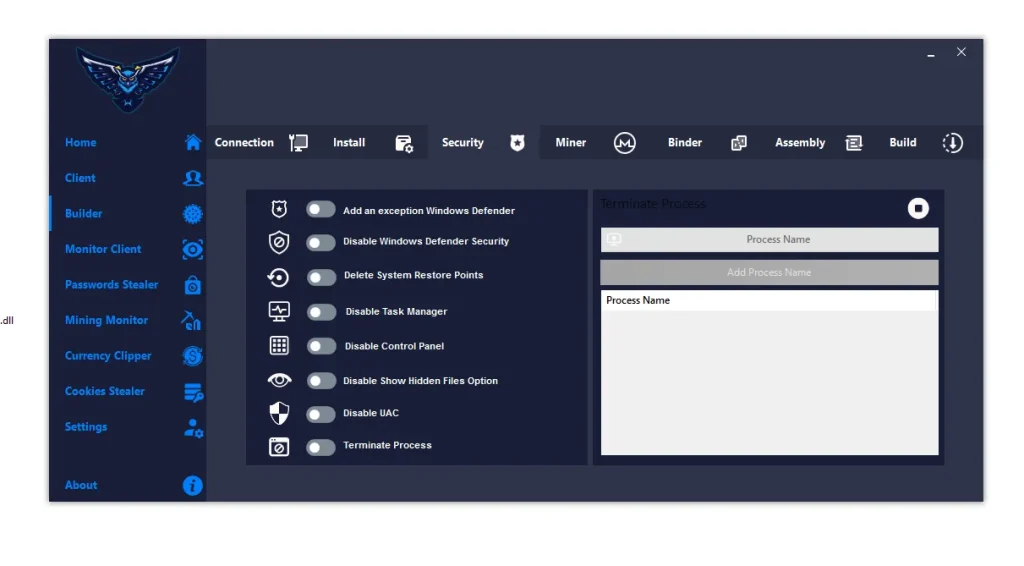
- 🔹 Windows Defender Bypass:
The malware adds itself to the exclusion list or disables Defender entirely.
This prevents scanning and automatic removal. - 🔹 Task Manager Blocking:
Disables access to Task Manager so users cannot terminate malicious processes.
This increases the malware’s survival time. - 🔹 System Restore Deletion:
Deletes restore points to prevent recovery of the system to a safe state.
This forces victims into more complex recovery processes. - 🔹 Control Panel Restriction:
Blocks access to system settings, limiting user control over their own device.
This further traps the victim in a compromised environment.
⛏️ 4. Cryptocurrency Miner with S400 RAT 2026
💻 Unauthorized Resource Usage
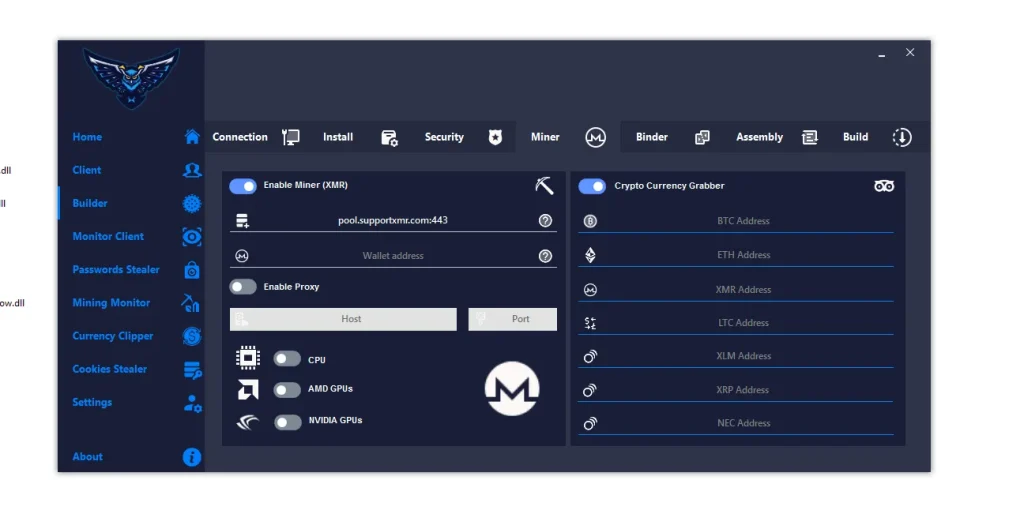
- 🔹 Monero Mining Activation:
The malware secretly uses CPU/GPU power to mine cryptocurrency like Monero.
This slows down the system and increases electricity consumption. - 🔹 Custom Mining Pools:
Attackers can connect victims’ machines to their own mining pools.
This ensures all profits go directly to the attacker. - 🔹 Hardware Utilization:
Uses both CPU and GPU resources to maximize mining efficiency.
This can cause overheating and hardware damage over time.
💸 5. Clipboard Hijacker (Clipper) feature of S400 RAT 2026
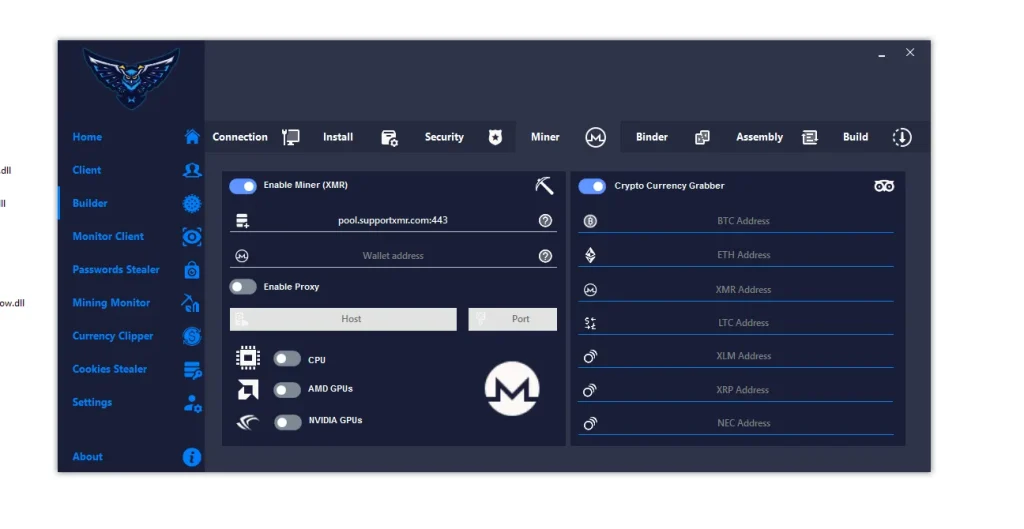
🔄 Crypto Transaction Manipulation
- 🔹 Clipboard Monitoring:
Continuously scans copied text for cryptocurrency wallet addresses.
It activates only when relevant patterns are detected. - 🔹 Address Replacement Attack:
Replaces the copied wallet address with the attacker’s address instantly.
Victims unknowingly send funds to the attacker. - 🔹 Multi-Currency Support:
Supports Bitcoin, Ethereum, Monero, and other cryptocurrencies.
This increases the attack success rate across different users.
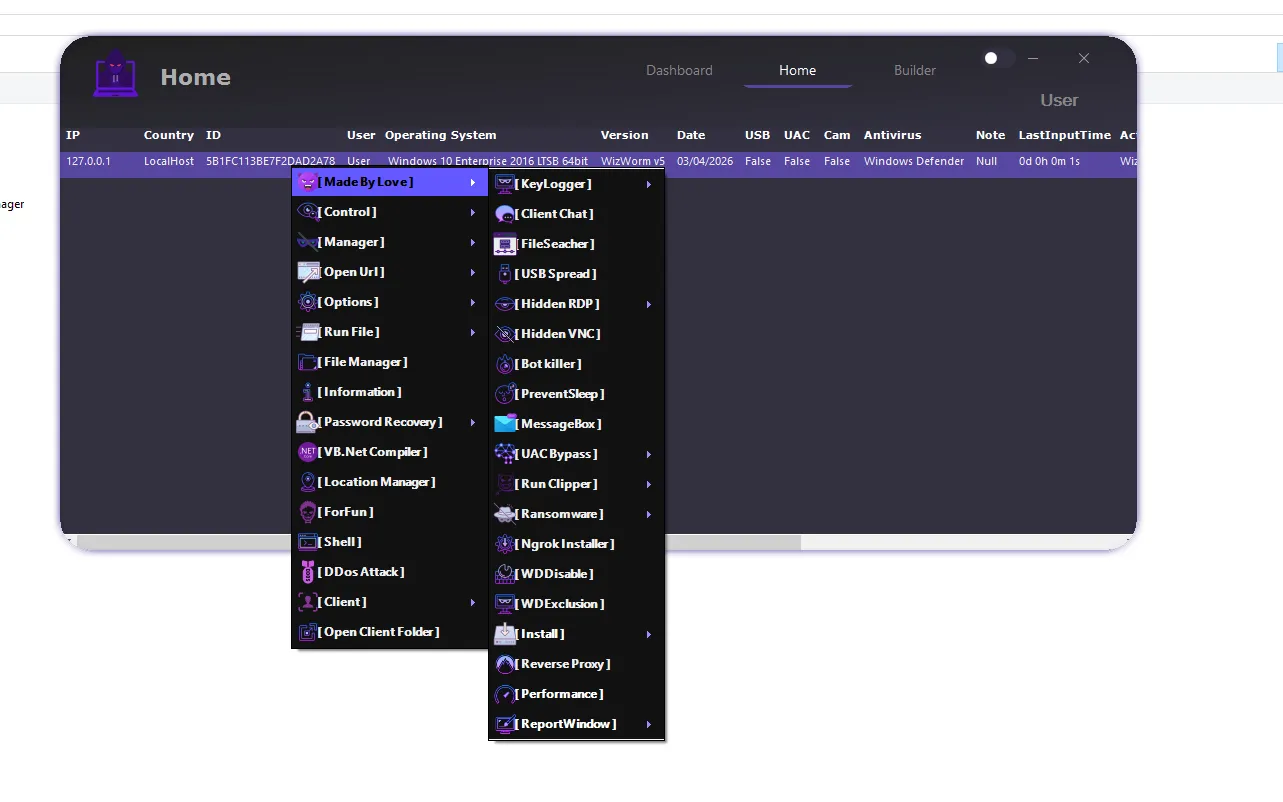
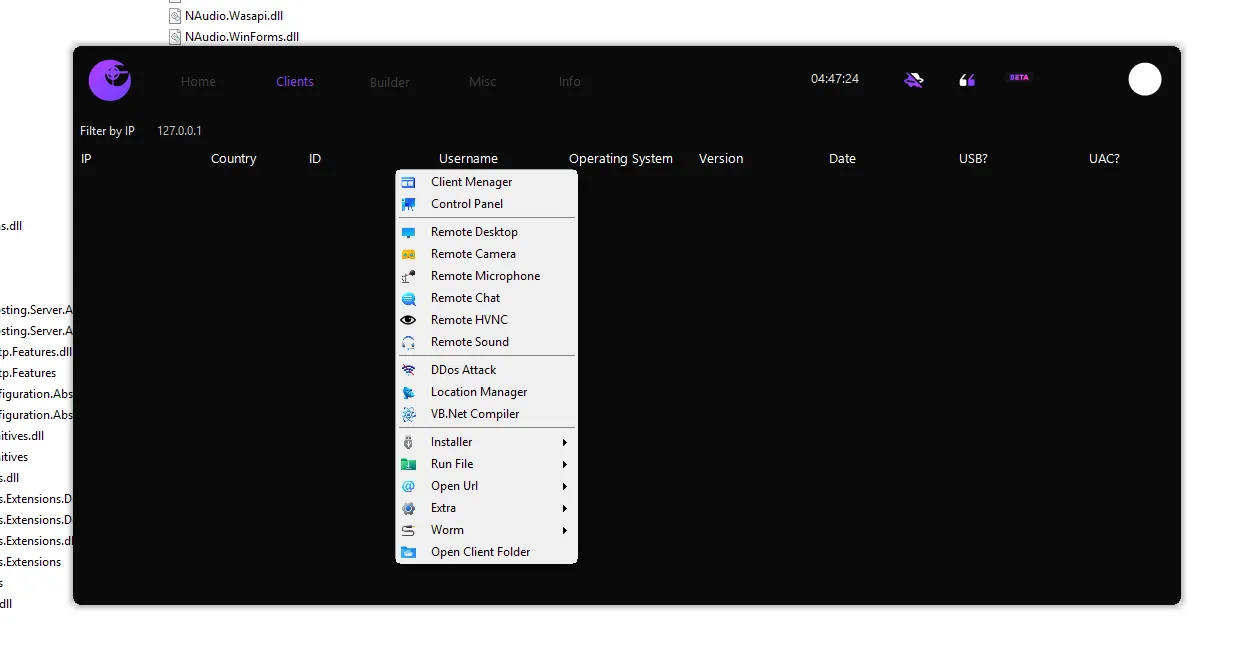
🔑 6. Password & Data Theft

📂 Sensitive Information Extraction
- 🔹 Browser Credential Theft:
Extracts saved usernames and passwords from popular browsers.
This can lead to account takeovers across multiple platforms. - 🔹 Cookie Hijacking:
Steals active session cookies to bypass login authentication.
Attackers can access accounts without needing passwords. - 🔹 Data Exfiltration:
Sends stolen data to remote servers controlled by attackers.
This data can be sold or used for further attacks.
🧱 7. Builder & Payload Configuration
🛠️ Custom Malware Creation
- 🔹 Payload Customization:
Attackers can assign names and configure behavior before deployment.
This allows targeted and flexible attacks. - 🔹 File Disguise Techniques:
Uses fake file extensions or icons to appear legitimate.
This tricks users into executing the malware. - 🔹 Antivirus Evasion:
Applies obfuscation and encryption to bypass detection.
This increases infection success rates.
🔗 8. Binder & Assembly Cloning
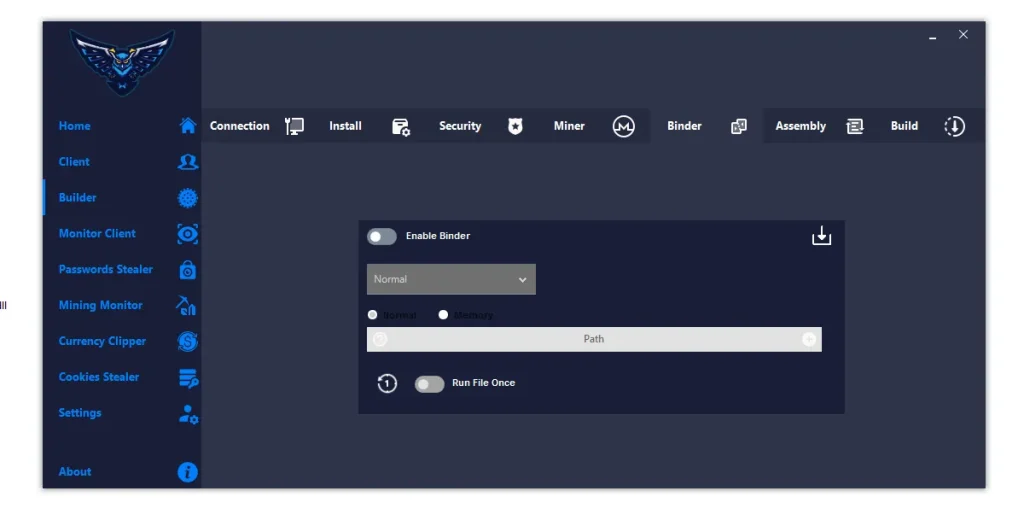
📎 Social Engineering Enhancement
- 🔹 File Binding Feature:
Combines malware with legitimate files like software or documents.
Users unknowingly execute malware along with the file. - 🔹 Metadata Cloning:
Copies properties from trusted files to appear genuine.
This builds user trust and reduces suspicion. - 🔹 Custom Icons:
Uses familiar icons to trick users visually.
This increases the likelihood of execution.
🔄 9. Spreading Mechanisms
🌐 Self-Propagation Techniques
- 🔹 USB Infection:
Copies itself to removable drives and spreads across systems.
This enables offline propagation. - 🔹 Link-Based Distribution:
Spreads via phishing links through email or messaging apps.
This targets a large number of users quickly. - 🔹 File Infection:
Injects malware into common file formats like ZIP or EXE.
Users unknowingly spread the infection further.
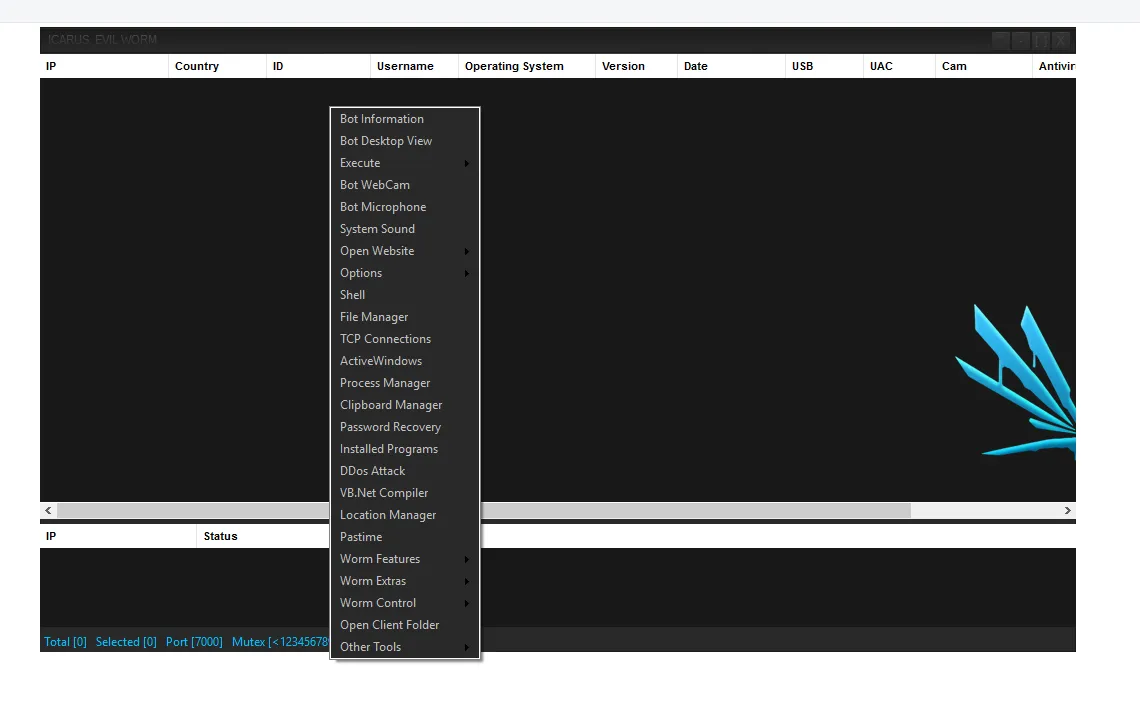
🖥️ 10. Monitoring & Remote Control
📡 Real-Time Victim Management
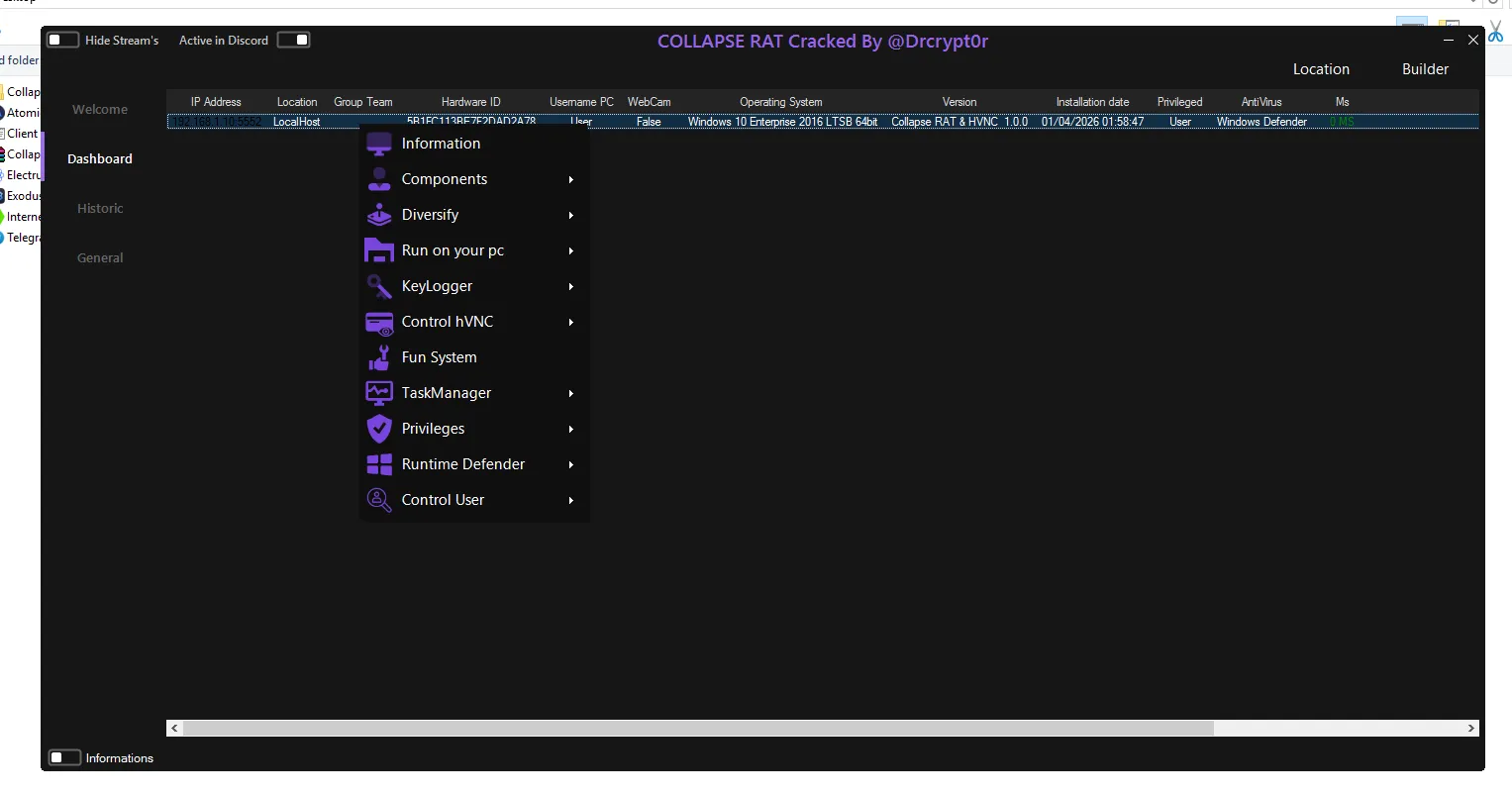
- 🔹 Client Dashboard:
Displays infected systems with detailed information.
Allows centralized control over multiple victims. - 🔹 Remote Access Capabilities:
Enables file access, screen monitoring, and command execution.
Attackers gain full control over the system. - 🔹 Activity Tracking:
Monitors mining, clipboard activity, and stolen data.
Helps attackers optimize their operations.
📊 11. Victim Profiling
🧾 System Intelligence Gathering
- 🔹 Hardware & OS Details:
Collects system specifications and operating system data.
Helps attackers tailor further attacks. - 🔹 User Identification:
Captures usernames and device names.
Enables targeted exploitation. - 🔹 Connection Monitoring:
Tracks online/offline status of infected machines.
Ensures continuous attacker access.
Download S400 RAT 2026
⚠️ Conclusion
S400 RAT 2026 (Cracked) represents a serious cybersecurity threat due to its advanced capabilities and widespread accessibility. It combines multiple malicious techniques into a single tool, making it highly effective and dangerous.
Understanding how such malware works is essential for prevention, detection, and response. Individuals and organizations in the US and Europe should prioritize strong cybersecurity practices, updated antivirus software, and safe browsing habits.
❓ FAQs
❓ What is S400 RAT 2026?
S400 RAT 2026 is a Remote Access Trojan that allows attackers to control infected computers, steal data, and perform malicious activities without user consent.
❓ Is S400 RAT legal to use?
No, using or distributing such malware is illegal in most countries, including the United States and European nations, under cybersecurity and fraud laws.
❓ How does S400 RAT infect systems?
It spreads through phishing links, infected files, USB drives, and social engineering techniques that trick users into executing malicious files.
❓ Can antivirus detect S400 RAT?
Modern antivirus tools can detect many variants, but cracked or modified versions may use evasion techniques to bypass detection.
❓ How can I protect my system?
Use updated antivirus software, avoid downloading unknown files, enable firewalls, and keep your operating system updated.