🔍 Introduction to GHOST RAT 2026
Cyber threats are evolving rapidly in the modern digital landscape. One of the most dangerous malware categories used by cybercriminals is the Remote Access Trojan (RAT). These malicious programs allow attackers to remotely control infected devices without the victim’s knowledge.
GHOST RAT 2026 represents an advanced variant of remote administration malware capable of performing numerous malicious operations including system monitoring, command execution, data theft, and botnet management.
Because of its stealth capabilities and powerful remote control features, it has become a major concern for cybersecurity researchers and security professionals.
🧠 What is GHOST RAT Malware
A Remote Access Trojan (RAT) is a type of malware designed to allow unauthorized remote control of a computer system.
Once installed, the malware connects to a remote command server where attackers can send commands to the infected machine.
📌 Main Characteristics
✔ Remote device control
✔ Hidden background execution
✔ Persistent system access
✔ Data collection and monitoring
✔ Botnet integration
Unlike legitimate remote administration software, RAT malware operates secretly and often spreads through malicious downloads or phishing attacks.
📜 History of GHOST RAT
The original Ghost RAT malware family became widely known due to its involvement in cyber espionage campaigns. Over time, various modified versions have appeared, each introducing additional features and improved stealth mechanisms.
Modern variants like GHOST RAT 2026 include advanced networking capabilities and improved persistence techniques, making them more difficult to detect.
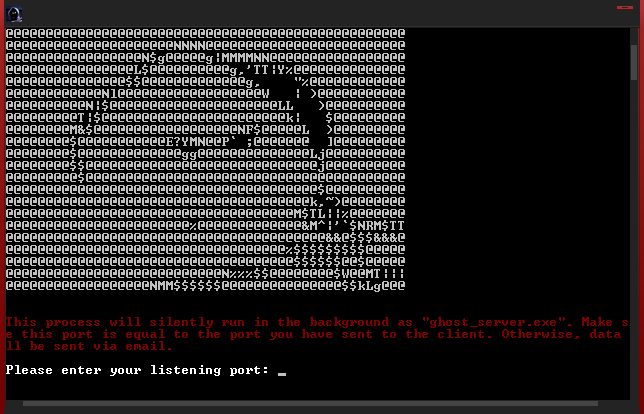
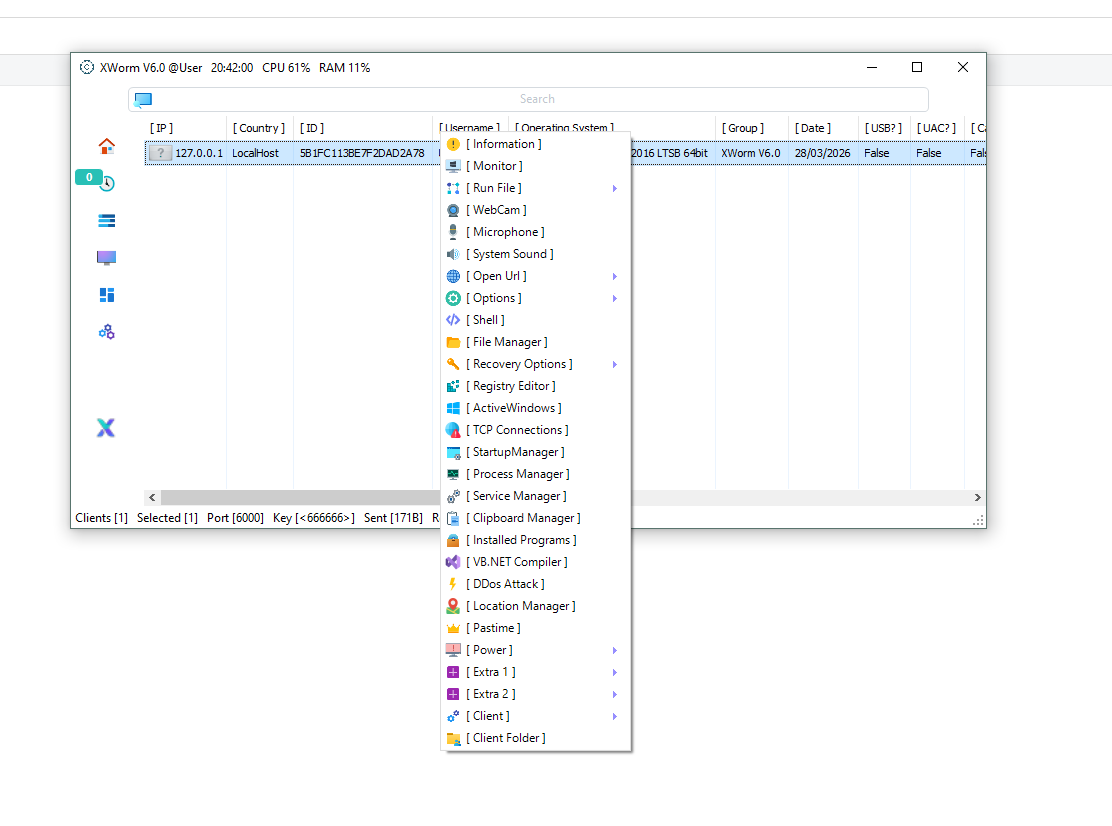
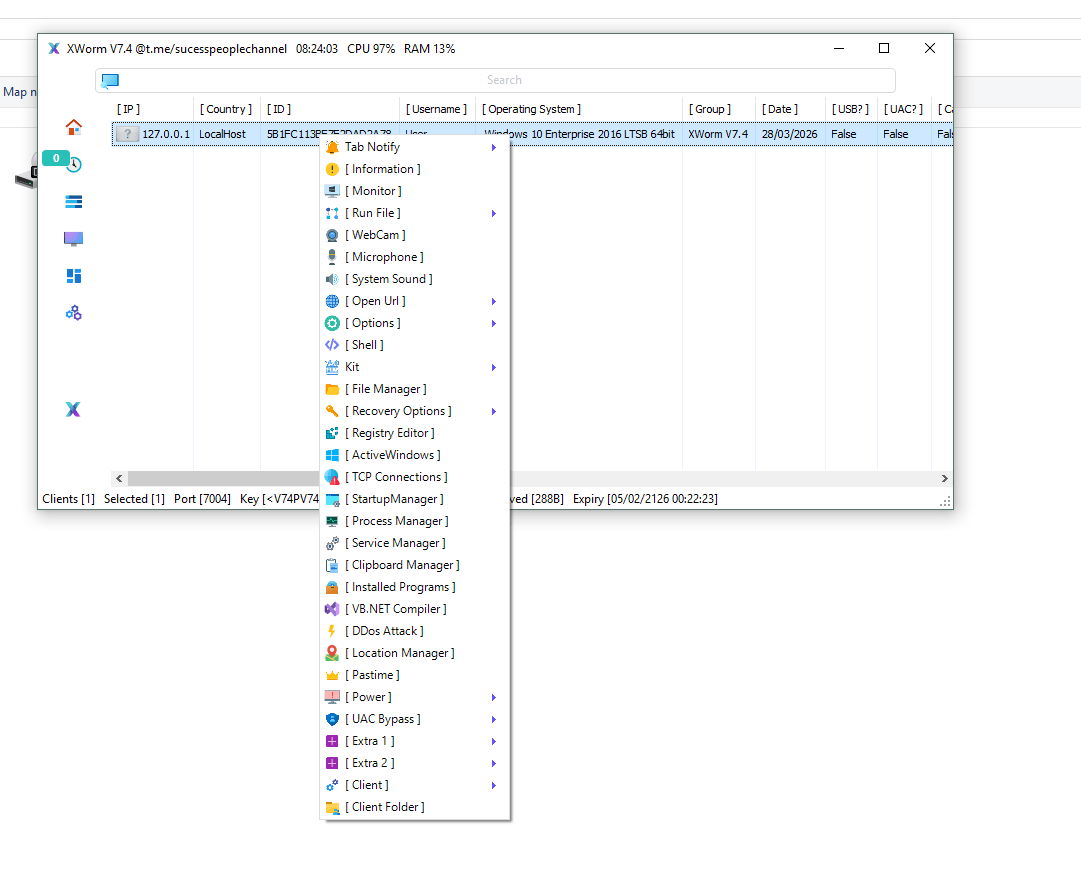
⚙️ Architecture of GHOST RAT 2026
The architecture of the malware typically includes two main components.
🖥️ Client Component
The client component runs on the infected machine.
Functions
🔹 Receive commands from attacker
🔹 Execute system instructions
🔹 Upload stolen data
🔹 Maintain connection to the command server
🌐 Command and Control Server
The command server acts as the central control panel used by attackers.
Server Capabilities
🔹 Manage infected machines
🔹 Send attack commands
🔹 Monitor compromised devices
🔹 Control botnet activity
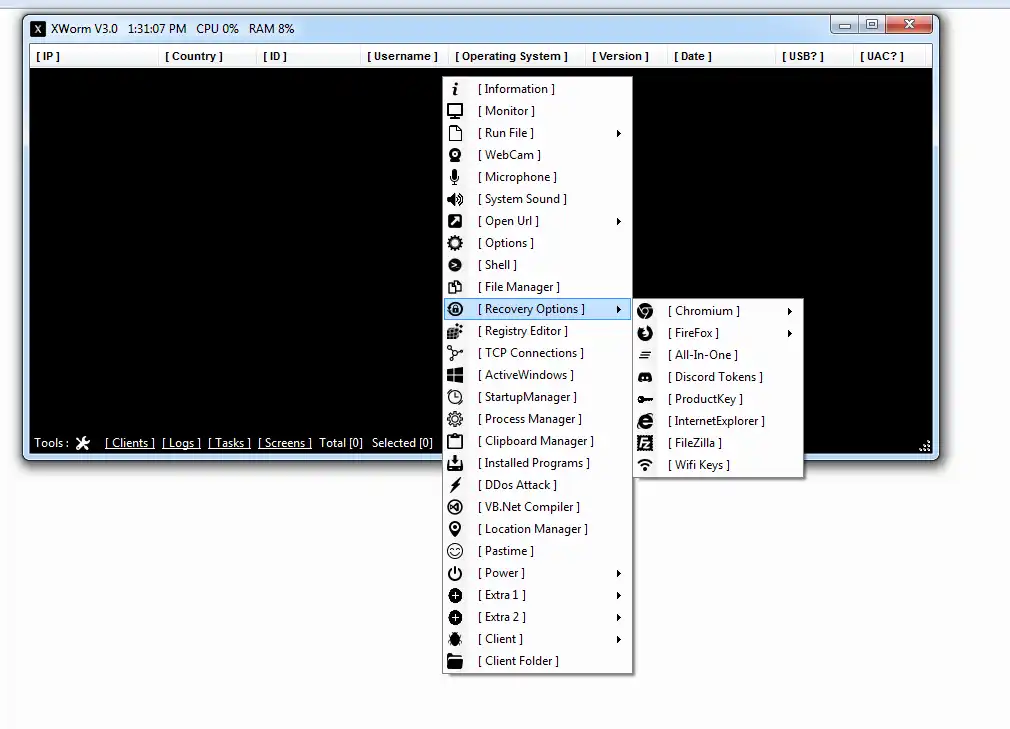
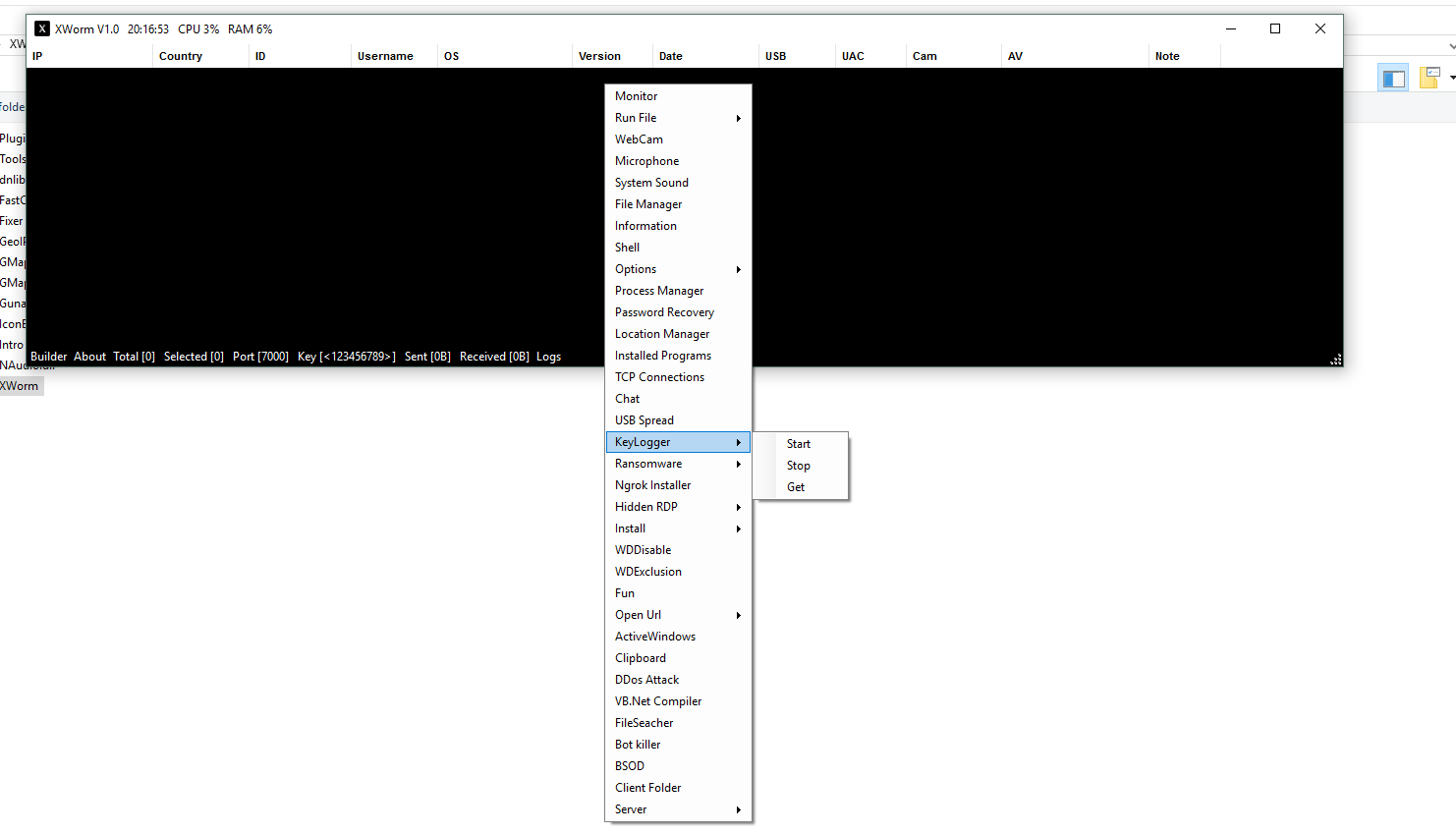
🚀 Key Features of GHOST RAT 2026
🎮 Remote System Control
Attackers can control the victim machine completely.
Capabilities include:
• Command execution
• Program launching
• Remote script execution
📂 File System Access
The malware enables attackers to manage files on infected systems.
Functions include:
• Upload files
• Download sensitive documents
• Delete files
• Execute applications
🕵️ Stealth Operation
The malware is designed to operate invisibly.
Stealth techniques include:
• Hidden processes
• Background execution
• Registry persistence
• Startup automation
🤖 Botnet Functionality
Infected machines can become part of a botnet network.
Botnets can be used for:
• Distributed cyber attacks
• Large-scale malware distribution
• Coordinated cybercrime campaigns
🧬 Advanced Capabilities of GHOST RAT 2026
⌨️ Keylogging
Records every keystroke typed by the victim.
This can expose:
• Login credentials
• Email passwords
• Banking details
📸 Screenshot Capture
Attackers can monitor the user’s screen activity in real time.
🎥 Webcam and Microphone Access
Some RAT variants allow attackers to activate webcams and microphones remotely.
🧾 System Information Harvesting
The malware collects device information such as:
• Operating system version
• Network configuration
• Installed applications
• Hardware specifications
🛠️ Infection Methods Used by GHOST RAT
The malware spreads through several attack vectors.
Common Infection Methods
⚠ Phishing email attachments
⚠ Fake software downloads
⚠ Malicious cracked applications
⚠ Trojanized installers
⚠ Exploit kits
🔄 Malware Attack Lifecycle
Typical RAT attacks follow a structured lifecycle.
1️⃣ Delivery
The malware reaches the victim through malicious files or downloads.
2️⃣ Installation
The malware installs itself and creates persistence mechanisms.
3️⃣ Command Server Connection
The infected system connects to the attacker’s command server.
4️⃣ Remote Control
Attackers can now monitor and control the system.
💾 Data Theft Capabilities
The malware can collect valuable information from infected systems.
Targeted Data
• Browser credentials
• Cryptocurrency wallets
• Email accounts
• Stored passwords
• Personal documents
🚨 Cybersecurity Risks
Remote access trojans present serious cybersecurity risks.
Potential Impacts
⚠ Financial fraud
⚠ Identity theft
⚠ Corporate espionage
⚠ Privacy invasion
⚠ Botnet-driven cyber attacks
🔍 Indicators of Compromise (IOCs)
Signs of a possible infection include:
• Suspicious network traffic
• Unknown background processes
• Unexpected system slowdown
• Disabled antivirus software
• Unauthorized remote connections
🛡️ Detection Techniques
Security analysts use several methods to detect RAT infections.
Detection Methods
🔎 Behavioral analysis
🔎 Network traffic monitoring
🔎 Malware sandbox analysis
🔎 Endpoint security monitoring
🔐 Prevention and Security Best Practices
Protecting systems from RAT malware requires proactive security measures.
Recommended Practices
✔ Install trusted antivirus software
✔ Keep operating systems updated
✔ Avoid downloading unknown files
✔ Use firewall protection
✔ Monitor network activity
🌐 Importance of RAT Malware Awareness
Cybersecurity awareness is one of the strongest defenses against malware attacks.
Users who understand phishing tactics and malicious downloads are less likely to fall victim to malware infections.
Organizations must also invest in security training and threat detection systems.
🔮 Future of Remote Access Trojans
As cybersecurity defenses improve, malware developers continuously evolve their techniques.
Future RAT malware may include:
• AI-driven attack automation
• stronger encryption
• advanced stealth techniques
• improved botnet infrastructure
Download GHOST RAT 2026
🧾 Conclusion
GHOST RAT 2026 highlights the growing sophistication of modern cyber threats. Its ability to provide attackers with remote system control makes it a dangerous malware tool in the cybersecurity landscape.
Understanding how such malware operates helps organizations and individuals strengthen their cybersecurity defenses and reduce the risk of compromise.
❓ Frequently Asked Questions (FAQs)
What is GHOST RAT 2026?
GHOST RAT 2026 is a remote access trojan that allows attackers to control infected computers remotely.
How does GHOST RAT infect devices?
It usually spreads through phishing emails, malicious downloads, or infected software installers.
What can attackers do with GHOST RAT?
Attackers can steal data, monitor activity, execute commands, and control the infected machine.
Is GHOST RAT dangerous?
Yes. It can lead to data theft, surveillance, and large-scale cyber attacks.
How can users protect their systems?
Users should install security software, avoid suspicious downloads, and keep systems updated.