❓ What is XWorm V7.4 Cracked?
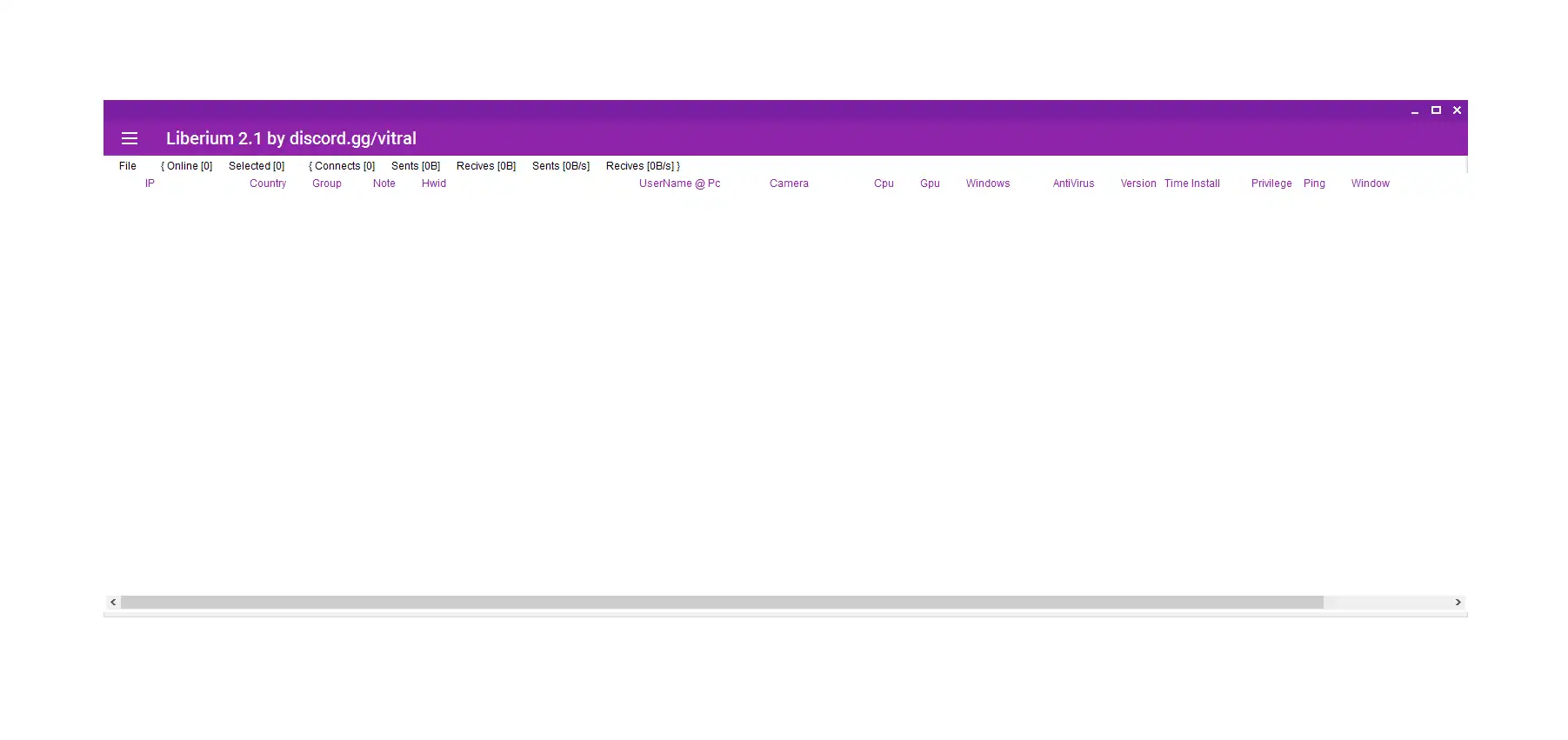
XWorm V7.4 Cracked refers to an unauthorized modified version of a Remote Access Trojan (RAT) that removes licensing restrictions.
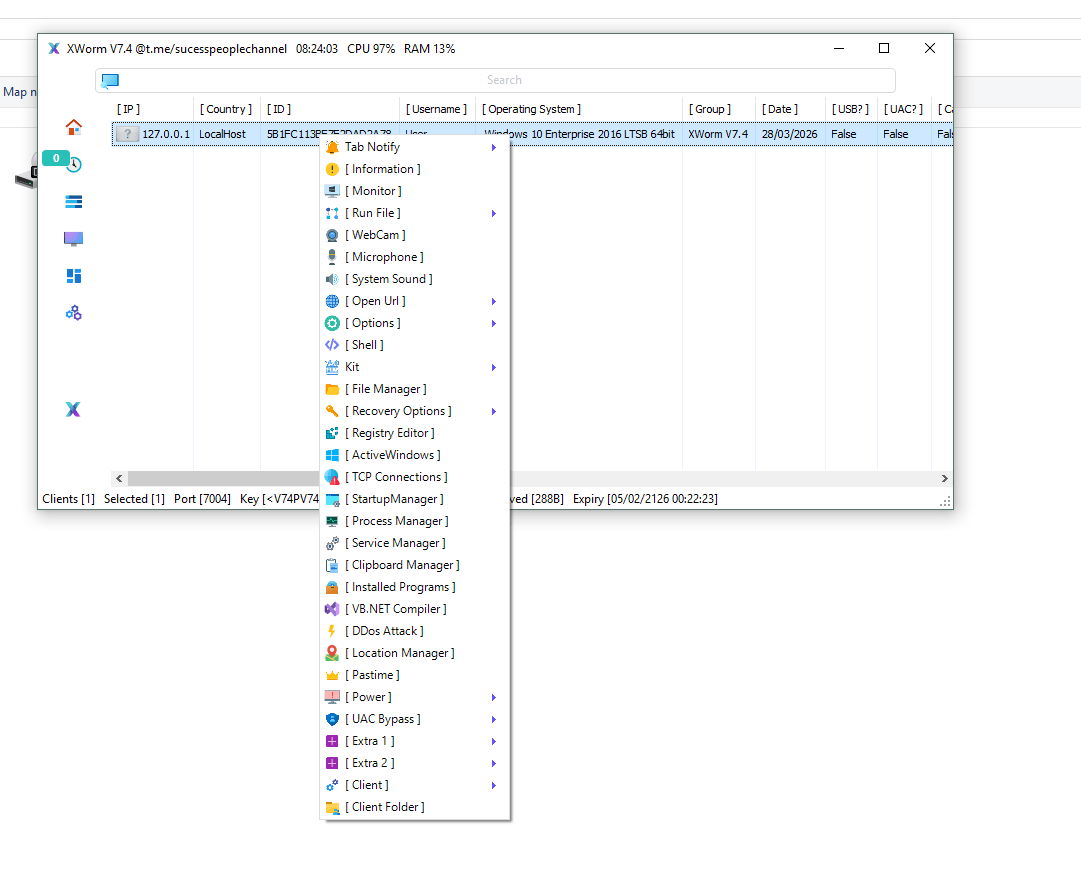
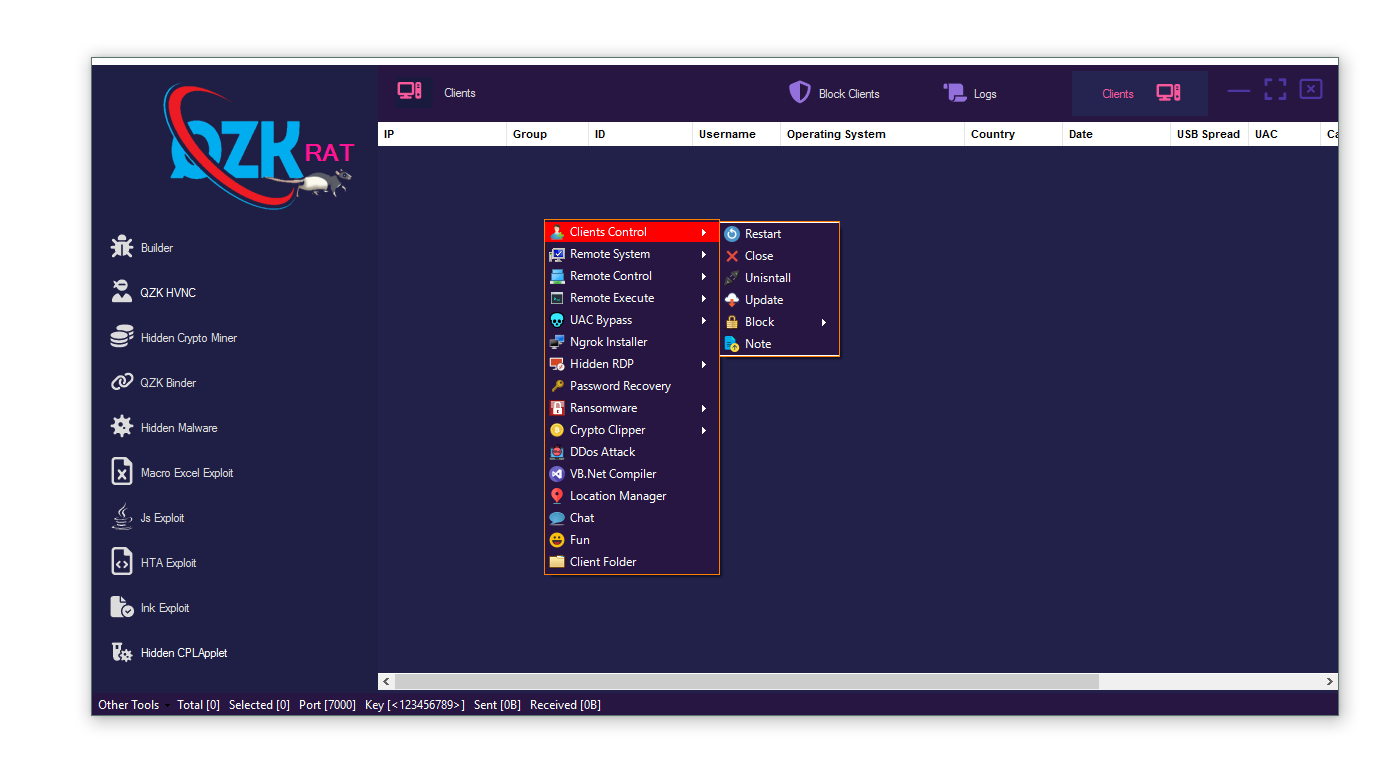
🔍 Core Capabilities:
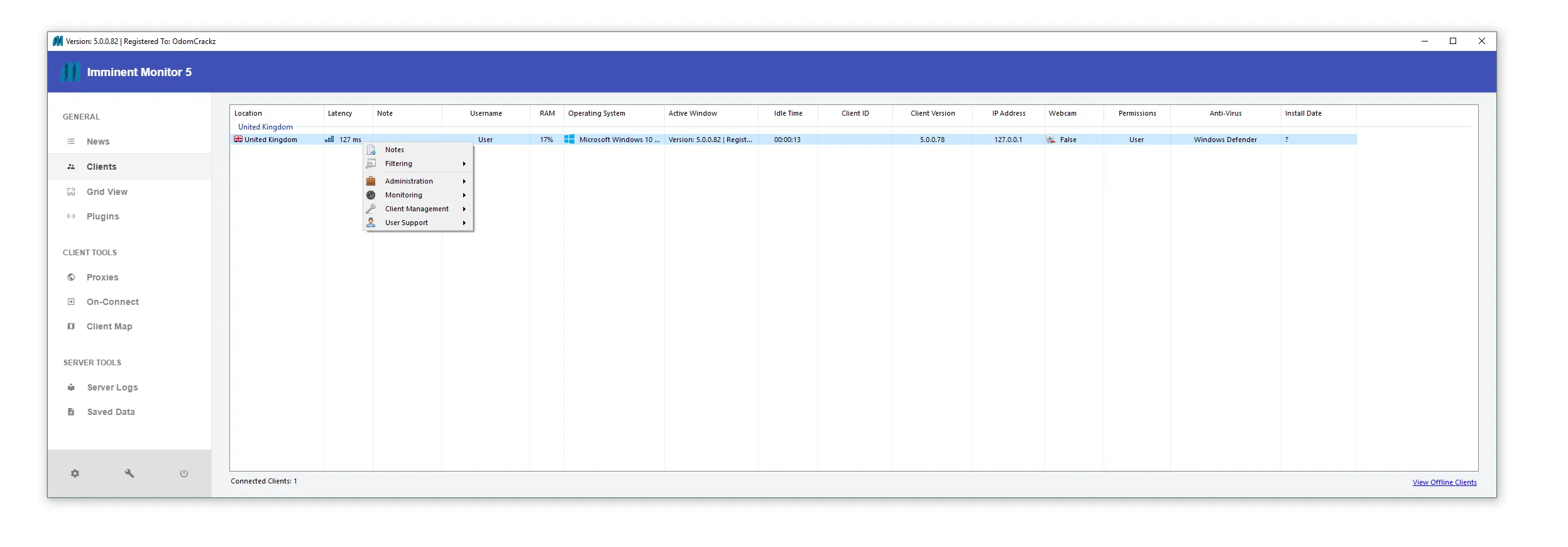
- 🖥️ Remote access to systems
- 🎥 User surveillance tools
- 🔑 Credential and data theft
- 💰 Financial manipulation (crypto theft)
- 🛡️ Security evasion
👉 It still operates on a client-server model, allowing remote control of infected machines.
🛠️ Builder Overview XWorm V7.4 Cracked
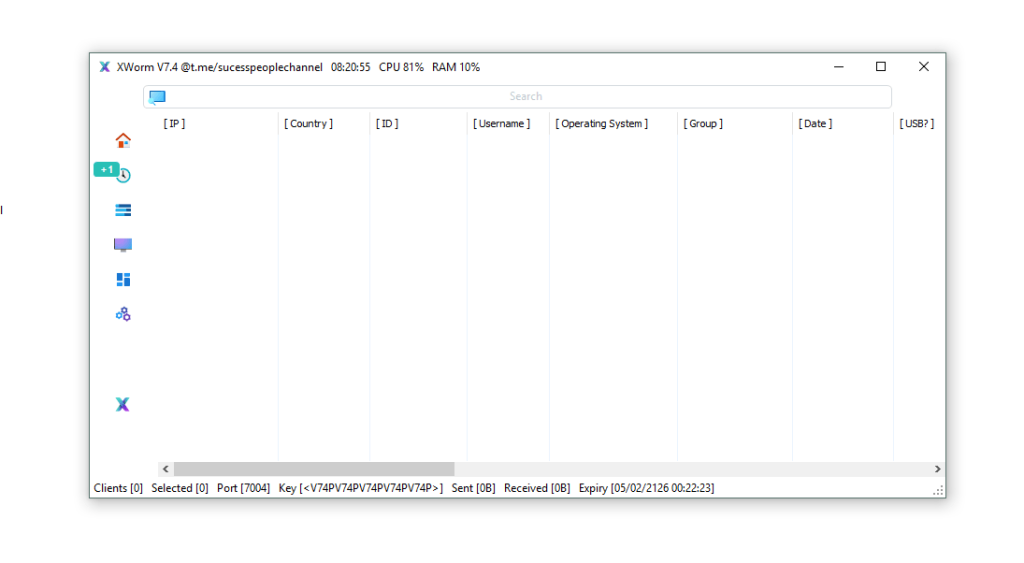
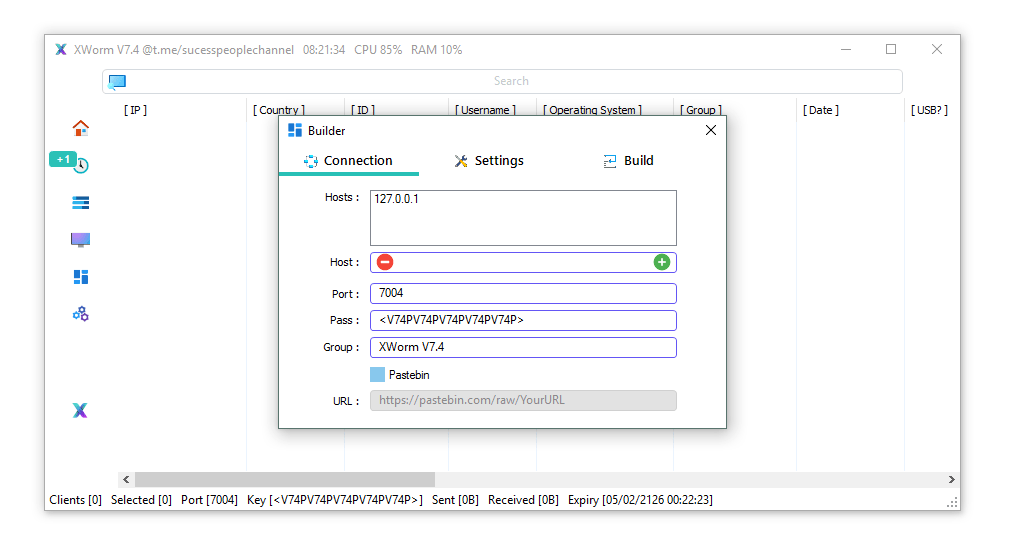
⚙️ Connection Settings
- 🌐 Host Configuration
👉 Defines where the infected device connects.
📌 Enables attacker communication with victims. - 🔌 Port Setup (e.g., 7004)
👉 Communication channel for data transfer. - 🔐 Connection Key
👉 Used to identify and control victims. - 📂 Victim Grouping
👉 Organizes infected systems for easier control.
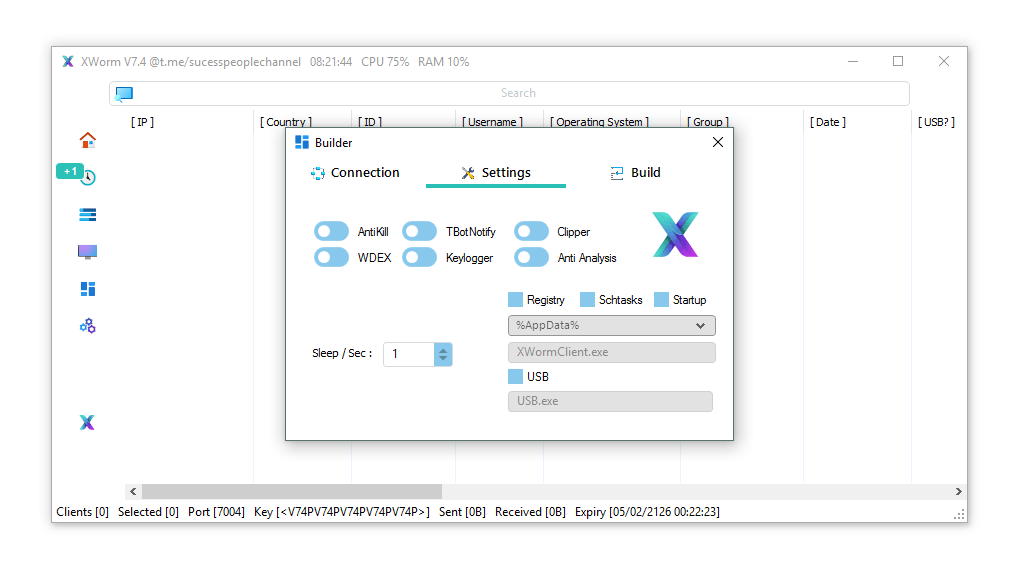
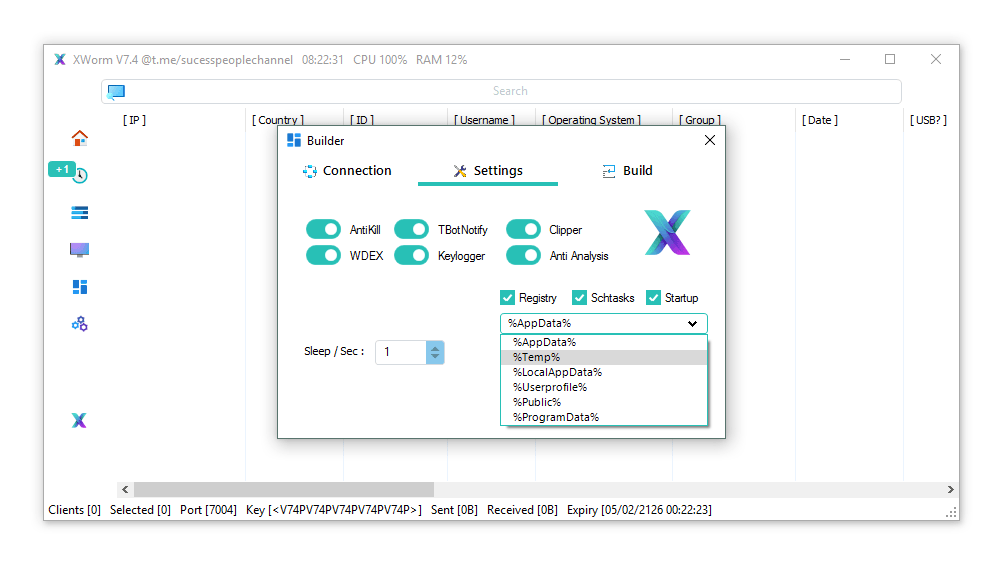
🔁 Persistence Mechanisms
- 🧾 Registry Auto-Start
👉 Runs malware on system startup. - ⏰ Scheduled Tasks
👉 Re-executes malware automatically. - 📁 Startup Folder Injection
👉 Ensures execution after login.
📍 Installation Locations
- 📂 %AppData% → hidden storage
- 📂 %Temp% → temporary but often ignored
- 📂 %LocalAppData% → blends with apps
- 📂 %ProgramData% → shared system data
- 📂 %UserProfile% → user-level persistence
- 🔌 USB Spread Feature
👉 Infects other devices via USB drives
🕵️♂️ Features Explained (Bullet + Detailed)
🎥 Surveillance & Monitoring
- 📷 Webcam Access
👉 Turns on camera remotely
📌 Used for spying and recording users - 🎤 Microphone Recording
👉 Captures surrounding audio
📌 Records private conversations - 🔊 System Audio Capture
👉 Records internal device sound
📌 Includes calls, media, and playback - ⌨️ Keylogger
👉 Records all keystrokes
📌 Steals passwords, OTPs, and messages - 🪟 Active Window Tracking
👉 Monitors active apps and tabs
📌 Detects sensitive activities - 📍 Location Tracking
👉 Estimates user location via IP
📌 Helps identify target region
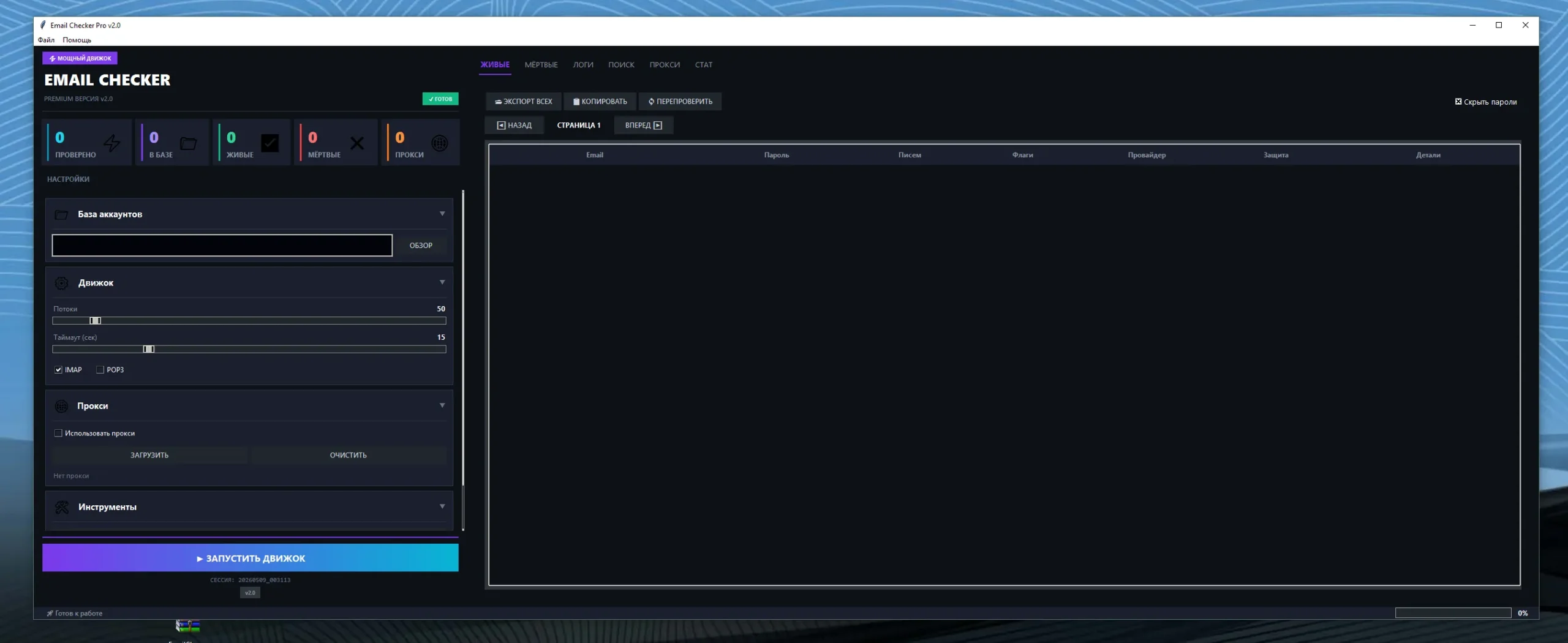
💰 Financial Theft
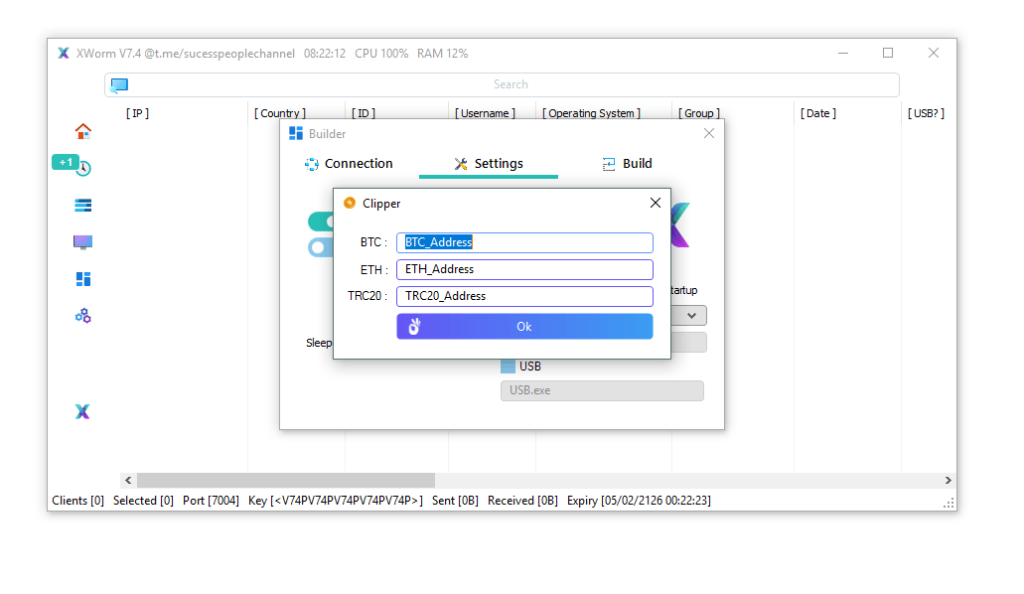
- 💸 Clipboard Hijacking (Clipper)
👉 Replaces crypto wallet addresses
📌 Redirects transactions to attacker
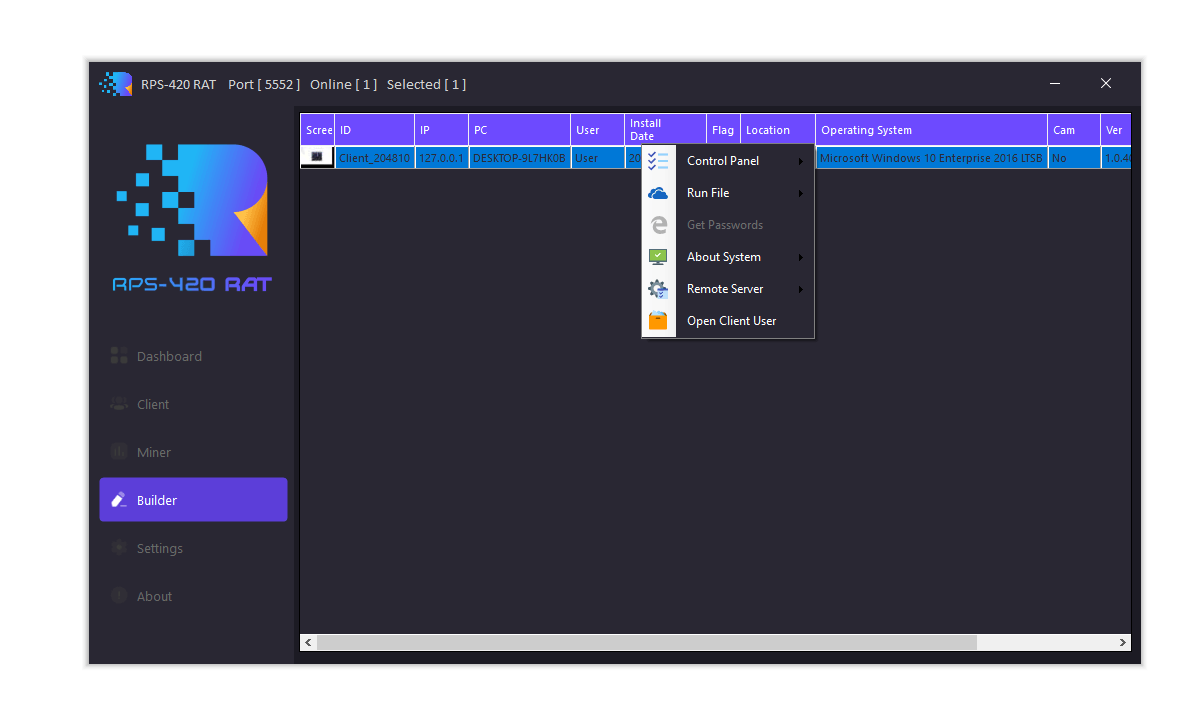
🖥️ System Control
- 📁 File Manager
👉 Full access to files
📌 View, delete, or steal data - ⚙️ Registry Editor
👉 Modify system settings
📌 Used for persistence and control - 🔄 Process Manager
👉 Control running programs
📌 Can disable antivirus - 🛎️ Service Manager
👉 Manage background services
📌 Maintains hidden activity - 🌐 DDoS Feature
👉 Uses system to attack websites
📌 Turns device into botnet - 🔐 UAC Bypass
👉 Skips security prompts
📌 Gains admin privileges - 🔌 Power Control
👉 Shutdown or restart system
📌 Used to disrupt or hide actions
🛡️ Anti-Detection Features
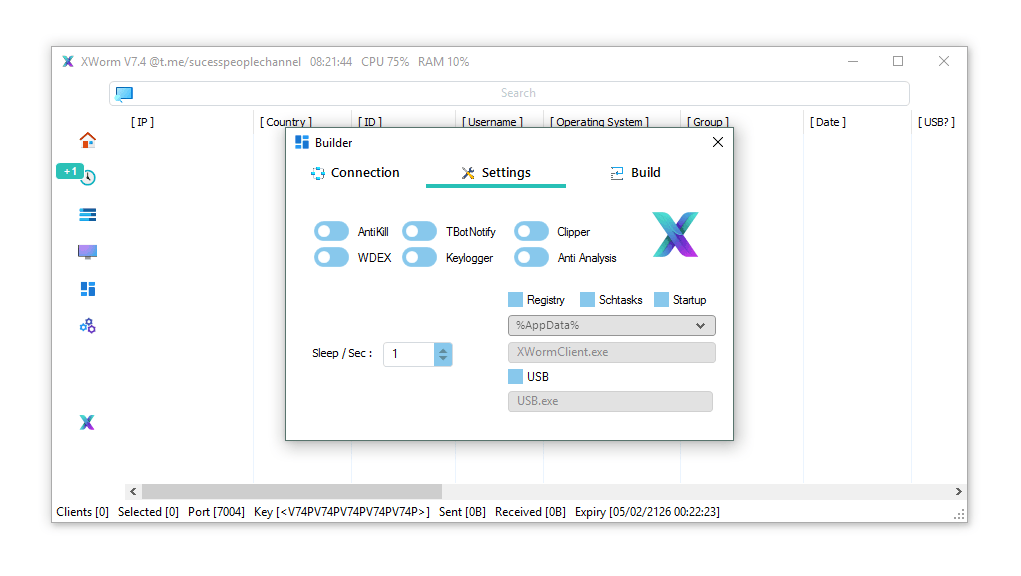
- 🧱 AntiKill Protection
👉 Prevents termination
📌 Hard to remove manually - 🧪 Anti-Analysis
👉 Detects sandbox/VM
📌 Avoids detection - 🛑 Antivirus Exclusion
👉 Bypasses security tools
📌 Runs undetected
🎯 Deployment & Social Engineering
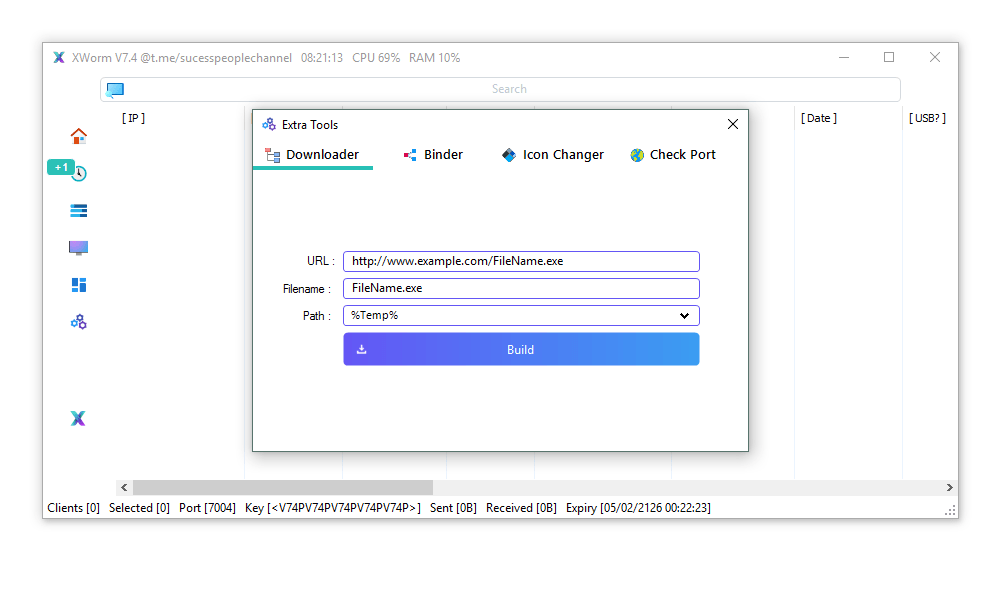
- 🧬 File Binder
👉 Combines malware with legit files
📌 Tricks users into installing - 🎭 Icon Changer
👉 Makes files look safe
📌 Increases trust - ⬇️ Downloader
👉 Installs more malware
📌 Expands attack - 💻 Built-in Compiler
👉 Generates malware easily
📌 No technical skill required
⚠️ Extra Risk of “Cracked” Versions
Using or downloading cracked malware introduces additional dangers:
- 🚨 Hidden backdoors (even attacker can be attacked)
- 🚨 Embedded spyware
- 🚨 No updates or security control
- 🚨 Legal consequences
👉 In many cases, the downloader becomes the victim.
🌍 Why XWorm V7.4 Cracked is More Dangerous
- 🚨 Freely available in underground sources
- 🚨 No license restrictions
- 🚨 Often modified with extra malicious code
- 🚨 Increases cybercrime accessibility
🛡️ Protection Tips
✔️ Avoid cracked software downloads
✔️ Do not open unknown files
✔️ Use trusted antivirus tools
✔️ Disable unknown USB devices
✔️ Keep system updated
Download XWorm V7.4 Cracked
📌 Conclusion
XWorm V7.4 Cracked is not just a cybersecurity threat—it is a high-risk malicious tool that can harm both victims and those who use it.
⚠️ The cracked nature makes it even more unpredictable and dangerous.
👉 Staying informed and avoiding such software is the best defense.
❓ FAQs
❓ What is XWorm V7.4 Cracked?
👉 It is an unauthorized modified version of a Remote Access Trojan without licensing restrictions.
❓ Is XWorm V7.4 Cracked safe to use?
❌ No, it is unsafe, illegal, and may contain hidden malware.
❓ How does it spread?
📥 Through malicious downloads, attachments, and USB devices.
❓ Can it harm the user who installs it?
⚠️ Yes, cracked versions may include hidden spyware or backdoors.
❓ How to stay safe?
🛡️ Avoid cracked software and use updated security tools.