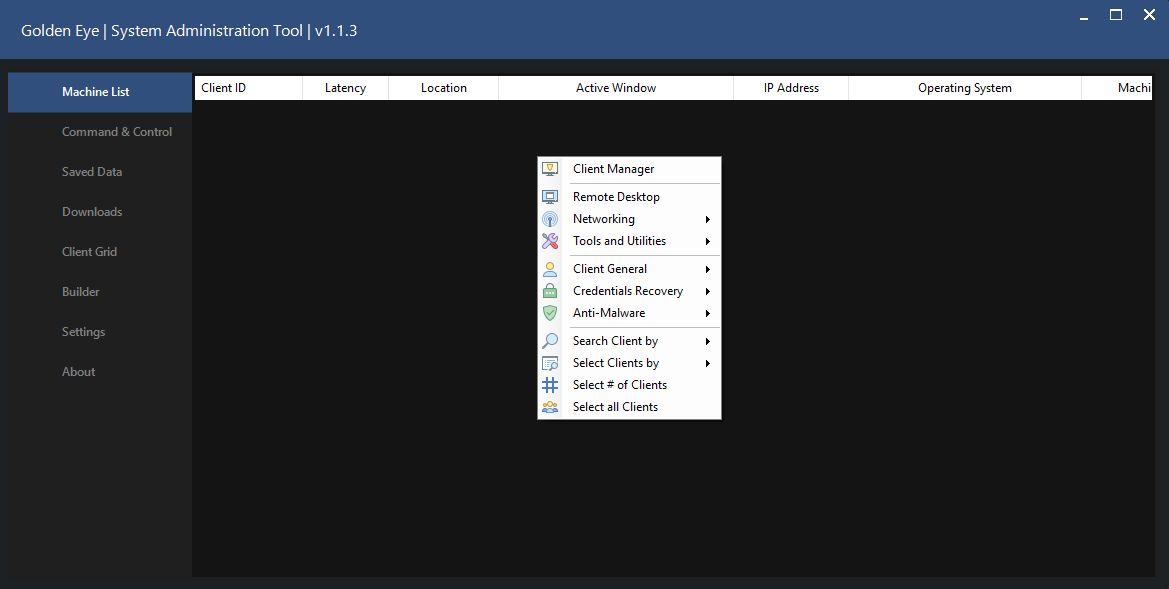
Golden Eye Rat with Tutorial 2023
In the ever-evolving landscape of cyberspace, the emergence of sophisticated malware has become an unfortunate reality. Among these digital threats, the GoldenEye Rat stands out as a particularly insidious and potent form of malicious software. As a remote access trojan (RAT), GoldenEye exhibits advanced capabilities, allowing unauthorized users to gain control over compromised systems and steal sensitive information. This essay delves into the characteristics, methods of propagation, and potential impacts of the GoldenEye Rat, shedding light on the evolving nature of cyber threats in the contemporary digital era.
Understanding the Golden Eye Rat with Tutorial 2023:
The GoldenEye Rat, also known as “GoldenEye” or “Eye of the Hydra,” is a type of malware designed to facilitate unauthorized remote access to a victim’s computer system. Like many other RATs, GoldenEye is typically deployed with the aim of surveillance, data exfiltration, and, in some cases, the execution of malicious commands. What sets GoldenEye apart is its high level of sophistication, enabling attackers to carry out targeted and stealthy cyber-espionage activities.
Propagation Methods Golden Eye Rat with Tutorial 2023:
The distribution of GoldenEye often relies on deceptive social engineering tactics. Common vectors of infection include phishing emails, malicious attachments, and compromised websites. The malware may be concealed within seemingly innocuous files or links, exploiting the unsuspecting nature of users to gain a foothold on their systems. Once a user falls victim to these tactics and inadvertently installs the malware, GoldenEye establishes a connection to a remote server, allowing attackers to exert control over the infected system.
Capabilities and Functionality:
GoldenEye boasts a range of capabilities that make it a formidable threat in the realm of cyber attacks. Some of its key functionalities include:
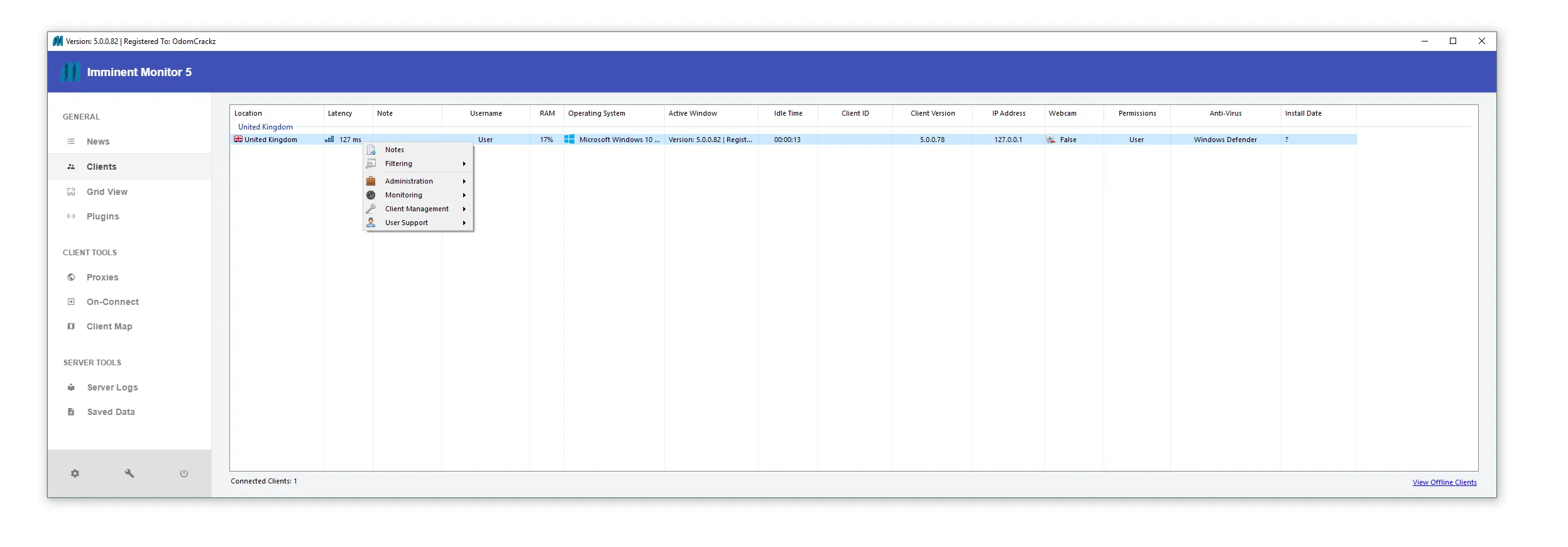
- Remote Access and Control: GoldenEye enables attackers to remotely access and control compromised systems, providing them with the ability to manipulate files, execute commands, and monitor user activities.
- Data Exfiltration: The malware is equipped with tools to steal sensitive information, including login credentials, financial data, and personal documents. This poses a significant risk to both individuals and organizations.
- Persistence: GoldenEye is adept at maintaining persistence on infected systems, ensuring that it can continue to operate undetected over extended periods. This characteristic makes it challenging for security measures to identify and eliminate the threat promptly.
Potential Impacts:
The GoldenEye Rat poses severe risks to individuals, businesses, and even government entities. The potential impacts include:
- Data Breaches: The malware’s ability to exfiltrate sensitive information may lead to data breaches, compromising the privacy and security of individuals and organizations.
- Financial Losses: GoldenEye can be utilized for financial crimes, such as unauthorized transactions and identity theft, resulting in substantial financial losses for victims.
- Compromised Infrastructure: Organizations may suffer from compromised infrastructure and disruptions to their operations, leading to a loss of productivity and potentially tarnishing their reputation.
Features:
Advanced INFO
File Manager
Remote Chat
Execute file
File Searcher
Visit Website
on Join Commands
Advanced Setting
Show Task Bar
Hide Task BarTask Manager
Windows Manager
Start Up manager
Update Client
Reconnect Client
Discconect Client
Infor Gathering
Client Grid
System Functions
Eject Disk Tray
Close Disk Tray
Remote CMD
Hosts Editor
UNInstall Client
Recover Password
Recover Win
Shut Down PC
Restart PC
Log off PC
Enable disable CMD
Disable UAC
Message BOX
Keylogger
UAC Panel
Malware Cleanr
Proactive Clieaner
Client Search
Hibernate
Enable Disable Monitor
Enable Disable Regedit
Enable Disable Taskmgrand much More