🚨 XWorm V 1.0 Cracked – Complete Guide, Features, Risks & Protection
🧠 Introduction to XWorm V 1.0 Cracked
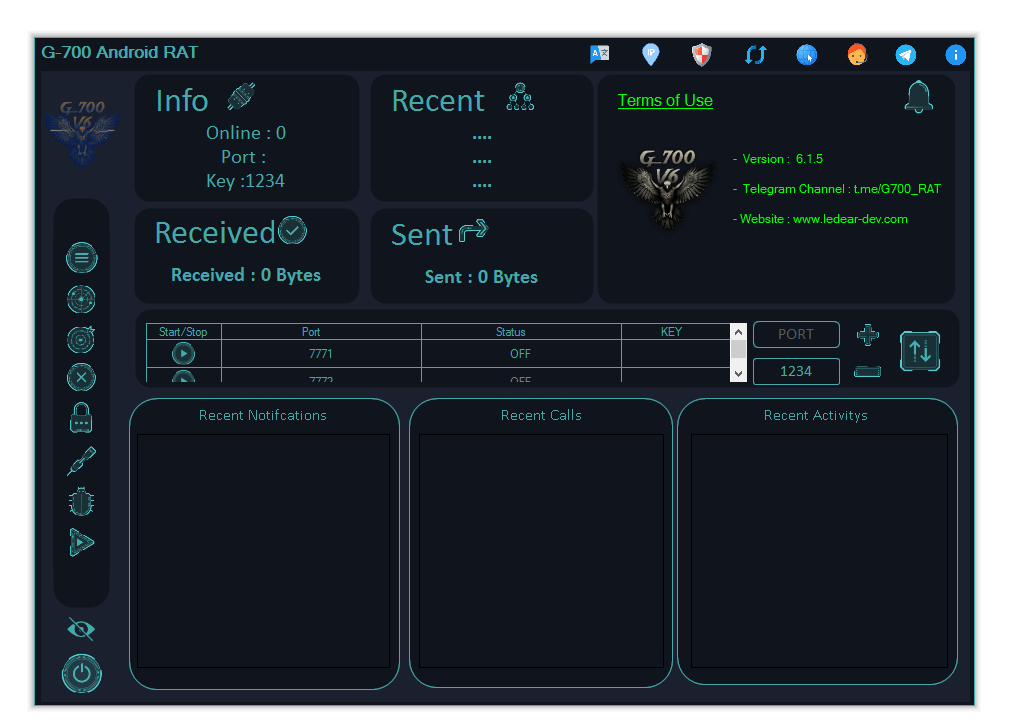
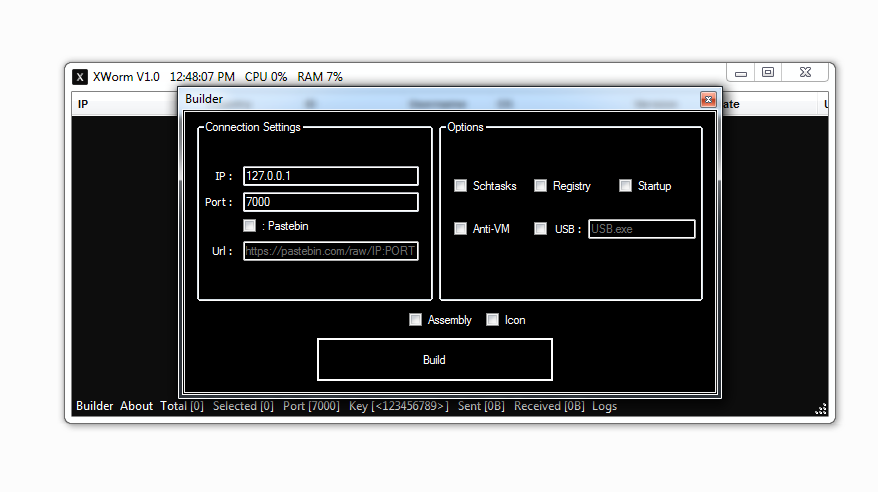
XWorm V 1.0 Cracked refers to an early modified or illegally distributed version of a Remote Access Trojan (RAT) that is often shared on underground platforms. These “cracked” versions are typically altered to bypass licensing or restrictions, making them easily accessible but extremely unsafe.
Even though this is an older version, it still poses serious cybersecurity risks. In many cases, cracked builds contain hidden malicious code, meaning even the person using it can unknowingly become a victim.
⚠️ This content is for educational and cybersecurity awareness purposes only.
🔍 Why XWorm V 1.0 Cracked is Dangerous
⚡ Major Risk Factors
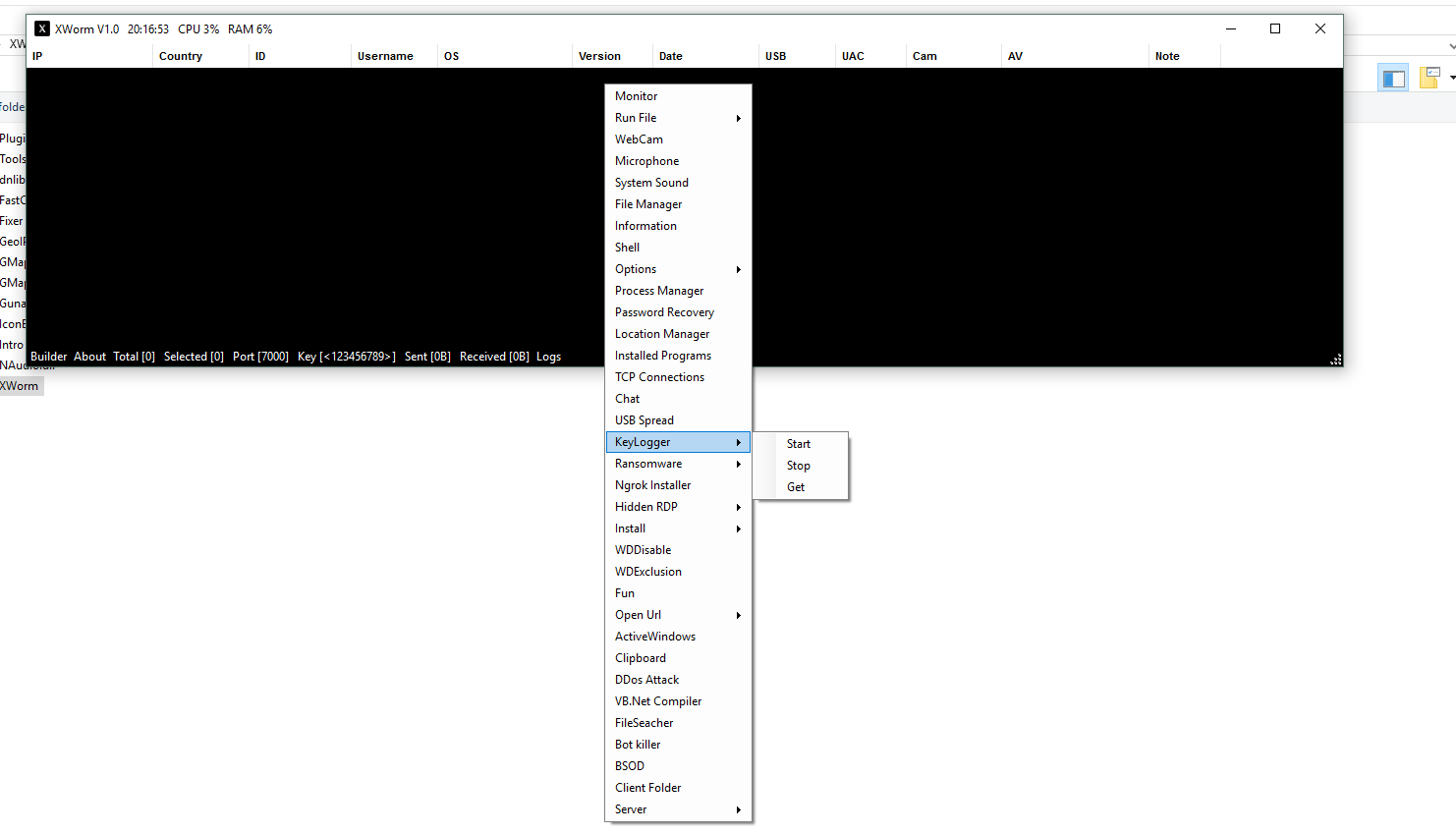
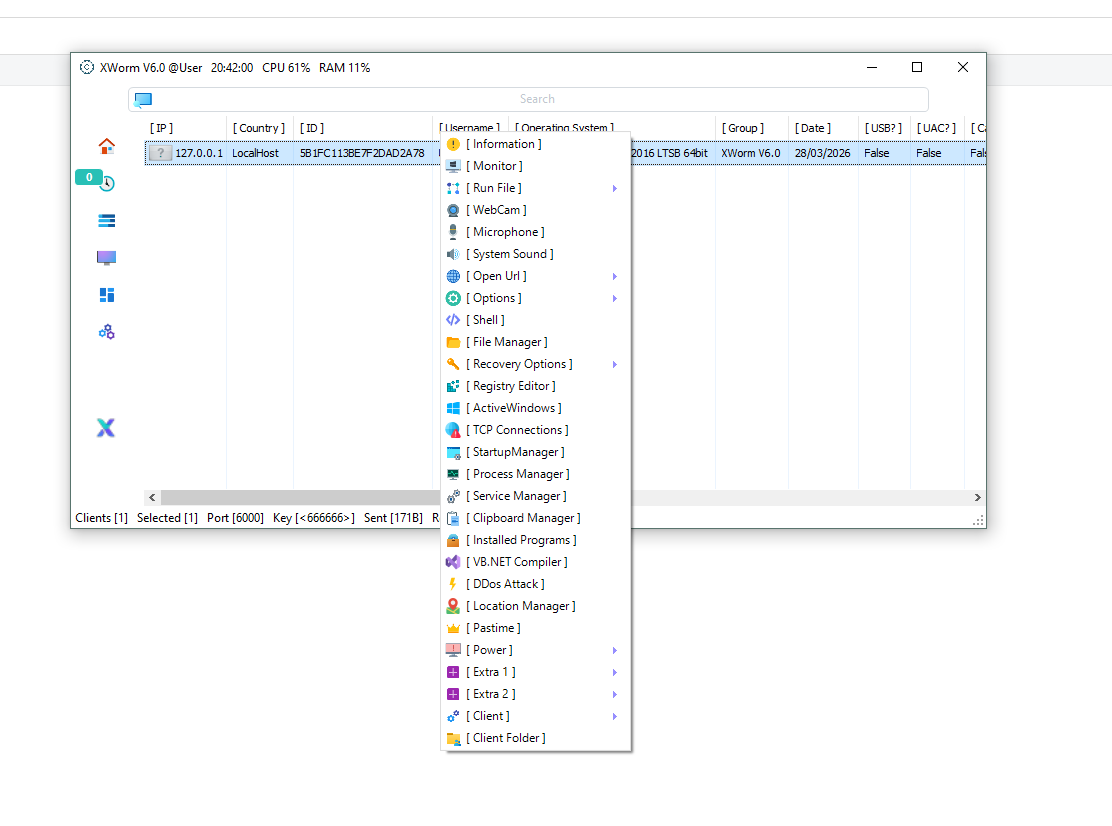
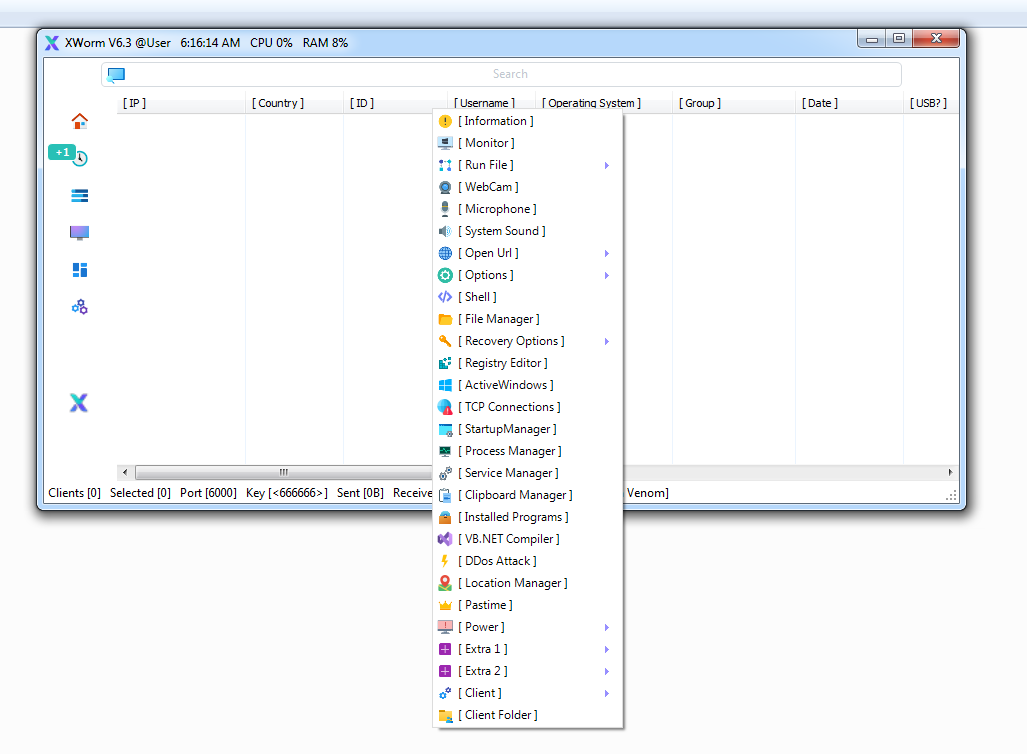
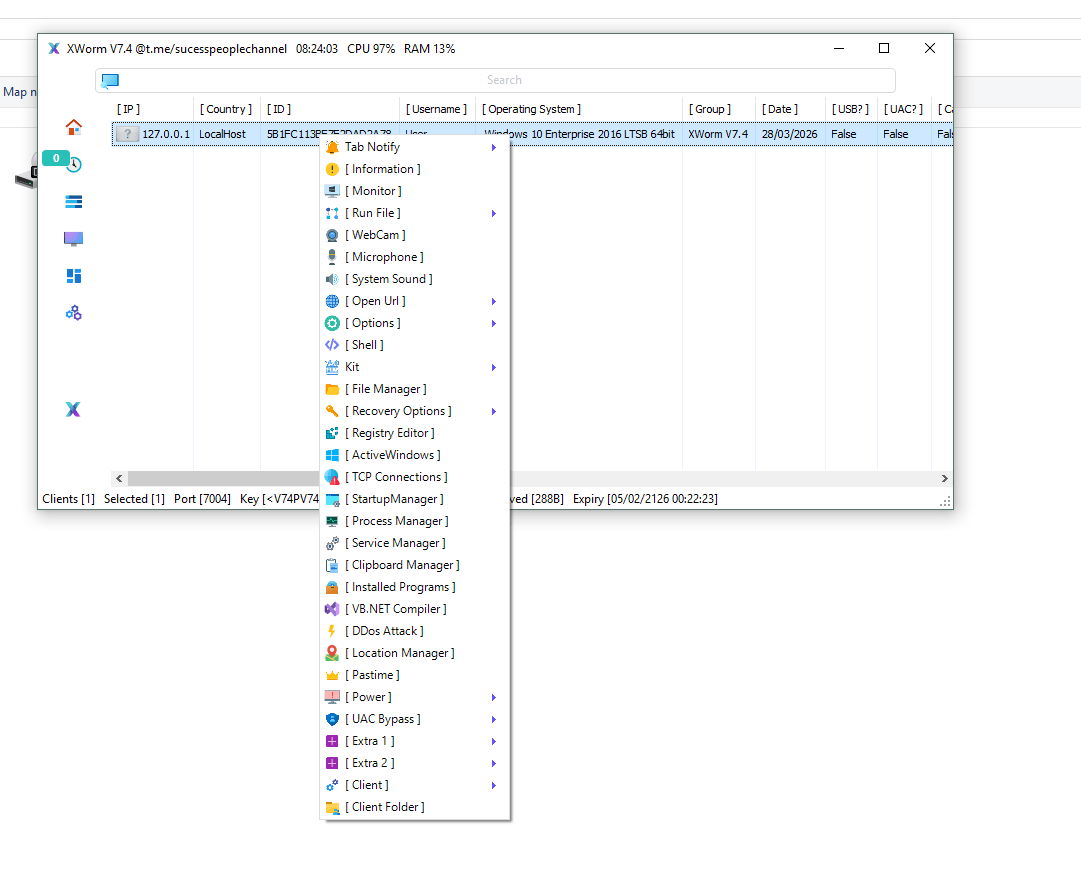
🔹 🖥️ Full System Access
XWorm V 1.0 Cracked allows unauthorized remote control of a victim’s computer. Attackers can open files, execute commands, and manage the entire system without permission, resulting in complete loss of control for the user.
🔹 🔑 Data & Credential Theft
This malware can extract stored passwords, browser data, and sensitive personal or financial information. Such data is often used for identity theft, fraud, or unauthorized account access.
🔹 ⌨️ Keystroke Logging (Keylogger)
It records every keystroke made by the user. This means login credentials, private chats, and confidential information can be captured silently in real time.
🔹 📸 Screen Monitoring
Attackers can take screenshots or view the victim’s screen live. This creates a serious privacy risk and allows monitoring of all user activities.
🔹 🔄 Persistence Mechanism
The malware ensures it stays active by embedding itself into startup processes or system registry entries, making removal more difficult.
🔹 🧩 Hidden Malware in Cracked Builds
Cracked versions are often repackaged by unknown sources. These can include additional hidden payloads, backdoors, or spyware, making them even more dangerous than the original malware.
🔹 🕵️ Basic Anti-Detection Techniques
Even early versions like 1.0 may include obfuscation techniques to avoid simple antivirus detection, allowing it to operate undetected for longer periods.
⚙️ How XWorm V 1.0 Cracked Works
📥 Infection Methods
🔹 Phishing Emails
Victims receive emails with malicious attachments disguised as documents or installers. Opening them triggers malware execution.
🔹 Cracked Software Downloads
Downloading pirated or cracked tools is one of the most common infection methods. These files often contain embedded malware.
🔹 Malicious Links
Clicking unsafe links can initiate silent downloads and install malware without user awareness.
🔗 Execution Process
- User opens or downloads an infected file
- Malware executes in the background
- XWorm installs itself silently
- It connects to a Command & Control (C2) server
- The attacker gains remote access
🧪 Post-Infection Behavior
🔹 Data Collection
The malware begins collecting sensitive information such as saved passwords and browsing history.
🔹 User Activity Monitoring
It tracks system activity, keystrokes, and behavior continuously.
🔹 Additional Payload Deployment
Attackers may install more malicious programs to expand control.
🔹 Potential Ransomware Use
In some scenarios, attackers may encrypt files and demand payment.
🛠️ Technical Overview
| 🔧 Feature | 📊 Details |
|---|---|
| Type | Remote Access Trojan (RAT) |
| Platform | .NET-based |
| Access | Remote Control |
| Persistence | Startup / Registry |
| Communication | C2 Server |
⚠️ Signs Your System May Be Infected
🚩 Warning Indicators
🔹 🐢 Slow Performance
A sudden decrease in system speed may indicate background malicious processes.
🔹 🔍 Unknown Programs
Unrecognized applications or processes can signal infection.
🔹 🔐 Unauthorized Access
Unexpected logins or suspicious activity in accounts may indicate stolen credentials.
🔹 ❌ Disabled Security Tools
Malware may turn off antivirus programs to avoid detection.
🔹 🌐 Suspicious Network Activity
Unusual outgoing connections may indicate communication with a remote attacker.
🔐 How to Protect Yourself
🛡️ Best Security Practices
🔹 🚫 Avoid Cracked Software
Downloading tools like XWorm V 1.0 Cracked is highly risky and often leads to infection.
🔹 📧 Be Careful with Emails
Always verify unknown senders before opening attachments.
🔹 🧰 Use Updated Security Software
Install trusted antivirus solutions and keep them updated.
🔹 🔄 Keep Your System Updated
Regular updates patch vulnerabilities used by malware.
🔹 📂 Disable Macros
Avoid enabling macros in documents from unknown sources.
Download XWorm V 1.0 Cracked
🧠 Conclusion
XWorm V 1.0 Cracked may be an older version, but it still represents a serious cybersecurity threat. Its ability to steal data, monitor users, and provide remote access makes it dangerous for both victims and those attempting to use it.
The biggest risk comes from cracked distributions, which often contain hidden malicious payloads. Staying informed and avoiding unsafe downloads is essential for maintaining security.
❓ Frequently Asked Questions (FAQ)
❓ What is XWorm V 1.0 Cracked?
It is a modified and illegally distributed version of a Remote Access Trojan used for unauthorized system access.
❓ Is XWorm V 1.0 Cracked safe?
No, it is extremely unsafe and may contain hidden malware that can harm both users and victims.
❓ How does it spread?
It spreads through phishing emails, malicious links, and cracked software downloads.
❓ Can antivirus detect it?
Yes, modern antivirus tools can detect many variants, but some versions may evade detection.
❓ What should I do if infected?
Disconnect from the internet, run a full antivirus scan, and consider reinstalling your system.